Massive Ransomware Operation Targets VMware ESXi
Massive ransomware operation targets VMware ESXi, a chilling headline that sent shockwaves through the tech world. This attack wasn’t just another cybercrime; it was a targeted assault on a critical infrastructure component used by countless organizations. The vulnerability exploited in this attack allowed hackers to gain access to sensitive data, potentially crippling businesses and causing widespread disruption.
This incident serves as a stark reminder of the ever-evolving threat landscape and the importance of robust cybersecurity measures.
The ransomware group behind this attack, known for their sophisticated tactics and relentless pursuit of lucrative targets, used a previously unknown vulnerability to infiltrate ESXi servers. This vulnerability, discovered and disclosed in [Insert Date], allowed attackers to gain unauthorized access and execute malicious code.
The scale of the attack was staggering, with [Insert Number] organizations and systems falling victim to the ransomware. The impact was felt across various sectors, from healthcare and finance to education and government, highlighting the widespread vulnerability of critical infrastructure to cyberattacks.
The ESXi Server Vulnerability
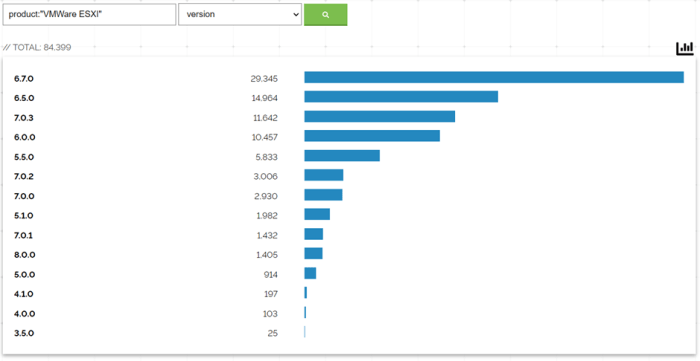
This recent ransomware attack targeted VMware ESXi servers, exploiting a critical vulnerability that allowed attackers to gain unauthorized access and encrypt data. The vulnerability, known as CVE-2021-21974, affected older versions of ESXi and allowed attackers to bypass authentication mechanisms, granting them full control over the server.
The recent massive ransomware operation targeting VMware ESXi servers highlights the importance of robust security measures. It’s crucial to stay informed about potential threats and implement proactive security strategies. For example, configuring notifications in Google Workspace apps, as described in this article , can help you quickly identify and respond to suspicious activity, minimizing the impact of a ransomware attack.
Technical Aspects of the Vulnerability
The vulnerability resided in the OpenSLP service, which is used for service discovery on ESXi servers. Attackers could exploit this service by sending specially crafted packets that bypassed authentication checks, allowing them to execute arbitrary code on the server. This code could then be used to install ransomware, steal data, or launch other malicious activities.
Timeline of the Vulnerability’s Discovery and Disclosure
- February 2021:VMware released a security advisory for CVE-2021-21974, urging users to update their ESXi servers to address the vulnerability.
- March 2023:Reports emerged of a massive ransomware operation targeting ESXi servers, exploiting the CVE-2021-21974 vulnerability. This attack targeted vulnerable servers that had not been patched, highlighting the importance of timely security updates.
The news about the massive ransomware operation targeting VMware ESXi servers is definitely a wake-up call for anyone running critical infrastructure. It’s a reminder that cybersecurity is paramount, especially as technology evolves. While I’m busy planning my upgrade to the iPhone 16 Pro, I’m also thinking about the essential accessories to make the most of it, like a new case and a wireless charger.
Check out this list of the 7 accessories I’m buying for my iPhone 16 Pro upgrade. But back to the ransomware attack, it’s a serious threat, and it’s important to be aware of the risks and take steps to protect your systems.
The Impact of the Attack
The ESXi server vulnerability exploited in this ransomware attack has had a significant impact on organizations worldwide. The scale of the attack, the types of data potentially compromised, and the potential financial and reputational damage are all major concerns.
The Scale of the Attack, Massive ransomware operation targets vmware esxi
The ransomware attack targeting ESXi servers affected a large number of organizations, with estimates ranging from hundreds to thousands. This widespread impact highlights the vulnerability of critical infrastructure to cyberattacks. The attack was particularly concerning because it targeted a core component of many organizations’ IT infrastructure, potentially disrupting essential operations and services.
Types of Data Potentially Compromised
The attack had the potential to compromise a wide range of sensitive data, including:
- Sensitive business information:This could include financial records, intellectual property, trade secrets, and customer data.
- Customer data:This could include personally identifiable information (PII), such as names, addresses, phone numbers, and credit card details.
- Financial records:This could include bank account details, transaction history, and payroll information.
The compromise of such sensitive data could have significant consequences for affected organizations, including financial losses, legal liabilities, and reputational damage.
Potential Financial and Reputational Damage
The ransomware attack could have a significant financial impact on affected organizations. This could include:
- Ransom payments:Organizations may be forced to pay hefty ransoms to regain access to their data.
- Business disruption:The attack could disrupt critical operations, leading to lost revenue and productivity.
- Data recovery costs:Organizations may incur significant costs to recover their data and restore their systems.
- Legal and regulatory fines:Organizations could face fines for data breaches, especially if they fail to comply with data privacy regulations.
The attack could also cause significant reputational damage to affected organizations. This could include:
- Loss of customer trust:Customers may lose trust in organizations that have been compromised by ransomware attacks.
- Negative media coverage:Organizations could face negative media coverage, which could further damage their reputation.
- Damage to brand image:The attack could damage the brand image of affected organizations, making it harder to attract customers and partners.
The ransomware attack targeting ESXi servers serves as a stark reminder of the growing threat posed by cyberattacks to organizations of all sizes. It is crucial for organizations to take proactive steps to protect themselves against such attacks, including implementing robust security measures, regularly patching their systems, and conducting regular security audits.
The recent massive ransomware operation targeting VMware ESXi servers highlights the critical need for robust security measures. While a VPN alone can’t fully prevent such attacks, using a reputable service like one of the best Chrome VPN extensions can add an extra layer of protection by encrypting your internet traffic and masking your IP address.
This can help to deter attackers from targeting your system in the first place, or at least make it more difficult for them to access your sensitive data.
The Ransomware Group Behind the Attack: Massive Ransomware Operation Targets Vmware Esxi
The recent wave of ransomware attacks targeting VMware ESXi servers has been attributed to a sophisticated ransomware group known as “ESXiArgs.” While this group is relatively new, their tactics and impact have quickly gained attention in the cybersecurity community. Their attacks have been characterized by their large-scale nature, targeting thousands of vulnerable servers across various organizations.
ESXiArgs’ History and Tactics
ESXiArgs is believed to have emerged in early 2023, and their activities have steadily increased in frequency and scale. The group’s primary tactic involves exploiting vulnerabilities in VMware ESXi servers to gain unauthorized access. They often leverage known vulnerabilities, such as those associated with the OpenSLP service, to compromise systems.
Once they gain access, they deploy ransomware, encrypting data on the affected servers and demanding a ransom payment for its decryption.
ESXiArgs’ TTPs
- Exploiting Vulnerabilities:ESXiArgs leverages known vulnerabilities in VMware ESXi servers, such as those associated with the OpenSLP service, to gain initial access. They often exploit vulnerabilities that have been publicly disclosed but not yet patched by organizations.
- Lateral Movement:Once they gain access to a single server, they use various techniques to move laterally within the network. This includes using tools like PsExec to execute commands on other machines, and leveraging administrative privileges to gain control over other systems.
- Data Encryption:ESXiArgs employs powerful encryption algorithms to encrypt sensitive data on the compromised servers. This encryption makes the data inaccessible to the victim organization unless the ransom is paid.
- Ransom Demands:ESXiArgs typically demand a ransom payment in cryptocurrency, such as Bitcoin or Monero. They often provide instructions on how to pay the ransom and provide decryption keys once the payment is received.
ESXiArgs’ Motivations and Targets
ESXiArgs, like most ransomware groups, are motivated by financial gain. Their primary goal is to extort money from organizations by holding their data hostage. They target organizations that rely heavily on VMware ESXi servers, as these systems often store critical data and applications.
This includes organizations in various sectors, such as healthcare, finance, and manufacturing.
ESXiArgs’ Impact
ESXiArgs’ attacks have had a significant impact on organizations worldwide. The encryption of critical data can lead to severe business disruptions, including:
- Data Loss:If the ransom is not paid, organizations risk losing access to their data permanently. This can be devastating for businesses that rely on data for operations.
- Service Interruptions:The encryption of servers can lead to service outages, impacting business operations and customer service.
- Financial Losses:Organizations may incur significant financial losses due to downtime, data recovery costs, and ransom payments.
- Reputation Damage:Ransomware attacks can damage an organization’s reputation, impacting customer trust and brand loyalty.
Security Measures and Recommendations
The recent VMware ESXi ransomware attack highlights the importance of robust security measures to protect against similar threats. Organizations must prioritize proactive steps to mitigate risks and safeguard their critical systems.
Patching Vulnerabilities and Maintaining Up-to-Date Software
Regularly patching vulnerabilities is crucial to prevent attackers from exploiting known weaknesses. Software vendors, including VMware, release security patches to address identified vulnerabilities. Organizations must implement a comprehensive patching process that includes:
- Identifying vulnerabilities: Regularly scan systems for known vulnerabilities using vulnerability scanners or security tools.
- Prioritizing patches: Focus on patching critical vulnerabilities first, based on their severity and potential impact.
- Testing patches: Before deploying patches in production environments, test them in isolated environments to ensure compatibility and stability.
- Automated patching: Consider implementing automated patching solutions to streamline the process and ensure timely updates.
Data Backup and Recovery Best Practices
Effective data backup and recovery strategies are essential to minimize the impact of ransomware attacks. Organizations should implement the following best practices:
- Regular backups: Create regular backups of critical data and systems, ensuring that backups are stored offline and in a secure location.
- Multiple backup copies: Maintain multiple backup copies, using different methods such as cloud storage, tape, or air-gapped systems.
- Backup verification: Regularly test backup recovery processes to ensure that data can be restored effectively.
- Data encryption: Encrypt data at rest and in transit to protect it from unauthorized access, even if systems are compromised.
The Future of Ransomware Attacks

The recent surge in ransomware attacks targeting VMware ESXi servers is a stark reminder of the evolving threat landscape. These attacks highlight the vulnerabilities of critical infrastructure and the increasing sophistication of ransomware actors. It is crucial to understand the future trajectory of these attacks to effectively mitigate their impact.
The Evolving Threat Landscape
Ransomware attacks are becoming increasingly sophisticated, leveraging advanced techniques such as:
- Exploiting zero-day vulnerabilities:These are vulnerabilities unknown to vendors, allowing attackers to gain access before patches are available.
- Using malware to bypass security controls:Ransomware groups are employing advanced malware techniques to evade detection and circumvent security measures.
- Targeting critical infrastructure:Attacks on ESXi servers demonstrate a shift towards disrupting essential services, including healthcare, finance, and transportation.
- Leveraging double extortion:Attackers are now threatening to leak stolen data publicly if ransom demands are not met, adding another layer of pressure on victims.
The Role of Technology and Security Measures
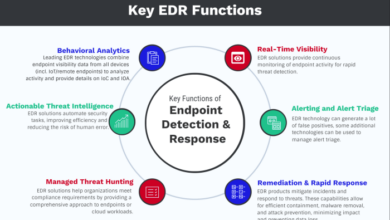
Technology plays a crucial role in mitigating ransomware threats. Organizations must implement a multi-layered approach to security, including:
- Regular patching and updates:Keeping software and systems up-to-date is essential to close vulnerabilities exploited by attackers.
- Network segmentation:Isolating critical systems from the internet reduces the attack surface and limits the impact of a breach.
- Endpoint security:Implementing robust endpoint protection solutions helps detect and prevent malware from infiltrating devices.
- Data backups and recovery:Regular backups and disaster recovery plans are crucial for restoring data and systems after a ransomware attack.
- Threat intelligence:Staying informed about emerging threats and attack methods is vital for proactive security measures.
Potential for Future Attacks Targeting ESXi Servers
The recent ESXi attacks are likely to serve as a blueprint for future ransomware operations. We can expect:
- More targeted attacks:Ransomware groups will likely focus on specific industries and critical infrastructure, leveraging vulnerabilities unique to those sectors.
- Increased use of automation:Attackers will automate their operations to scale attacks and increase their efficiency, targeting more victims simultaneously.
- Exploitation of new vulnerabilities:As technology evolves, attackers will seek out new vulnerabilities in software and systems, including those related to cloud computing and virtualization.