Meduza Stealer Targets Browsers, Crypto Wallets, and Password Managers
Meduza stealer targets browser variants crypto wallets password managers – Meduza Stealer targets browser variants, crypto wallets, and password managers, making it a serious threat to online security. This sophisticated malware can steal sensitive information like login credentials, cryptocurrency holdings, and personal data. It operates by exploiting vulnerabilities in popular browsers, targeting specific crypto wallets, and compromising password managers, giving attackers access to a wealth of valuable data.
The consequences of a Meduza Stealer infection can be devastating, leading to financial losses, data breaches, reputational damage, and legal repercussions.
Understanding how Meduza Stealer works, its targets, and its methods of distribution is crucial for staying ahead of this threat. By implementing preventative measures, recognizing the signs of infection, and knowing how to respond effectively, individuals and organizations can protect themselves from this malicious software.
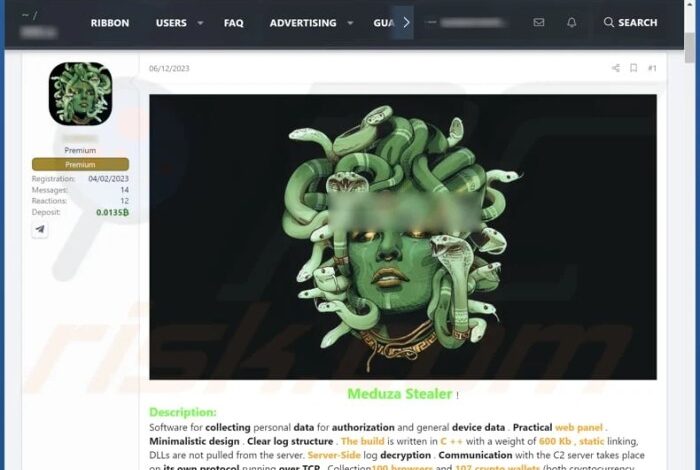
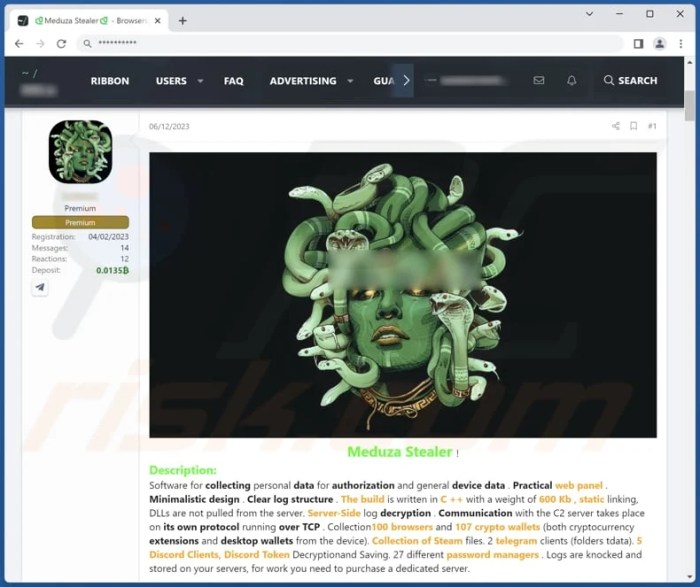
Meduza Stealer

Meduza Stealer is a malicious software program designed to steal sensitive information from compromised computers. It operates as an information stealer, targeting various data types, including browser credentials, cryptocurrency wallet data, and password manager entries.
The Meduza stealer is a serious threat, targeting browser variants, crypto wallets, and password managers. Protecting your data is crucial, and using a VPN can be a vital part of your security strategy. Check out this list of the best Chrome VPN extensions to enhance your online privacy and security, making it harder for malware like Meduza to steal your sensitive information.
History and Evolution
Meduza Stealer has been actively circulating since at least 2022. The malware has undergone several revisions and updates, with each iteration incorporating new features and enhancements to evade detection and increase its effectiveness. This evolution reflects the ongoing arms race between cybercriminals and security researchers, as attackers continuously seek to refine their tools to maximize their gains while defenders strive to stay ahead of emerging threats.
Targets
Meduza Stealer targets a wide range of sensitive data, including:
- Browser Credentials:It steals login information stored in popular web browsers, such as Google Chrome, Mozilla Firefox, and Microsoft Edge. This data includes usernames, passwords, and cookies, providing attackers with access to online accounts.
- Cryptocurrency Wallets:Meduza Stealer targets cryptocurrency wallets, aiming to steal private keys and other sensitive data associated with digital assets. This data grants attackers control over cryptocurrency holdings, allowing them to drain victims’ wallets.
- Password Managers:The malware also targets password managers, such as LastPass, KeePass, and 1Password, seeking to extract stored passwords and other confidential information. This data can be used to compromise multiple accounts across various online services.
Distribution and Infection
Meduza Stealer is typically distributed through various methods, including:
- Malicious Email Attachments:Attackers often disguise the malware as legitimate files, such as invoices, documents, or software updates, and send them through email. Victims who open these attachments unknowingly install the malware on their computers.
- Exploiting Software Vulnerabilities:Meduza Stealer can also be distributed by exploiting vulnerabilities in popular software applications, such as web browsers, operating systems, and office suites. These vulnerabilities allow attackers to gain unauthorized access to computers and install the malware without user interaction.
- Phishing Websites:Attackers create fake websites that mimic legitimate online services, such as banks, social media platforms, or e-commerce stores. Victims who visit these websites may be tricked into entering their login credentials, which are then stolen by the malware.
Target Platforms and Applications: Meduza Stealer Targets Browser Variants Crypto Wallets Password Managers
Meduza Stealer is a sophisticated malware designed to target various platforms and applications, aiming to steal sensitive information such as login credentials, financial data, and personal files. Its primary targets include popular web browsers, cryptocurrency wallets, and password managers.
The news about the Meduza stealer targeting browser variants, crypto wallets, and password managers is a serious reminder of the constant threat to our online security. It’s a stark contrast to the news that Apple’s intelligence AI features for iOS 18 will be in a beta test phase even after the full iOS 18 launch rolls out.
While it’s great to see Apple prioritizing user safety and feedback, the Meduza stealer threat highlights the need for constant vigilance in protecting our digital lives.
Browser Variants
Meduza Stealer targets a wide range of popular web browsers, exploiting vulnerabilities in their security mechanisms to gain access to stored data.
- Google Chrome:Exploits vulnerabilities in the browser’s autofill feature to steal saved passwords and credit card information.
- Mozilla Firefox:Targets Firefox’s password manager, attempting to exfiltrate stored credentials and sensitive data.
- Microsoft Edge:Exploits vulnerabilities in Edge’s autofill functionality to steal saved passwords and credit card details.
- Opera:Targets Opera’s built-in password manager, attempting to steal saved credentials and other sensitive information.
- Brave:Exploits vulnerabilities in Brave’s autofill feature to steal saved passwords and credit card information.
Cryptocurrency Wallets
Meduza Stealer specifically targets popular cryptocurrency wallets, aiming to steal funds stored within them.
- MetaMask:Exploits vulnerabilities in the MetaMask extension to steal private keys and cryptocurrency holdings.
- Coinbase Wallet:Targets Coinbase Wallet’s extension, attempting to steal seed phrases and cryptocurrency assets.
- Exodus:Exploits vulnerabilities in Exodus’s desktop application to steal cryptocurrency holdings.
- Trust Wallet:Targets Trust Wallet’s mobile application, attempting to steal cryptocurrency holdings and private keys.
Meduza Stealer employs various techniques to steal cryptocurrency funds, including:
- Keylogging:Records keystrokes, capturing passwords and seed phrases entered by users.
- Clipboard Monitoring:Monitors the clipboard for copied private keys and seed phrases.
- Web Injection:Injects malicious code into cryptocurrency wallet websites to steal credentials and funds.
Password Managers
Meduza Stealer also targets popular password managers, attempting to steal stored credentials and other sensitive information.
- LastPass:Exploits vulnerabilities in LastPass’s browser extension to steal stored passwords and other sensitive data.
- KeePass:Targets KeePass’s desktop application, attempting to steal stored passwords and other sensitive information.
- Dashlane:Exploits vulnerabilities in Dashlane’s browser extension to steal stored passwords and other sensitive data.
Meduza Stealer exfiltrates stolen data through various channels, including:
- Command and Control (C&C) servers:Sends stolen data to a remote server controlled by the attackers.
- File Transfer Protocol (FTP):Uploads stolen data to a remote server using FTP.
- Email:Sends stolen data to the attackers’ email address.
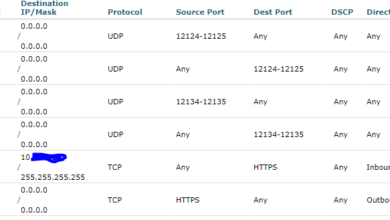
Technical Analysis of Meduza Stealer
Meduza Stealer, a sophisticated malware, exhibits a complex structure and utilizes various techniques to steal sensitive data from compromised systems. Its modular design and advanced functionalities enable it to effectively target and exfiltrate valuable information, posing a significant threat to users and organizations.
The Meduza stealer is a serious threat, targeting browser variants, crypto wallets, and password managers. It’s like a digital thief trying to unlock all your most valuable online assets. It’s almost like Apple deciding to stop selling its beloved “Apple II” computer, a product that was revolutionary in its time.
Why did Apple choose to abandon this iconic product? Just like Apple’s decision, the Meduza stealer aims to exploit vulnerabilities in our digital lives, making it crucial to be aware of the threats and take steps to protect ourselves.
Core Functionality and Modules
Meduza Stealer is designed with a modular architecture, allowing it to adapt and evolve to target different platforms and applications. This modularity facilitates the addition or removal of specific modules, making it difficult to detect and analyze. The core functionalities of Meduza Stealer include:
- Data Collection:Meduza Stealer gathers sensitive information from various sources, including web browsers, cryptocurrency wallets, and password managers. It utilizes techniques like browser history, cookie, and credential extraction to collect user data.
- Data Exfiltration:Once data is collected, Meduza Stealer uses different methods to exfiltrate it to the threat actor’s control server. Common techniques include uploading data to a remote server, sending it via email, or using a custom protocol for covert communication.
- Persistence:Meduza Stealer employs various persistence mechanisms to ensure its survival on the infected system. These techniques include creating registry entries, modifying system files, or injecting itself into legitimate processes, making it difficult to remove.
- Anti-Detection:To evade detection by security software, Meduza Stealer utilizes obfuscation techniques, such as code encryption, string encoding, and dynamic code generation. This makes it challenging for security researchers to analyze and understand its functionality.
Data Collection Methods
Meduza Stealer employs a variety of methods to collect data from infected systems, targeting specific applications and data sources. These methods include:
- Browser Data:Meduza Stealer can extract browser history, cookies, saved passwords, and credit card details from popular browsers like Chrome, Firefox, and Edge. It utilizes techniques like browser extension injection and web storage manipulation to gain access to this sensitive information.
- Cryptocurrency Wallet Data:Meduza Stealer targets cryptocurrency wallets like MetaMask, Exodus, and Electrum, attempting to steal private keys and seed phrases. It uses techniques like process injection and memory scanning to access and exfiltrate this sensitive information.
- Password Manager Data:Meduza Stealer can steal login credentials, passwords, and other sensitive information stored in password managers like LastPass, KeePass, and 1Password. It utilizes techniques like process injection and memory manipulation to gain access to these stored credentials.
- System Information:Meduza Stealer collects system information like operating system details, hardware specifications, and network configuration. This information is valuable to threat actors for profiling infected systems and planning further attacks.
Data Exfiltration Techniques
Once data is collected, Meduza Stealer utilizes various techniques to exfiltrate it to the threat actor’s control server. These techniques include:
- Upload to Remote Server:Meduza Stealer can upload the stolen data to a remote server controlled by the threat actor. This server can be located in a different country, making it difficult to track and identify the attacker.
- Email Exfiltration:Meduza Stealer can send the stolen data to the threat actor’s email address. This method is less sophisticated but can be effective in some cases.
- Custom Protocol:Meduza Stealer can use a custom protocol to communicate with the threat actor’s server. This protocol is designed to be covert and difficult to detect by security software.
- Tor Network:Meduza Stealer can use the Tor network to anonymize its communication with the threat actor’s server. This makes it even more difficult to trace the data exfiltration process.
Obfuscation and Anti-Detection Techniques
To evade detection by security software, Meduza Stealer employs various obfuscation and anti-detection techniques. These techniques include:
- Code Encryption:Meduza Stealer’s code can be encrypted to make it difficult for security researchers to analyze its functionality. This encryption can be implemented using various algorithms, making it challenging to decrypt and understand the code.
- String Encoding:Meduza Stealer can use string encoding techniques to obfuscate sensitive information, such as file paths, URLs, and API keys. This makes it difficult for security software to identify and analyze the data being accessed or transmitted.
- Dynamic Code Generation:Meduza Stealer can generate code dynamically at runtime, making it difficult for security software to detect and analyze its behavior. This dynamic code generation can be used to create custom malware modules or modify the malware’s functionality on the fly.
- Anti-VM Techniques:Meduza Stealer can detect virtual machines and sandboxes, making it difficult for security researchers to analyze its behavior in a controlled environment. This can involve checking for specific hardware or software configurations or using techniques like code injection to modify the execution environment.
Persistence Mechanisms
Meduza Stealer uses various persistence mechanisms to ensure its survival on the infected system. These techniques include:
- Registry Entries:Meduza Stealer can create registry entries to ensure that it runs automatically when the system starts. This allows the malware to persist even after the user restarts their computer.
- System File Modification:Meduza Stealer can modify system files to include its own code, ensuring that it is executed when the system starts or when specific processes are launched.
- Process Injection:Meduza Stealer can inject its code into legitimate processes, allowing it to run in the context of these processes and avoid detection by security software.
- Startup Scripts:Meduza Stealer can create startup scripts that run automatically when the system starts, allowing the malware to persist even after the user restarts their computer.
Impact and Consequences of Meduza Stealer Infections
Meduza Stealer, a potent malware designed to steal sensitive data from infected systems, poses a significant threat to individuals and organizations alike. Its ability to compromise various sensitive data types, including login credentials, financial information, and personal files, can have far-reaching consequences.
Financial Losses
Meduza Stealer’s primary objective is financial gain. Attackers leverage stolen credentials to access online accounts and financial resources. Victims may experience unauthorized transactions, account closures, and identity theft, leading to substantial financial losses. The malware’s ability to steal cryptocurrency wallet data exacerbates the financial risk, as stolen crypto assets can be difficult to recover.
Data Breaches
Meduza Stealer can compromise a wide range of sensitive data, including passwords, credit card information, and personal documents. These data breaches can have devastating consequences for individuals and organizations. Victims may experience identity theft, fraud, and reputational damage.
Reputational Damage and Legal Implications
Data breaches caused by Meduza Stealer can severely damage an organization’s reputation. Customers and stakeholders may lose trust in the organization’s ability to protect sensitive information. Legal repercussions can include fines, lawsuits, and regulatory scrutiny.
Real-World Incidents
Numerous real-world incidents highlight the devastating impact of Meduza Stealer infections. In one notable case, a large corporation suffered a major data breach, exposing millions of customer records, leading to significant financial losses and reputational damage. Another incident involved a university, where Meduza Stealer compromised student and faculty records, resulting in widespread identity theft and privacy concerns.
Prevention and Mitigation Strategies
Protecting yourself from malware like Meduza Stealer requires a proactive approach, combining common sense with robust security measures. It’s not just about avoiding suspicious links; it’s about creating a secure digital environment that makes it difficult for these threats to gain a foothold.
Importance of Software Updates and Security Patches
Software updates and security patches are critical to protecting your systems against Meduza Stealer and other malware. These updates often contain fixes for vulnerabilities that attackers exploit to gain access to your computer.
- Regularly update your operating system:Windows, macOS, and Linux all release regular security updates that patch vulnerabilities. Enable automatic updates to ensure your system is always up-to-date.
- Update your web browser:Web browsers like Chrome, Firefox, and Edge are frequently updated to address security vulnerabilities. Ensure your browser is set to automatically update.
- Update your applications:Applications like Adobe Reader, Microsoft Office, and Java are also potential targets for malware. Update these applications regularly to ensure they have the latest security patches.
Role of Antivirus Software and Other Security Tools
Antivirus software plays a crucial role in detecting and blocking Meduza Stealer and other malware. These programs use various techniques to identify and remove malicious software from your system.
- Real-time protection:Antivirus software constantly monitors your system for suspicious activity and blocks malware in real-time.
- Signature-based detection:Antivirus software uses a database of known malware signatures to identify and remove threats.
- Heuristic analysis:Antivirus software can analyze the behavior of programs to detect suspicious activity, even if the software isn’t yet known to be malicious.
- Firewall:A firewall acts as a barrier between your computer and the internet, blocking unauthorized access to your system.
- Anti-phishing software:Anti-phishing software helps protect you from phishing attacks, which can trick you into giving away sensitive information like passwords.
Best Practices for Managing Passwords and Protecting Sensitive Data, Meduza stealer targets browser variants crypto wallets password managers
Strong passwords and secure data management are essential for preventing Meduza Stealer from accessing your sensitive information.
- Use strong passwords:Strong passwords are at least 12 characters long, include a mix of uppercase and lowercase letters, numbers, and symbols, and are not easily guessable.
- Avoid using the same password for multiple accounts:If one account is compromised, attackers could use the same password to access your other accounts.
- Use a password manager:A password manager securely stores your passwords and generates strong, unique passwords for each of your accounts.
- Enable two-factor authentication (2FA):2FA adds an extra layer of security by requiring you to enter a code from your phone or email in addition to your password.
- Be cautious about what you download:Only download software from trusted sources and be wary of suspicious attachments in emails.
- Be careful about what you click on:Avoid clicking on links in emails or websites that you don’t recognize.
- Back up your data:Regularly back up your important data to an external hard drive or cloud storage service. This way, even if your computer is infected, you can restore your data from the backup.
Detection and Response
Detecting and responding to a Meduza Stealer infection is crucial to minimizing damage and restoring system security. Recognizing the signs of infection, understanding detection methods, and implementing effective removal and recovery strategies are essential steps in mitigating the risks associated with this malware.
Signs and Symptoms of a Meduza Stealer Infection
Recognizing the signs and symptoms of a Meduza Stealer infection is crucial for early detection and timely response. Here are some common indicators:
- Unusual system behavior, such as slow performance, frequent crashes, or unresponsive applications.
- Unexplained changes in system settings, including modified browser configurations, new startup programs, or unexpected firewall changes.
- Appearance of new, suspicious files or folders, especially those located in hidden system directories or with unusual names.
- Increased network activity, particularly unusual outbound connections to unknown or suspicious IP addresses.
- Missing or corrupted files, particularly sensitive data stored in browsers, wallets, or password managers.
- Compromised login credentials, such as usernames and passwords, being stolen from browsers or password managers.
- Unauthorized access to personal accounts, such as email, social media, or online banking.
- Unusual activity in your online accounts, such as suspicious login attempts or transactions.
Detection Methods
Several methods can be employed to detect a Meduza Stealer infection. These methods involve utilizing security tools, analyzing system behavior, and monitoring network activity:
- Antivirus and Anti-Malware Software:Up-to-date antivirus and anti-malware software can detect and remove Meduza Stealer. These tools regularly scan your system for known malicious files and suspicious activities.
- Security Monitoring Tools:Security monitoring tools, such as system event logs and network traffic analysis tools, can identify unusual activities or patterns that may indicate a Meduza Stealer infection.
- Behavioral Analysis:Observing changes in system behavior, such as unexpected performance issues, new startup programs, or unusual network connections, can provide clues about a potential infection.
- Network Monitoring:Analyzing network traffic for suspicious connections, such as outbound connections to known command-and-control servers, can help detect Meduza Stealer activity.
Removal and Recovery
Removing Meduza Stealer and recovering from an infection involves a multi-step process that aims to eliminate the malware, restore compromised data, and strengthen system security:
- Isolate the Infected System:Disconnect the infected system from the network to prevent further data exfiltration and spreading to other devices.
- Run a Full System Scan:Use a reputable antivirus or anti-malware software to perform a full system scan, identifying and removing all traces of Meduza Stealer.
- Clean Up Infected Files and Registry Entries:Manually remove any remaining infected files and registry entries identified by the scan.
- Reset Browser Settings:Reset the settings of all affected browsers to their default values, removing any malicious extensions or configurations.
- Change Passwords:Change the passwords for all compromised accounts, including email, social media, online banking, and any other accounts that may have been accessed by the malware.
- Restore Backups:If available, restore system and data backups to recover lost files and configurations.
- Update Software:Ensure all operating systems, applications, and security software are updated to the latest versions to patch vulnerabilities that Meduza Stealer might exploit.
- Monitor for Further Infections:Continuously monitor the system for any signs of reinfection or unusual activity.
Incident Response Planning and Coordination
Effective incident response planning and coordination are essential for mitigating the impact of a Meduza Stealer infection. A well-defined incident response plan Artikels the steps to be taken in case of a security breach, ensuring a coordinated and timely response:
- Develop a Comprehensive Plan:Establish a detailed incident response plan that Artikels the roles, responsibilities, and procedures for handling security incidents, including Meduza Stealer infections.
- Establish Communication Channels:Define clear communication channels and procedures for internal and external stakeholders, ensuring timely and accurate information sharing during an incident.
- Conduct Regular Drills:Conduct regular incident response drills to test the plan and ensure that all team members are familiar with their roles and responsibilities.
- Collaborate with Security Experts:Involve security experts and professionals, such as incident response teams or cybersecurity consultants, to assist in investigation, remediation, and recovery efforts.
- Document and Learn:Document the incident response process, including the actions taken, the lessons learned, and any recommendations for improvement.