Zero Trust Security: A Cheat Sheet
Zero trust security a cheat sheet – Zero Trust Security: A Cheat Sheet sets the stage for this enthralling narrative, offering readers a glimpse into a story that is rich in detail and brimming with originality from the outset. In today’s digital landscape, where cyber threats are constantly evolving, organizations are increasingly turning to Zero Trust security as a robust defense mechanism.
This modern approach to security abandons the traditional perimeter-based model, shifting the focus to verifying every access request, regardless of its origin.
This cheat sheet delves into the core concepts of Zero Trust, outlining its key components, implementation strategies, and the benefits it offers. We’ll explore how Zero Trust can be applied across various industries, including cloud environments, remote work, and the Internet of Things (IoT).
We’ll also discuss the future trends shaping the evolution of Zero Trust, including the impact of artificial intelligence and machine learning.
Zero Trust Security: Zero Trust Security A Cheat Sheet
The security landscape is constantly evolving, with traditional perimeter-based security models proving increasingly ineffective against sophisticated cyber threats. Zero Trust security emerges as a modern and robust approach, fundamentally changing the way organizations protect their digital assets.
The Core Principles of Zero Trust Security
Zero Trust security operates on the principle of “never trust, always verify.” It assumes that any user or device, both internal and external, cannot be inherently trusted and requires rigorous verification before accessing sensitive data or resources. This approach shifts the focus from securing the network perimeter to securing every access point and resource within the organization.
Shifting from Perimeter-Based Security to a Trust-Less Approach
Traditional perimeter-based security models relied on firewalls and other security measures to create a secure boundary around the network, assuming that anything inside the perimeter was safe. However, this model has become vulnerable to internal threats, lateral movement, and sophisticated attacks that bypass perimeter defenses.
Zero Trust challenges this assumption by eliminating the concept of a trusted network and treating every request as potentially malicious.
Real-World Applications of Zero Trust Security
Zero Trust principles can be applied across various organizational contexts, including:
- Remote Work Environments:As remote work becomes increasingly common, Zero Trust ensures secure access to corporate resources for employees working from home or other locations.
- Cloud Computing:Zero Trust helps secure access to cloud-based applications and data, ensuring that only authorized users and devices can access sensitive information.
- Internet of Things (IoT):With the proliferation of connected devices, Zero Trust helps secure IoT devices and their interactions with corporate networks, mitigating potential vulnerabilities.
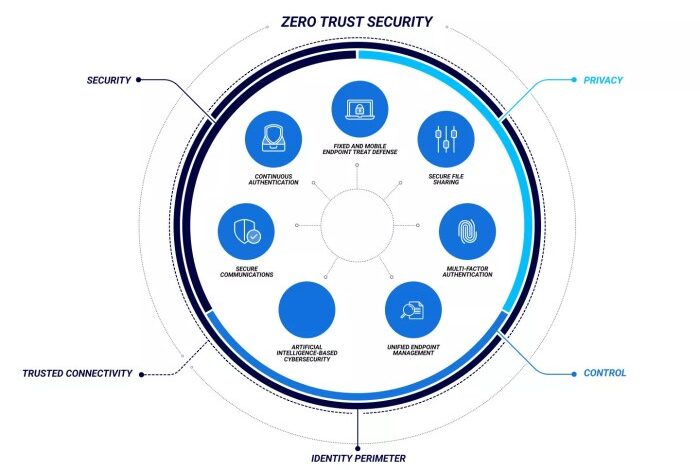
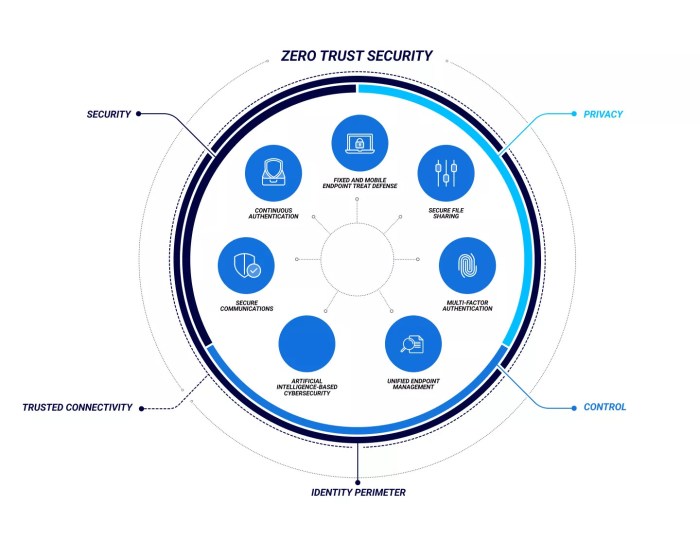
Key Components of Zero Trust
Zero Trust is a security framework that assumes no user or device can be trusted by default. It emphasizes strict access control, continuous monitoring, and data protection regardless of location. This approach shifts the focus from perimeter security to securing individual resources and users, regardless of their location.
Identity and Access Management (IAM)
IAM plays a crucial role in Zero Trust by establishing and enforcing granular access controls based on user identity, device context, and the sensitivity of the data being accessed.
Zero trust security is all about assuming nothing and verifying everything. It’s like a fortress with multiple layers of security, each one carefully scrutinized. But even the best defenses can be compromised if you don’t understand the people you’re working with.
That’s where social CRM comes in, helping you build relationships with your customers and employees and understand their needs and motivations. By incorporating social CRM into your zero trust strategy, you can create a more secure and collaborative environment for everyone.
- Multi-Factor Authentication (MFA):MFA adds an extra layer of security by requiring users to provide multiple forms of authentication, such as a password and a one-time code, before granting access to sensitive resources. This significantly reduces the risk of unauthorized access, even if a password is compromised.
- Least Privilege Access:This principle ensures that users are granted only the minimum permissions necessary to perform their assigned tasks. By limiting access to specific resources and functionalities, organizations can significantly reduce the potential impact of a security breach.
- Single Sign-On (SSO):SSO simplifies the authentication process by allowing users to log in once and access multiple applications and resources without having to re-authenticate. This improves user experience and reduces the risk of credential fatigue, which can lead to users choosing weak passwords or reusing passwords across multiple accounts.
Continuous Monitoring and Threat Detection
Zero Trust necessitates continuous monitoring and threat detection to identify and respond to potential threats in real-time.
- Security Information and Event Management (SIEM):SIEM solutions aggregate security data from various sources, such as firewalls, intrusion detection systems (IDS), and endpoint security agents. They analyze this data to detect anomalies and potential security threats, enabling security teams to respond proactively to incidents.
- User and Entity Behavior Analytics (UEBA):UEBA solutions monitor user and device activity patterns to identify deviations from normal behavior. This helps detect malicious activities, such as insider threats, data exfiltration, and unauthorized access attempts.
- Threat Intelligence:By leveraging threat intelligence feeds, organizations can gain insights into emerging threats, attack patterns, and known vulnerabilities. This information helps prioritize security measures, enhance detection capabilities, and respond effectively to incidents.
Implementation Strategies
Implementing Zero Trust security requires a strategic approach that considers the organization’s unique environment, goals, and resources. It’s not a one-size-fits-all solution and demands a phased rollout to ensure successful adoption.
Zero trust security is all about assuming no user or device can be trusted by default, requiring strict verification at every access point. This is a lot like how a database administrator (DBA), whose job you can read more about here , ensures the integrity and security of data within a database system.
Just as a DBA manages access and permissions, zero trust security implements granular controls to protect sensitive data, making it a vital strategy in today’s digital landscape.
Step-by-Step Guide
The following steps provide a comprehensive framework for implementing Zero Trust in an organization:
- Define Scope and Goals:Identify the specific areas and applications to be included in the Zero Trust initiative. Establish clear objectives, such as reducing risk, improving security posture, and enhancing compliance. For example, you might start with critical infrastructure, sensitive data, or high-value applications.
- Assess Current Security Posture:Conduct a thorough security assessment to identify existing vulnerabilities and gaps. This includes evaluating network infrastructure, applications, data storage, and user access controls. This step helps prioritize areas for improvement and identify potential challenges.
- Develop a Zero Trust Policy:Create a comprehensive policy that Artikels the principles, guidelines, and procedures for implementing Zero Trust. This policy should address key aspects such as authentication, authorization, data encryption, and device security. For example, it should specify how user access will be verified, what data access permissions will be granted, and what security measures will be enforced for devices accessing the network.
- Implement Zero Trust Controls:Deploy the necessary technologies and tools to enforce Zero Trust principles. This includes:
- Multi-factor Authentication (MFA):Require users to provide multiple forms of authentication before granting access, making it harder for attackers to gain unauthorized access. For example, a user might need to provide a password and a one-time code from a mobile app.
- Least Privilege Access:Grant users only the permissions they need to perform their job functions, minimizing the potential impact of a security breach. For example, a customer service representative might only have access to the customer database, not the entire company network.
- Data Encryption:Encrypt sensitive data both at rest and in transit to protect it from unauthorized access. For example, encrypting databases and network traffic prevents attackers from reading or modifying data even if they gain access to the system.
- Network Segmentation:Divide the network into smaller, isolated segments to limit the spread of attacks. For example, separating the production network from the development network can prevent an attacker from compromising both systems.
- Security Information and Event Management (SIEM):Use a SIEM system to monitor network activity, detect suspicious behavior, and respond to security incidents in real-time. This provides a centralized view of security events across the organization, allowing for faster detection and response.
- Test and Validate:Conduct regular security testing and penetration testing to evaluate the effectiveness of Zero Trust controls. This helps identify any vulnerabilities or weaknesses that need to be addressed. Testing can be performed by internal security teams or by third-party security experts.
- Monitor and Adapt:Continuously monitor the effectiveness of Zero Trust controls and make adjustments as needed. This includes analyzing security logs, reviewing security alerts, and responding to security incidents. Zero Trust is an ongoing process, not a one-time implementation, and requires ongoing monitoring and adaptation to stay ahead of evolving threats.
Zero trust security is all about assuming nothing and verifying everything. It’s a shift in mindset, and a great resource for getting started is a cheat sheet. But while we’re talking about security, I recently read an article about how the Control Center on iPhone has always been useful, but iOS 18 has made it even more exciting.
It’s a great example of how simple, accessible tools can enhance security. So, whether it’s your phone or your network, take a look at that zero trust cheat sheet and see how you can strengthen your defenses.
Essential Considerations
Several factors must be considered for successful Zero Trust implementation:
- Leadership Support:Secure strong leadership buy-in and commitment to support the Zero Trust initiative. This includes allocating necessary resources, providing guidance, and promoting a culture of security awareness.
- Employee Training:Train employees on Zero Trust principles and best practices. This includes educating them on secure password management, recognizing phishing attacks, and understanding the importance of reporting suspicious activity.
- Technology Integration:Ensure seamless integration of Zero Trust technologies with existing systems and infrastructure. This might involve upgrading existing systems, implementing new technologies, or configuring existing systems to support Zero Trust principles.
- Risk Assessment:Regularly assess the effectiveness of Zero Trust controls and identify areas for improvement. This includes analyzing security logs, reviewing security alerts, and conducting penetration testing.
- Scalability:Ensure the Zero Trust solution can scale to meet the evolving needs of the organization. This includes considering future growth, changes in business processes, and new technologies.
Deployment Models
Organizations can implement Zero Trust using various deployment models:
- Perimeter-Based:This model focuses on securing the network perimeter and relies on traditional security controls such as firewalls and intrusion detection systems. While this approach can be effective for some organizations, it is less effective against sophisticated attackers who can bypass perimeter defenses.
- Identity-Based:This model focuses on verifying user identities and granting access based on user roles and permissions. This approach can be more effective than perimeter-based security, but it requires a robust identity management system and strong authentication mechanisms.
- Data-Centric:This model focuses on protecting data regardless of where it is stored or accessed. This approach uses data encryption, access control lists, and other technologies to ensure data confidentiality and integrity.
- Software-Defined Perimeter (SDP):This model uses a software-defined perimeter to create a secure connection between users and applications. This approach can be highly effective in protecting sensitive data and applications, but it requires specialized software and expertise.
Benefits and Challenges
Zero Trust security is a modern approach to cybersecurity that has gained significant traction in recent years. It offers numerous benefits that can enhance an organization’s security posture, but its implementation also presents unique challenges. This section explores the key benefits and challenges associated with Zero Trust and provides practical best practices to overcome these hurdles.
Benefits of Zero Trust
Zero Trust offers several significant advantages for organizations, including:
- Enhanced Security Posture:By eliminating implicit trust, Zero Trust significantly reduces the attack surface and makes it more difficult for attackers to gain access to sensitive data. It prevents lateral movement within a network, limiting the impact of a successful breach.
- Improved Data Protection:Zero Trust principles enforce strong access controls and data encryption, ensuring that only authorized users can access sensitive information, regardless of their location or device. This helps safeguard data from unauthorized access and potential data breaches.
- Increased Compliance:Zero Trust aligns with industry regulations and compliance standards, such as GDPR, HIPAA, and PCI DSS, by providing robust security controls and audit trails. This helps organizations demonstrate compliance and mitigate potential legal and financial risks.
- Reduced Risk of Insider Threats:Zero Trust mitigates the risk of insider threats by implementing strict access controls and continuous monitoring, ensuring that employees only access the resources they need to perform their job duties. This helps prevent unauthorized data access and misuse.
- Improved Incident Response:In the event of a security breach, Zero Trust principles can help contain the damage by isolating compromised systems and preventing further lateral movement. This enables faster incident response and reduces the overall impact of the attack.
Challenges of Implementing Zero Trust
Implementing Zero Trust can be a complex and challenging process. Organizations need to overcome several hurdles to achieve successful adoption, including:
- Legacy Infrastructure:Many organizations still rely on legacy systems and applications that may not be compatible with Zero Trust principles. Upgrading or replacing these systems can be a significant investment and may require extensive planning and coordination.
- Complexity and Integration:Implementing Zero Trust requires a comprehensive approach that involves integrating various security technologies and tools. This can be a complex undertaking that requires specialized expertise and careful planning to ensure interoperability and seamless operation.
- User Adoption and Training:Zero Trust principles may require changes in user behavior, such as multi-factor authentication and frequent password resets. Organizations need to effectively communicate these changes to users and provide adequate training to ensure smooth adoption.
- Performance Impact:Implementing Zero Trust can potentially impact network performance due to increased authentication and authorization checks. Organizations need to carefully design and optimize their Zero Trust implementation to minimize any performance degradation.
- Cost and Resource Allocation:Implementing Zero Trust requires significant investments in technology, infrastructure, and personnel. Organizations need to carefully assess the costs and resource requirements to ensure a successful implementation.
Best Practices for Overcoming Challenges
Organizations can overcome the challenges of implementing Zero Trust by adopting best practices, including:
- Start Small and Scale Gradually:Instead of attempting to implement Zero Trust across the entire organization at once, organizations can start with a pilot project in a specific department or business unit. This allows them to test and refine their approach before scaling it to the rest of the organization.
- Prioritize High-Value Assets:Organizations should prioritize implementing Zero Trust principles for their most critical assets, such as sensitive data, critical applications, and infrastructure. This ensures that the most important resources are protected first.
- Invest in Training and Communication:Organizations need to invest in comprehensive training programs for users and IT staff to educate them about Zero Trust principles and how to use the new security tools and processes. Clear and consistent communication is essential to ensure user buy-in and smooth adoption.
- Partner with Experts:Organizations can partner with cybersecurity experts to assist with the implementation of Zero Trust. These experts can provide valuable guidance, technical expertise, and best practices to ensure a successful implementation.
- Continuously Monitor and Evaluate:Organizations should continuously monitor their Zero Trust implementation to identify any vulnerabilities or areas for improvement. Regular security assessments and audits can help ensure that the Zero Trust framework remains effective and meets evolving security threats.
Real-World Applications
Zero Trust is not just a theoretical concept; it’s a practical framework that can be implemented across various industries and scenarios to enhance security. Here, we explore some real-world applications of Zero Trust in different sectors, demonstrating its versatility and effectiveness.
Securing Cloud Environments, Zero trust security a cheat sheet
Cloud computing has revolutionized how businesses operate, but it also presents new security challenges. Zero Trust principles can be applied to secure cloud environments effectively.
- Data Encryption:All data stored in the cloud, regardless of location or access, is encrypted using robust algorithms, ensuring confidentiality even if unauthorized access occurs.
- Multi-Factor Authentication (MFA):MFA adds an extra layer of security by requiring users to provide multiple forms of authentication before granting access to sensitive cloud resources.
- Micro-segmentation:Dividing cloud infrastructure into smaller, isolated segments restricts access to specific resources, minimizing the impact of potential breaches.
- Continuous Monitoring and Threat Detection:Zero Trust emphasizes continuous monitoring of cloud environments for suspicious activities and potential threats, enabling prompt responses to security incidents.
Securing Remote Work
The rise of remote work has significantly increased the attack surface for organizations. Zero Trust principles are crucial for securing remote work environments.
- Endpoint Security:All devices used for remote work, whether company-owned or personal, must meet specific security standards, including up-to-date software, anti-malware protection, and strong passwords.
- Network Segmentation:Isolating remote worker devices from the organization’s internal network minimizes the risk of lateral movement by attackers.
- VPN and Secure Access:Remote workers should access company resources through secure VPN connections, enforcing strong authentication and encryption for data transmission.
- Data Loss Prevention (DLP):DLP solutions prevent sensitive data from leaving the organization’s control, even if it’s accessed by remote workers.
Securing IoT Devices
The Internet of Things (IoT) has created a vast network of interconnected devices, increasing the vulnerability to security threats. Zero Trust principles can be applied to secure IoT devices.
- Device Authentication:All IoT devices must be authenticated before connecting to the network, ensuring only authorized devices are granted access.
- Data Encryption:Data transmitted between IoT devices and the network should be encrypted to prevent eavesdropping or data interception.
- Secure Firmware Updates:Regular firmware updates for IoT devices are crucial to patch vulnerabilities and enhance security.
- Network Segmentation:Separating IoT devices from critical infrastructure or sensitive networks limits the potential impact of a breach.
Future Trends
Zero Trust security is a dynamic field that is constantly evolving to address emerging threats and leverage new technologies. As we move forward, several key trends will shape the future of Zero Trust, pushing the boundaries of security and creating new opportunities for organizations to protect their digital assets.
The Rise of AI and Machine Learning in Zero Trust
AI and machine learning are transforming the way organizations approach security. These technologies are playing a crucial role in enhancing Zero Trust security by automating threat detection, improving threat response, and personalizing security policies.
- Enhanced Threat Detection and Response:AI-powered security solutions can analyze vast amounts of data from various sources to identify suspicious activities and potential threats. Machine learning algorithms can learn from past attacks and adapt to new attack patterns, enabling organizations to detect and respond to threats more effectively.
- Automated Security Policy Enforcement:AI can automate the process of creating and enforcing security policies based on real-time threat intelligence and user behavior analysis. This helps organizations to maintain a dynamic and adaptive security posture, automatically adjusting policies to mitigate emerging threats.
- Personalized Security Experiences:AI can be used to tailor security policies to individual users and devices based on their roles, access privileges, and risk profiles. This personalized approach can enhance security without compromising user experience.
Zero Trust for the Cloud and Beyond
The increasing adoption of cloud computing and the rise of hybrid and multi-cloud environments have created new challenges for traditional security approaches. Zero Trust is becoming increasingly important in securing cloud-based resources and ensuring secure data access across multiple cloud platforms.
- Cloud Security Posture Management:Zero Trust principles are being integrated into cloud security posture management (CSPM) solutions to continuously monitor and assess cloud security configurations and identify vulnerabilities. This helps organizations ensure that their cloud deployments adhere to Zero Trust principles.
- Cloud Access Security Broker (CASB):CASBs are used to enforce Zero Trust principles for cloud applications, providing visibility and control over data access and usage. They help organizations enforce granular access policies, monitor user activity, and detect suspicious behavior in the cloud.
- Zero Trust for Multi-Cloud Environments:Zero Trust principles are becoming essential for securing multi-cloud environments, ensuring that data and applications are protected regardless of their location. This requires organizations to adopt a consistent Zero Trust approach across all cloud platforms.
The Convergence of Zero Trust and SASE
SASE (Secure Access Service Edge) is an emerging architectural framework that combines network security and wide-area networking (WAN) capabilities. The convergence of Zero Trust and SASE is creating a more holistic and integrated approach to security, extending Zero Trust principles to the network edge.
- Unified Security and Network Management:SASE platforms provide a centralized point of control for managing network access, security policies, and user authentication. This allows organizations to enforce Zero Trust principles across their entire network infrastructure, from the data center to the cloud and the edge.
- Improved User Experience:SASE architectures can optimize network performance and user experience by directing traffic through the most efficient path. This helps organizations ensure that users can access the resources they need securely and efficiently, regardless of their location.
- Enhanced Security Posture:SASE platforms integrate advanced security capabilities, such as next-generation firewalls, intrusion detection systems, and data loss prevention tools, to provide comprehensive protection against threats. This helps organizations to maintain a robust security posture and minimize their attack surface.
The Rise of Zero Trust for IoT and Edge Computing
The proliferation of Internet of Things (IoT) devices and the growth of edge computing are creating new security challenges. Zero Trust principles are becoming essential for securing these devices and ensuring secure data access at the edge.
- Secure Device Management:Zero Trust principles can be applied to manage and secure IoT devices, ensuring that only authorized devices are allowed to access the network and that their communication is secure. This helps organizations to mitigate the risks associated with compromised or malicious IoT devices.
- Edge Security:Zero Trust principles are being extended to the edge to secure data and applications at the point of collection and processing. This helps organizations to minimize the risk of data breaches and ensure that sensitive data is protected, even in remote locations.
- Data Privacy and Compliance:Zero Trust principles can help organizations to comply with data privacy regulations, such as GDPR and CCPA, by ensuring that data is accessed only by authorized individuals and that appropriate security measures are in place to protect sensitive information.