NISTs New Post-Quantum Cryptography Standards: A Secure Future
Nist new post quantum cryptography standards – NIST’s new post-quantum cryptography standards are a critical step towards securing our digital world in the face of emerging quantum computing threats. As quantum computers become more powerful, they pose a serious risk to the cryptographic algorithms that protect our sensitive data, online transactions, and critical infrastructure.
NIST has taken the lead in developing and standardizing post-quantum cryptography, ensuring that our digital security remains robust in the quantum era.
This standardization process, which began in 2016, has been a collaborative effort involving leading cryptographers, researchers, and industry experts worldwide. The goal is to identify and select algorithms that are resistant to attacks by both classical and quantum computers. NIST has meticulously evaluated and analyzed numerous candidate algorithms, culminating in the selection of several promising options that are poised to become the new foundation for secure communication and data protection.
Introduction to NIST Post-Quantum Cryptography Standards: Nist New Post Quantum Cryptography Standards
The rise of quantum computers poses a significant threat to the security of our digital world. These powerful machines, capable of performing computations at an unprecedented scale, can break the cryptographic algorithms that currently secure our online communications, financial transactions, and sensitive data.
The National Institute of Standards and Technology (NIST) recognizes the urgency of this threat and has taken a leading role in developing new cryptographic standards that are resistant to attacks from quantum computers. These standards, known as post-quantum cryptography (PQC), are designed to ensure the continued security of our digital infrastructure in the face of this emerging technology.
NIST’s Role in Post-Quantum Cryptography
NIST’s involvement in PQC standardization is crucial because it provides a global framework for developing and adopting secure cryptographic algorithms. The organization’s expertise and rigorous evaluation process ensure that the chosen algorithms are robust, efficient, and widely implementable.
The NIST Post-Quantum Cryptography Standardization Process
NIST’s standardization process has been a multi-year effort, involving a series of phases to ensure the selection of the most secure and practical PQC algorithms. The process began in 2016 with a call for proposals from the research community.
Phases of the Standardization Process
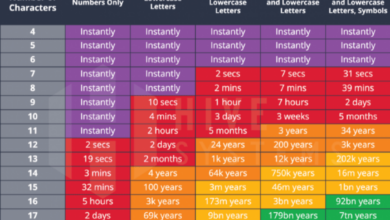
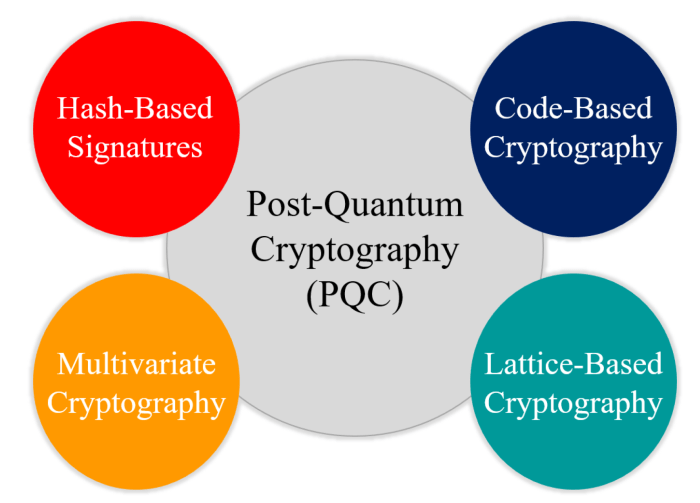
- Round 1 (2016-2017):NIST received 82 submissions for PQC algorithms. These algorithms were based on various mathematical problems, including lattice-based cryptography, code-based cryptography, multivariate cryptography, and hash-based cryptography.
- Round 2 (2017-2019):NIST narrowed down the initial submissions to 26 algorithms, based on their security, performance, and efficiency. The selected algorithms were subjected to rigorous analysis and testing by the cryptographic community.
- Round 3 (2019-2022):NIST further reduced the candidate algorithms to 7 finalists and 8 alternate candidates. These algorithms were subjected to extensive cryptanalysis and implementation efforts.
- Standardization (2022-present):NIST is currently in the process of standardizing the selected PQC algorithms. The first set of standards, based on the chosen algorithms, are expected to be released in 2024.
Key Algorithms and their Features
The NIST Post-Quantum Cryptography Standardization project has selected several algorithms for standardization, each offering unique security properties and performance characteristics. These algorithms represent a diverse range of mathematical approaches to achieve post-quantum security, aiming to withstand attacks from both classical and quantum computers.
Key Algorithms and their Features
The table below provides an overview of the key algorithms selected by NIST, highlighting their types, key features, strengths, and weaknesses.
| Algorithm Name | Algorithm Type | Key Features | Strengths | Weaknesses |
|---|---|---|---|---|
| CRYSTALS-Kyber | Key Encapsulation Mechanism (KEM) | – Based on the hardness of the module learning with errors (MLWE) problem.
|
– Fast encryption and decryption.
|
– Moderate key size for signatures.
|
| CRYSTALS-Dilithium | Digital Signature Algorithm | – Based on the hardness of the module learning with errors (MLWE) problem.
|
– Strong security against known quantum attacks.
|
– Slightly larger key sizes than some other algorithms.
|
| Falcon | Digital Signature Algorithm | – Based on the hardness of the shortest vector problem (SVP) on lattices.
|
– Very small signature sizes.
|
– Key sizes are larger than other algorithms.
|
| SPHINCS+ | Digital Signature Algorithm | – Based on the hardness of the hash-based signature (HBS) problem.
|
– Extremely high security against known quantum attacks.
|
– Larger signature sizes than other algorithms.
|
| SIKE | Key Encapsulation Mechanism (KEM) | – Based on the hardness of the supersingular isogeny Diffie-Hellman (SIDH) problem.
|
– Small key sizes.
|
– Requires specialized mathematical tools for implementation.
|
Underlying Mathematical Principles
The NIST-selected algorithms rely on various mathematical problems that are believed to be difficult for both classical and quantum computers to solve. These problems are often based on advanced mathematical concepts such as:
Lattice-based cryptography
CRYSTALS-Kyber and CRYSTALS-Dilithium rely on the hardness of finding short vectors in high-dimensional lattices. This problem is believed to be difficult for both classical and quantum computers.
The NIST’s new post-quantum cryptography standards are a big deal, especially as we move towards a future where quantum computers could potentially break current encryption methods. Implementing these new standards requires careful planning and a robust CI/CD pipeline. There are many options out there, and you might find yourself wondering about the differences between tools like bamboo vs circleci ci cd.
Ultimately, the choice depends on your specific needs and priorities, but it’s crucial to ensure that your chosen solution can handle the complexities of post-quantum cryptography.
Hash-based cryptography
SPHINCS+ leverages the difficulty of finding collisions in cryptographic hash functions. This approach is inherently resistant to quantum attacks.
Code-based cryptography
This category includes algorithms that rely on the hardness of decoding random linear codes. While code-based cryptography has been around for a while, it’s still being explored for post-quantum applications.
Isogeny-based cryptography
SIKE leverages the difficulty of computing isogenies between supersingular elliptic curves. This approach offers high security and small key sizes.
Security Level and Performance
The NIST Post-Quantum Cryptography Standardization project aims to provide different security levels for various applications. The security level is determined by the difficulty of breaking the underlying mathematical problem. For instance, a higher security level would require more computational resources to break the algorithm.The performance of each algorithm is evaluated based on factors such as key size, signature size, encryption/decryption speed, and computational requirements.
Algorithms like CRYSTALS-Kyber and CRYSTALS-Dilithium offer good performance and relatively small key sizes, making them suitable for a wide range of applications. However, algorithms like SPHINCS+ and Falcon may require more computational resources, leading to longer processing times.The NIST project continues to evaluate and refine these algorithms to ensure their security and performance meet the needs of different applications.
As the field of quantum computing evolves, the NIST standards will likely be updated to reflect the latest advancements and security considerations.
Implementation and Deployment Considerations
The transition to post-quantum cryptography (PQC) is a significant undertaking that requires careful planning and execution. Implementing PQC in existing systems presents both challenges and opportunities. The success of this transition depends on a well-defined strategy that addresses key factors, such as algorithm selection, migration processes, and security considerations.
Challenges and Opportunities
Implementing PQC in existing systems presents several challenges and opportunities. * Interoperability: PQC algorithms are still in their early stages of development and standardization, which can lead to interoperability issues between different implementations. Ensuring compatibility between different platforms and applications is crucial for seamless integration.
Performance
PQC algorithms are generally more computationally intensive than traditional algorithms, which can impact performance, especially on resource-constrained devices. Optimizing implementations and exploring hardware acceleration options are essential to mitigate these performance challenges.
Migration
Migrating from existing cryptographic algorithms to PQC alternatives requires careful planning and execution to minimize disruption to existing systems. This involves assessing the impact of the migration on different applications and developing a phased approach to ensure a smooth transition.
Security
PQC algorithms are designed to be resistant to attacks from quantum computers, but it is essential to implement them securely to prevent other types of attacks. Best practices for key management, secure coding, and vulnerability testing are crucial to ensure the overall security of PQC deployments.
NIST’s new post-quantum cryptography standards are a big deal, ushering in a new era of security that’s resistant to attacks from quantum computers. While you’re securing your digital future, why not grab yourself an iPhone 14, an Apple Watch SE, and an iPad in this epic Verizon deal grab yourself an iphone 14 plus an apple watch se and an ipad in this epic verizon deal ?
With these devices, you’ll be ready to experience the latest in technology, all while knowing your data is protected by the most advanced cryptography available.
Key Factors to Consider When Migrating to PQC
Several key factors must be considered when migrating from current cryptographic algorithms to PQC alternatives.* Algorithm Selection: Choosing the appropriate PQC algorithm is critical for ensuring security and performance. The selection process should consider factors such as the specific application requirements, the security level required, and the performance characteristics of different algorithms.
Migration Strategy
A well-defined migration strategy is essential for minimizing disruption to existing systems. This strategy should Artikel the steps involved in the migration, the timeline for implementation, and the resources required. A phased approach, starting with low-impact applications and gradually migrating to more critical systems, can help reduce the risk of disruptions.
Testing and Validation
Thorough testing and validation are essential to ensure that PQC implementations are secure and perform as expected. This involves conducting rigorous security audits, penetration testing, and performance evaluations to identify and address potential vulnerabilities.
Best Practices for Secure Integration
Several best practices can help ensure the secure integration of PQC algorithms into different applications and platforms.* Secure Key Management: Implementing robust key management practices is crucial for protecting PQC keys from unauthorized access. This includes using strong key generation methods, secure key storage, and secure key distribution protocols.
Secure Coding Practices
Following secure coding practices is essential to prevent vulnerabilities in PQC implementations. This involves using secure programming languages, avoiding common coding errors, and conducting regular code reviews.
Vulnerability Testing
Regular vulnerability testing is essential to identify and address potential weaknesses in PQC implementations. This involves conducting penetration testing, code audits, and other security assessments to ensure the overall security of PQC deployments.
Impact on Existing Systems and Applications

The transition to post-quantum cryptography (PQC) will inevitably impact existing systems and applications across various sectors. This shift is necessary to ensure the continued security of digital information in the face of the potential threat posed by quantum computers.
Impact on Different Sectors
The adoption of PQC will have significant implications for different sectors, including finance, healthcare, and government.
- Finance:Financial institutions heavily rely on cryptography for secure transactions, data storage, and communication. The transition to PQC will necessitate the upgrade of existing systems and protocols to ensure the continued integrity and confidentiality of financial data. This will involve updating encryption algorithms, digital signatures, and key management systems.
- Healthcare:Healthcare organizations handle sensitive patient data, including medical records, diagnoses, and treatment plans. The adoption of PQC will be crucial to protect this data from potential breaches by quantum computers. Healthcare systems will need to implement PQC algorithms in their electronic health records (EHR) systems, secure communication networks, and data storage solutions.
- Government:Governments rely on cryptography for secure communications, data storage, and critical infrastructure protection. The transition to PQC will be a critical step in ensuring the continued security of government operations and national security. This will involve updating encryption protocols, digital signatures, and authentication mechanisms used for government services, classified information, and critical infrastructure control systems.
Migration Strategies for Different Application Domains
The migration to PQC will require careful planning and execution to minimize disruption to existing systems and applications. Different application domains will require tailored migration strategies based on their specific needs and constraints.
| Application Domain | Migration Strategy | Considerations |
|---|---|---|
| Financial Transactions | Phased implementation, starting with non-critical applications and gradually migrating to critical systems. | Compliance with industry standards, regulatory requirements, and potential impact on existing systems and protocols. |
| Healthcare Records | Prioritization of sensitive data, ensuring the integrity and confidentiality of patient information. | Compliance with HIPAA regulations, impact on existing EHR systems, and potential need for data migration and re-encryption. |
| Government Services | Strategic approach to prioritize critical infrastructure and national security applications. | Compliance with government security standards, impact on existing systems and protocols, and potential need for training and support for government personnel. |
Future Directions and Research Areas
The field of post-quantum cryptography is constantly evolving, with ongoing research efforts pushing the boundaries of what is possible. Researchers are exploring new algorithms and techniques to ensure the security of our digital systems in the face of quantum computing advancements.
This section delves into key research areas, including code-based and lattice-based cryptography, and explores the potential of emerging technologies like quantum-resistant key exchange protocols and digital signatures.
Code-Based Cryptography
Code-based cryptography relies on the difficulty of decoding random linear codes, a problem that is believed to be intractable even for quantum computers. Research in this area focuses on improving the efficiency and performance of code-based cryptosystems, as well as exploring new code families and decoding algorithms.
“Code-based cryptography offers a promising alternative to traditional public-key cryptosystems, with the potential to withstand quantum attacks.”
Lattice-Based Cryptography, Nist new post quantum cryptography standards
Lattice-based cryptography leverages the mathematical properties of lattices, which are sets of points in a multi-dimensional space. This approach offers a wide range of cryptographic primitives, including encryption, digital signatures, and key exchange protocols. Research in lattice-based cryptography focuses on developing more efficient and secure algorithms, as well as exploring new applications.
Quantum-Resistant Key Exchange Protocols
Quantum-resistant key exchange protocols allow two parties to establish a shared secret key without relying on the difficulty of factoring large numbers or solving the discrete logarithm problem, which are vulnerable to quantum attacks.
“Quantum-resistant key exchange protocols are essential for secure communication in a post-quantum world.”
Quantum-Safe Digital Signatures
Quantum-safe digital signatures provide verifiable authenticity and integrity of digital documents, even in the presence of quantum computers.
“Quantum-safe digital signatures are crucial for ensuring the trustworthiness of digital transactions and communications.”