SentinelOne vs Palo Alto: Choosing the Right Endpoint Security
SentinelOne vs Palo Alto: In today’s threat landscape, securing your endpoints is crucial. Both SentinelOne and Palo Alto Networks are leading players in the endpoint security space, offering a wide range of features and capabilities. But which one is right for your organization?
This blog post will dive into the key differences between these two solutions, helping you make an informed decision.
From their core features and deployment models to pricing and customer support, we’ll explore the strengths and weaknesses of each vendor. Whether you’re a small business or a large enterprise, understanding the nuances of these solutions is vital for building a robust and effective security posture.
Endpoint Security in the Modern Threat Landscape
Endpoint security has become increasingly crucial in today’s digital world, where cyberattacks are growing in sophistication and frequency. Organizations face a relentless barrage of threats, including malware, ransomware, phishing, and zero-day exploits. These attacks can compromise sensitive data, disrupt business operations, and inflict significant financial damage.
As the attack surface expands with the adoption of remote work, cloud computing, and mobile devices, securing endpoints has become a top priority for businesses of all sizes.
SentinelOne and Palo Alto Networks: Leading Endpoint Security Vendors
SentinelOne and Palo Alto Networks are two leading vendors in the endpoint security market. Both companies offer comprehensive solutions that protect against a wide range of threats, including malware, ransomware, and advanced persistent threats (APTs). They are known for their innovative technologies, robust features, and strong track records in the industry.
Key Features and Capabilities of SentinelOne and Palo Alto Networks
Both SentinelOne and Palo Alto Networks offer a comprehensive suite of endpoint security features. Here’s a breakdown of their key capabilities:
- Next-Generation Antivirus (NGAV):Both vendors provide advanced antivirus protection that goes beyond traditional signature-based detection. They leverage machine learning, behavioral analysis, and threat intelligence to identify and block unknown and emerging threats.
- Endpoint Detection and Response (EDR):EDR is a critical component of modern endpoint security. It enables organizations to detect, investigate, and respond to security incidents in real time. Both SentinelOne and Palo Alto Networks offer robust EDR capabilities, including threat hunting, incident analysis, and automated remediation.
- Threat Intelligence:Both vendors integrate threat intelligence feeds from various sources to stay ahead of emerging threats. This intelligence helps them to proactively identify and block malicious activities before they can impact the organization.
- Vulnerability Management:Vulnerability management is crucial for identifying and mitigating security weaknesses in endpoints. Both SentinelOne and Palo Alto Networks offer tools to scan for vulnerabilities, prioritize remediation efforts, and track progress.
- Security Automation and Orchestration (SOAR):SOAR platforms streamline security operations by automating repetitive tasks, improving incident response times, and enhancing overall efficiency. Both vendors offer SOAR capabilities that integrate with their endpoint security solutions.
Key Features and Capabilities
Endpoint security solutions like SentinelOne and Palo Alto Networks offer a robust set of features to combat modern threats. This section will delve into the core capabilities of each vendor, comparing and contrasting their strengths and weaknesses in key areas.
Choosing between SentinelOne and Palo Alto Networks can be tough, especially when you’re trying to decide which platform best aligns with your cybersecurity needs. It’s interesting to see how Microsoft is pushing the boundaries of secure transactions with blockchain and the COCO framework, microsoft facilitates automated transactions with blockchain and the coco framework.
This innovative approach might even influence the future development of security solutions like SentinelOne and Palo Alto, as they seek to integrate emerging technologies for greater protection.
Endpoint Detection and Response (EDR)
EDR is a critical component of modern endpoint security, enabling organizations to detect, investigate, and respond to threats in real-time. Both SentinelOne and Palo Alto Networks provide comprehensive EDR solutions with distinct capabilities.
- SentinelOne: SentinelOne’s EDR solution is known for its AI-powered threat detection and response capabilities. It leverages machine learning algorithms to analyze endpoint behavior and identify suspicious activities. SentinelOne’s platform offers automated incident response, allowing for swift containment and remediation of threats.
A key strength is its ability to roll back attacks to a clean state, minimizing the impact of malicious activity.
- Palo Alto Networks: Palo Alto Networks’ EDR solution, part of its Cortex XDR platform, focuses on threat hunting and incident response. It utilizes a combination of behavioral analysis, threat intelligence, and machine learning to detect and respond to attacks. Cortex XDR provides a unified view of security events across multiple endpoints and network devices, enabling comprehensive threat investigation and response.
Next-Generation Antivirus (NGAV)
NGAV solutions go beyond traditional signature-based antivirus to detect and prevent a wider range of threats. Both SentinelOne and Palo Alto Networks offer NGAV capabilities with different approaches.
- SentinelOne: SentinelOne’s NGAV leverages a combination of behavioral analysis, machine learning, and static analysis to identify and block malware. It goes beyond traditional signature-based detection, offering protection against zero-day threats and fileless attacks. SentinelOne’s NGAV is integrated with its EDR solution, providing a unified platform for threat detection and response.
- Palo Alto Networks: Palo Alto Networks’ NGAV solution, part of its Traps platform, uses a multi-layered approach to threat prevention. It combines behavioral analysis, threat intelligence, and static analysis to identify and block malicious activity. Traps also leverages machine learning to adapt to evolving threats and provide proactive protection.
Threat Intelligence and Analytics
Effective threat intelligence is essential for understanding the threat landscape and proactively defending against attacks. Both SentinelOne and Palo Alto Networks provide threat intelligence capabilities to enhance their security solutions.
- SentinelOne: SentinelOne leverages its global threat intelligence network to provide real-time threat information and insights. Its platform analyzes data from millions of endpoints to identify emerging threats and provide proactive protection. SentinelOne also integrates with third-party threat intelligence feeds, expanding its threat detection and response capabilities.
- Palo Alto Networks: Palo Alto Networks’ threat intelligence platform, known as WildFire, analyzes suspicious files and URLs to identify malicious activity. WildFire provides real-time threat information and insights, enabling organizations to proactively defend against attacks. Palo Alto Networks also offers a range of threat intelligence services, including threat hunting and incident response.
Vulnerability Management
Vulnerability management is crucial for identifying and mitigating security weaknesses in software and hardware. Both SentinelOne and Palo Alto Networks offer vulnerability management capabilities to enhance their endpoint security solutions.
- SentinelOne: SentinelOne’s vulnerability management solution, part of its platform, automatically scans endpoints for vulnerabilities and provides remediation guidance. It integrates with popular vulnerability databases, such as the National Vulnerability Database (NVD), to provide comprehensive vulnerability assessments.
- Palo Alto Networks: Palo Alto Networks’ vulnerability management solution, part of its Prisma Cloud platform, offers a comprehensive approach to vulnerability assessment and remediation. It scans endpoints for vulnerabilities, provides remediation guidance, and automates the patching process. Prisma Cloud also integrates with other security tools, enabling a unified approach to vulnerability management.
Security Orchestration, Automation, and Response (SOAR)
SOAR solutions help organizations automate security workflows, improve efficiency, and accelerate incident response. Both SentinelOne and Palo Alto Networks offer SOAR capabilities to enhance their endpoint security solutions.
- SentinelOne: SentinelOne’s SOAR capabilities are integrated into its platform, providing automated incident response and remediation. It enables organizations to automate security workflows, such as incident investigation, containment, and remediation. SentinelOne’s SOAR solution is designed to be user-friendly, making it easy to configure and manage.
- Palo Alto Networks: Palo Alto Networks’ SOAR solution, part of its Cortex XSOAR platform, offers a comprehensive approach to security orchestration, automation, and response. Cortex XSOAR enables organizations to automate security workflows, integrate with various security tools, and accelerate incident response. Its platform is designed to be highly customizable and scalable, meeting the needs of organizations of all sizes.
Pricing and Licensing
Choosing the right endpoint security solution often involves careful consideration of pricing and licensing models. Both SentinelOne and Palo Alto Networks offer various options that cater to different organizational sizes and security needs. Understanding these models is crucial for making an informed decision that aligns with your budget and security requirements.
Pricing Models and Licensing Options
Both SentinelOne and Palo Alto Networks employ a subscription-based pricing model, with costs varying based on the number of endpoints protected, the features included, and the level of support desired.
- SentinelOne:SentinelOne offers a tiered pricing structure, with its core product, Singularity XDR, providing a comprehensive suite of endpoint security capabilities. The pricing is based on the number of endpoints protected, and customers can choose from different tiers, including:
- Essential:This tier offers basic endpoint protection with features like real-time threat detection, prevention, and response.
- Professional:This tier includes advanced capabilities like endpoint detection and response (EDR), threat intelligence, and vulnerability management.
- Enterprise:This tier provides the most comprehensive protection with features like managed detection and response (MDR), threat hunting, and integration with other security tools.
SentinelOne also offers flexible licensing options, allowing organizations to pay for only the features they need.
- Palo Alto Networks:Palo Alto Networks provides a similar tiered pricing structure for its endpoint security solutions, with options ranging from basic protection to advanced threat detection and response capabilities.
- Traps Advanced Endpoint Protection:This product offers comprehensive endpoint security, including threat prevention, detection, and response.
- Prisma Cloud:This solution provides cloud security, including workload protection, cloud access security broker (CASB), and cloud security posture management (CSPM).
Palo Alto Networks also offers a variety of licensing options, including per-endpoint, per-user, and per-device licensing.
Cost Implications for Different Organization Sizes and Security Needs
The cost implications of choosing between SentinelOne and Palo Alto Networks depend on factors such as the size of your organization, the complexity of your IT infrastructure, and your specific security needs.
- Small and Medium-Sized Businesses (SMBs):SMBs with limited budgets and IT resources may find SentinelOne’s Essential tier or Palo Alto Networks’ Traps Advanced Endpoint Protection to be more cost-effective. These solutions offer a balance of basic protection and affordability.
- Large Enterprises:Larger enterprises with complex IT environments and higher security requirements may benefit from the advanced features and comprehensive protection offered by SentinelOne’s Enterprise tier or Palo Alto Networks’ Prisma Cloud. While these solutions may be more expensive, they can provide the necessary level of security to protect sensitive data and critical infrastructure.
Customer Support and Resources
In addition to core features and pricing, customer support and resources play a crucial role in the overall value proposition of an endpoint security solution. Both SentinelOne and Palo Alto Networks offer robust support options, but their approaches and strengths differ.
Customer Support Services
Both SentinelOne and Palo Alto Networks provide comprehensive customer support services to assist users with product implementation, troubleshooting, and ongoing maintenance. These services typically include:
- Phone support:Both vendors offer 24/7 phone support for urgent issues.
- Email support:Users can submit support tickets via email for less urgent issues or detailed inquiries.
- Online knowledge base:Both SentinelOne and Palo Alto Networks maintain extensive online knowledge bases containing documentation, FAQs, and troubleshooting guides. These resources can often provide quick solutions to common problems.
- Community forums:Both vendors have active online communities where users can connect with each other, share experiences, and seek assistance from peers.
In terms of responsiveness, both SentinelOne and Palo Alto Networks are generally regarded as having strong support teams. However, the actual response times can vary depending on the severity of the issue and the time of day.
Documentation and Training Resources
Both vendors provide comprehensive documentation and training resources to help users maximize their investment in their endpoint security solutions.
- User manuals:Both SentinelOne and Palo Alto Networks offer detailed user manuals covering all aspects of their products, including installation, configuration, and advanced features.
- Online tutorials:Both vendors provide a range of online tutorials and video guides to walk users through various aspects of their products.
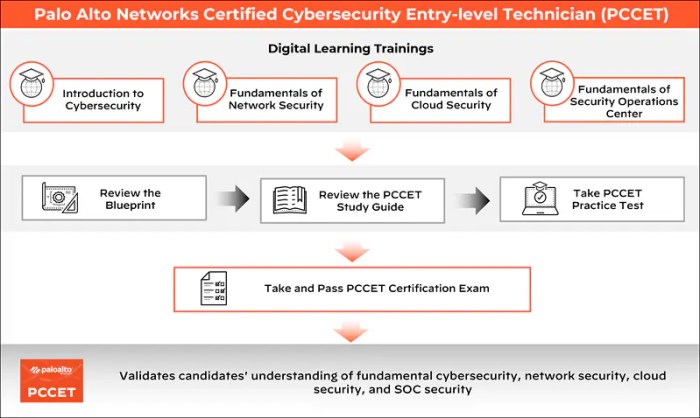
- Training courses:Both vendors offer a variety of training courses, both online and in-person, covering various topics, including product fundamentals, advanced configurations, and best practices.
- Certification programs:Both SentinelOne and Palo Alto Networks offer certification programs for professionals who want to demonstrate their expertise in their products.
The quality and comprehensiveness of the documentation and training resources offered by both vendors are generally well-regarded by users. The availability of certification programs is a particular advantage for organizations that want to ensure their staff has the necessary skills to effectively manage their endpoint security solutions.
Choosing between SentinelOne and Palo Alto Networks for endpoint security can be tough, as both offer robust features. But while you’re weighing those options, have you considered getting a lifetime subscription to OfficeSuite’s personal plan ? It’s a great value for productivity, and with all that document editing and management, you’ll want to make sure your endpoint security is top-notch.
Back to SentinelOne and Palo Alto, remember to consider your specific needs and budget when making your final decision.
Use Cases and Industry Applications
SentinelOne and Palo Alto Networks are both powerful endpoint security solutions, but their strengths lie in different areas. Understanding these differences is crucial for organizations to choose the right platform based on their specific needs and industry context.
Financial Services
Financial institutions are highly vulnerable to cyberattacks, making robust endpoint security a top priority. SentinelOne’s AI-powered threat detection and response capabilities excel in this sector, especially in detecting and mitigating zero-day attacks. Palo Alto Networks’ strong network security features, including its Next-Generation Firewall (NGFW), are also valuable for financial institutions, ensuring secure access to sensitive data and preventing unauthorized access.
Choosing between SentinelOne and Palo Alto Networks is a tough decision, especially when considering your overall security strategy. A crucial element in that strategy is a robust cloud disaster recovery plan , which ensures your business can bounce back from any incident.
Whether you opt for SentinelOne’s AI-driven approach or Palo Alto’s comprehensive suite, a solid recovery plan is essential to minimize downtime and protect your data, regardless of the endpoint protection solution you choose.
Healthcare
Healthcare organizations face unique challenges, including compliance with regulations like HIPAA and the need to protect sensitive patient data. SentinelOne’s ability to quickly identify and isolate infected endpoints helps minimize the impact of ransomware attacks, a common threat in this industry.
Palo Alto Networks’ strong network security features, including its NGFW, are also valuable for healthcare organizations, ensuring secure access to sensitive data and preventing unauthorized access.
Manufacturing
Manufacturing organizations rely on a diverse network of connected devices, making them susceptible to both traditional and industrial control system (ICS) attacks. SentinelOne’s endpoint detection and response (EDR) capabilities can effectively identify and respond to threats on these devices, while Palo Alto Networks’ network security solutions, including its NGFW, provide a strong layer of protection against external threats.
Government
Government agencies face an ever-increasing threat landscape, with attackers targeting critical infrastructure and sensitive data. SentinelOne’s advanced threat detection and response capabilities, including its AI-powered behavioral analysis, are well-suited for government agencies, enabling them to proactively identify and respond to threats.
Palo Alto Networks’ strong network security features, including its NGFW, are also valuable for government agencies, ensuring secure access to sensitive data and preventing unauthorized access.
Security Certifications and Compliance

In today’s digitally connected world, cybersecurity is paramount for organizations of all sizes. Ensuring the security of sensitive data and maintaining compliance with industry regulations is crucial. Security certifications and compliance standards serve as a testament to an organization’s commitment to security best practices and can be a valuable asset for building trust with customers and partners.
Security Certifications and Compliance Standards
Security certifications and compliance standards are crucial for organizations seeking to demonstrate their commitment to security best practices and meet regulatory requirements. These certifications and standards provide a framework for implementing robust security controls and verifying their effectiveness.
SentinelOne Certifications and Compliance
SentinelOne offers a comprehensive suite of security solutions that meet various industry-specific compliance standards. Some of the key certifications and compliance standards met by SentinelOne include:
- ISO 27001:This international standard for information security management systems (ISMS) ensures that SentinelOne’s products and services meet stringent security requirements.
- SOC 2 Type II:This certification verifies that SentinelOne’s controls related to security, availability, processing integrity, confidentiality, and privacy are designed and operating effectively.
- GDPR:SentinelOne is compliant with the General Data Protection Regulation (GDPR), ensuring the protection of personal data within the European Union.
- HIPAA:SentinelOne’s solutions meet the Health Insurance Portability and Accountability Act (HIPAA) requirements, ensuring the security of sensitive healthcare data.
- PCI DSS:SentinelOne is compliant with the Payment Card Industry Data Security Standard (PCI DSS), protecting cardholder data and preventing fraud.
Palo Alto Networks Certifications and Compliance
Palo Alto Networks, another leading cybersecurity vendor, also holds a wide range of security certifications and compliance standards. Some of the key certifications and compliance standards met by Palo Alto Networks include:
- ISO 27001:Palo Alto Networks’ products and services meet the requirements of ISO 27001, demonstrating their commitment to information security.
- SOC 2 Type II:Palo Alto Networks has achieved SOC 2 Type II certification, verifying the effectiveness of their security controls.
- GDPR:Palo Alto Networks is compliant with GDPR, ensuring the protection of personal data within the EU.
- HIPAA:Palo Alto Networks’ solutions meet HIPAA requirements, safeguarding sensitive healthcare information.
- PCI DSS:Palo Alto Networks is compliant with PCI DSS, protecting cardholder data and preventing fraud.
Implications for Organizations
The security certifications and compliance standards met by SentinelOne and Palo Alto Networks have significant implications for organizations seeking to meet regulatory requirements.
Demonstrating Security and Compliance
Organizations can leverage these certifications to demonstrate their commitment to security best practices and compliance with industry regulations. This can be particularly important for organizations operating in highly regulated industries such as healthcare, finance, and government.
Building Trust with Customers and Partners
Security certifications and compliance standards help build trust with customers and partners. By demonstrating their adherence to recognized security standards, organizations can reassure stakeholders that their data is protected and their operations are secure.
Reducing Risk and Liability
Compliance with security standards helps reduce the risk of security breaches and data leaks. By implementing robust security controls and adhering to industry regulations, organizations can mitigate potential legal and financial liabilities.
Enhancing Competitive Advantage
Organizations that prioritize security and compliance can gain a competitive advantage. Customers and partners are increasingly looking for vendors who can demonstrate a strong commitment to security.
“Security certifications and compliance standards are essential for organizations seeking to protect their data, meet regulatory requirements, and build trust with stakeholders.”
Integration with Other Security Tools
In today’s complex threat landscape, a comprehensive security strategy often involves integrating multiple security tools to enhance protection, visibility, and response capabilities. Both SentinelOne and Palo Alto Networks offer robust integration capabilities with a wide range of security solutions, enabling organizations to build a cohesive and effective security ecosystem.
Integration with SIEM
SIEM (Security Information and Event Management) systems play a crucial role in centralizing security data from various sources, providing real-time threat visibility and enabling incident response. Both SentinelOne and Palo Alto Networks offer seamless integration with leading SIEM platforms, such as Splunk, Elastic Stack (ELK), and IBM QRadar.
- SentinelOne provides a dedicated SIEM connector that allows it to send security events and logs to SIEM platforms in a standardized format, enabling efficient correlation and analysis.
- Palo Alto Networks’ integration with SIEM platforms leverages its own proprietary logging and event management framework, facilitating data ingestion and analysis for threat detection and incident response.
Integration with SOAR, Sentinelone vs palo alto
SOAR (Security Orchestration, Automation, and Response) platforms automate security workflows, streamline incident response, and improve operational efficiency. Both SentinelOne and Palo Alto Networks integrate with leading SOAR platforms, such as Demisto, ServiceNow, and IBM Resilient.
- SentinelOne’s integration with SOAR platforms enables automated incident response actions, such as isolating infected devices, quarantining malicious files, and triggering remediation scripts.
- Palo Alto Networks’ SOAR integration allows for automated threat hunting, incident investigation, and remediation, leveraging its comprehensive security data and threat intelligence.
Integration with Cloud Security Platforms
As organizations increasingly adopt cloud services, integrating endpoint security solutions with cloud security platforms is essential for comprehensive protection. Both SentinelOne and Palo Alto Networks offer integration with leading cloud security platforms, such as AWS, Azure, and Google Cloud.
- SentinelOne’s cloud integration provides visibility and control over endpoints deployed in cloud environments, enabling consistent security policies and threat detection across on-premises and cloud infrastructure.
- Palo Alto Networks’ cloud security solutions integrate with its endpoint security platform, offering a unified approach to protecting both on-premises and cloud-based endpoints.
Performance and Scalability
In today’s threat landscape, endpoint security solutions must be able to handle large numbers of endpoints and complex security threats without compromising performance. This is crucial for maintaining business operations and ensuring continuous security protection. Let’s delve into how SentinelOne and Palo Alto Networks perform in real-world deployments, examining their ability to scale and deliver efficient protection.
Performance in Real-World Deployments
Performance is critical for any endpoint security solution, as it directly impacts the user experience and overall system efficiency. SentinelOne and Palo Alto Networks both boast impressive performance metrics, but real-world deployments provide valuable insights into their capabilities. SentinelOne, known for its lightweight agent and cloud-native architecture, has consistently demonstrated excellent performance, even with a large number of endpoints.
Its agent’s minimal resource consumption ensures minimal impact on system performance, allowing users to experience seamless operations. Palo Alto Networks, with its traditional agent-based approach, can sometimes experience performance challenges, especially when dealing with a large number of endpoints. While its agent is optimized for efficiency, it may require more system resources compared to SentinelOne’s cloud-native solution.
Scalability in Large Environments
Scalability is crucial for organizations with geographically dispersed endpoints or rapidly expanding infrastructures. The ability to manage and protect a growing number of endpoints without impacting performance is essential.SentinelOne’s cloud-native architecture offers inherent scalability, allowing it to manage millions of endpoints efficiently.
Its cloud infrastructure allows for flexible scaling and resource allocation, ensuring seamless protection as the number of endpoints increases. Palo Alto Networks, with its traditional agent-based approach, requires careful planning and resource management to scale effectively. While its solution can handle large environments, it may require more infrastructure investment and dedicated resources compared to SentinelOne’s cloud-native approach.
Handling Complex Security Threats
Modern security threats are increasingly sophisticated, requiring advanced detection and response capabilities. Both SentinelOne and Palo Alto Networks employ sophisticated technologies to identify and mitigate complex threats.SentinelOne’s AI-powered engine continuously learns and adapts to new threats, providing proactive protection against unknown and emerging attacks.
Its behavioral analysis and machine learning capabilities enable it to detect even the most elusive threats.Palo Alto Networks leverages its extensive threat intelligence database and advanced threat detection technologies to identify and respond to complex threats. Its sandboxing capabilities provide a safe environment to analyze suspicious files and prevent malicious activity.
Performance Optimization and Resource Management
Both SentinelOne and Palo Alto Networks offer features to optimize performance and manage resources effectively.SentinelOne’s cloud-native architecture enables centralized management and resource allocation, ensuring optimal performance across all endpoints. Its intelligent resource management capabilities dynamically adjust resource utilization based on real-time threats and system load.Palo Alto Networks provides tools for performance monitoring and tuning, allowing administrators to optimize resource utilization and ensure smooth operation.
Its agent configuration options allow for customization to minimize resource consumption and optimize performance based on specific environment requirements.
Future Trends and Innovations: Sentinelone Vs Palo Alto

The endpoint security landscape is constantly evolving, driven by the increasing sophistication of cyberattacks and the rise of new technologies. SentinelOne and Palo Alto Networks are both actively adapting to these trends, incorporating new technologies and approaches into their platforms to maintain their effectiveness in protecting organizations from modern threats.
Emerging Trends in Endpoint Security
The endpoint security landscape is characterized by several emerging trends, each demanding new solutions and approaches from vendors like SentinelOne and Palo Alto Networks.
- Rise of Cloud-Native Environments:The increasing adoption of cloud-native applications and infrastructure necessitates endpoint security solutions that can effectively protect these environments. Both SentinelOne and Palo Alto Networks are expanding their offerings to provide comprehensive cloud-based security solutions, encompassing workload protection, threat detection, and response capabilities.
- Growing Prevalence of Zero-Trust Security:Zero-trust security principles are becoming increasingly popular, demanding that all access to resources be verified and authenticated. SentinelOne and Palo Alto Networks are incorporating zero-trust principles into their platforms, implementing granular access controls, multi-factor authentication, and continuous threat monitoring to ensure secure access to sensitive data and applications.
- Increasing Use of Artificial Intelligence (AI) and Machine Learning (ML):AI and ML are playing an increasingly vital role in endpoint security, enabling faster and more accurate threat detection, response, and prevention. Both SentinelOne and Palo Alto Networks are leveraging these technologies to enhance their threat intelligence capabilities, automate incident response, and improve the overall effectiveness of their platforms.
- Integration with Extended Detection and Response (XDR):XDR is an emerging security approach that consolidates data from various security tools, enabling a holistic view of threats across the organization. SentinelOne and Palo Alto Networks are actively integrating their endpoint security solutions with XDR platforms to provide a comprehensive and coordinated approach to threat detection and response.
Adapting to the Evolving Threat Landscape
SentinelOne and Palo Alto Networks are responding to the evolving threat landscape by incorporating the following innovations into their platforms:
- Next-Generation Endpoint Protection:Both companies are developing next-generation endpoint protection solutions that leverage AI, ML, and behavioral analysis to detect and prevent advanced threats, including zero-day attacks and fileless malware.
- Threat Hunting and Response Automation:They are introducing advanced threat hunting capabilities that enable security teams to proactively identify and investigate suspicious activities. They are also automating incident response processes to reduce the time it takes to contain and remediate threats.
- Enhanced Cloud Security:They are expanding their cloud security offerings to protect cloud-native applications and workloads, including serverless computing and containerized applications.
- Integration with Security Information and Event Management (SIEM) and Security Orchestration, Automation, and Response (SOAR):They are integrating their endpoint security solutions with SIEM and SOAR platforms to provide a comprehensive and centralized view of security events and automate incident response processes.