
Data Stealing Malware Study: A Deep Dive
Data stealing malware study is a critical area of cybersecurity research. It delves into the malicious software designed to steal sensitive information from unsuspecting victims. This type of malware can have devastating consequences for individuals, businesses, and even governments. The motivations behind these attacks are diverse, ranging from financial gain to espionage and even personal vendettas.
Understanding the inner workings of data stealing malware is crucial for safeguarding our digital lives. This study explores various types of malware, their infection vectors, data exfiltration techniques, and effective detection and prevention methods. We’ll also examine real-world case studies to understand the impact of these attacks and identify emerging trends in the evolving landscape of cybercrime.
Data Stealing Malware: A Threat to Individuals and Organizations
Data stealing malware is a type of malicious software designed to infiltrate computer systems and steal sensitive information. These programs operate stealthily, often without the user’s knowledge, to collect data and transmit it to the attacker’s control. The information targeted by data stealing malware can range from personal details like passwords and credit card numbers to confidential business data, intellectual property, and proprietary information.The motivations behind data theft are diverse and can include financial gain, espionage, extortion, and identity theft.
Impact of Data Stealing Malware
Data stealing malware has a significant impact on both individuals and organizations, leading to various consequences:
- Financial Loss:Stolen financial information, such as credit card numbers and bank account details, can be used for fraudulent transactions, leading to significant financial losses for individuals and organizations.
- Identity Theft:Data stealing malware can compromise personal information, such as social security numbers, addresses, and birth dates, enabling identity theft, a crime that can have long-term repercussions for victims.
- Reputational Damage:Data breaches caused by data stealing malware can damage an organization’s reputation, erode customer trust, and lead to negative publicity, impacting its brand image and market value.
- Legal and Regulatory Penalties:Organizations that experience data breaches due to data stealing malware may face legal action and regulatory fines, depending on the nature of the stolen data and the severity of the breach.
- Disruption of Business Operations:Data stealing malware can disrupt business operations by compromising critical systems, causing downtime, and hindering productivity.
Types of Data Stealing Malware: Data Stealing Malware Study
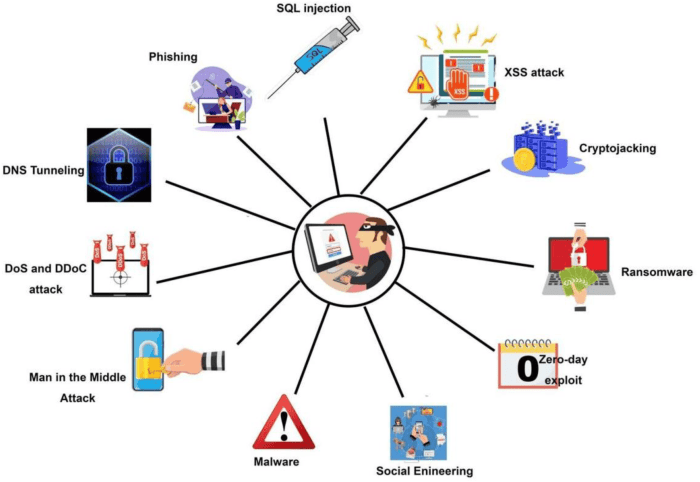
Data stealing malware is a broad category encompassing various tools and techniques employed by malicious actors to extract sensitive information from unsuspecting victims. These tools vary in their methods and targets, making it essential to understand the different types to effectively protect against them.
Keyloggers
Keyloggers are a type of malware that records every keystroke made on a compromised device. This includes passwords, credit card numbers, personal messages, and any other data entered by the user. Keyloggers operate silently in the background, capturing all keystrokes without the user’s knowledge.
They are commonly used by cybercriminals to steal financial information, login credentials, and other sensitive data.
Keyloggers can be installed through malicious emails, websites, or even physical devices. They can also be embedded in legitimate software, making it difficult for users to detect them.
Screen Capturers
Screen capturers, as the name suggests, capture screenshots of the user’s screen activity. This allows attackers to monitor what the user is viewing and doing on their computer. Screen capturers can be used to steal financial information, login credentials, and other sensitive data, especially when used in conjunction with keyloggers.
The latest data stealing malware study highlights the increasing sophistication of cyberattacks, targeting sensitive information like financial data and personal details. It’s a stark reminder that even with the latest technology, security remains paramount. Speaking of tech, it’s fascinating to see how the public is reacting to the Apple Vision Pro, with some of the most viral videos and memes showcasing its capabilities and limitations.
The public has gotten their hands on Apple Vision Pro here are the most viral videos and memes so far This wave of user-generated content is a valuable insight into how the public perceives new technologies and their potential impact on our lives, reminding us that even the most advanced devices can be subject to scrutiny and humor.
They can also be used to record sensitive information displayed on the screen, such as credit card numbers entered during online transactions.
Screen capturers are particularly effective in stealing information from online banking sessions, as they can capture the entire screen, including the user’s login credentials and transaction details.
Password Stealers
Password stealers target the user’s stored passwords, aiming to gain access to their online accounts. These malicious programs can steal passwords from web browsers, email clients, and other applications that store login credentials. Password stealers often work by searching for and extracting passwords from the user’s computer, or by intercepting password data transmitted over the network.
Examples of password stealers include the infamous “Zeus” Trojan, which targeted online banking accounts, and “Credential Stealer,” which steals passwords from web browsers.
Banking Trojans
Banking Trojans are specifically designed to target online banking accounts. They work by intercepting and manipulating online banking transactions, allowing attackers to steal financial information and funds. Banking Trojans often use sophisticated techniques to evade detection, including hiding within legitimate software or using encryption to protect their communication.
One of the most notorious banking Trojans is “Dridex,” which has been responsible for stealing millions of dollars from banks and individuals worldwide.
Infection Vectors and Spread
Data stealing malware, like any other malicious software, needs a way to infiltrate a system. This is where infection vectors come into play. These are the pathways that attackers use to introduce the malware into a vulnerable environment. Understanding these vectors is crucial for implementing effective security measures and preventing infections.
Common Infection Vectors
The methods employed by attackers to spread data stealing malware are constantly evolving. Here are some of the most prevalent infection vectors:
- Phishing Emails: Phishing emails are one of the most common ways data stealing malware is distributed. These emails often masquerade as legitimate messages from trusted sources, like banks, online retailers, or social media platforms. They might contain malicious attachments, links to infected websites, or requests for sensitive information, such as login credentials or credit card details.
The goal is to trick users into clicking on the malicious link or opening the attachment, which then installs the malware on their device.
- Malicious Websites: Visiting compromised websites or those designed to spread malware can also lead to infection. These websites might contain malicious scripts that exploit vulnerabilities in the user’s browser or operating system, allowing the malware to download and install itself without the user’s knowledge.
- Infected Software: Downloading and installing software from untrusted sources or using pirated software can expose users to data stealing malware. Hackers often disguise malware as legitimate software or bundle it with other free programs. When users install these infected applications, they unwittingly grant the malware access to their systems and personal data.
My latest data stealing malware study got me thinking about how technology can be used for both good and bad. It’s fascinating how easily data can be compromised, but on the flip side, there’s so much potential for positive innovation.
Take apple vision pros spatial personas could bring couch co op gaming back for a whole new generation , for example. Imagine the possibilities for collaborative gaming and shared experiences. It’s a reminder that technology can be a powerful tool for connection, even as we navigate the challenges of cybersecurity.
- Exploiting Software Vulnerabilities: Hackers often target known vulnerabilities in popular software applications and operating systems to gain access to systems. These vulnerabilities can be exploited to install malware without the user’s knowledge or consent. Software vendors regularly release security patches to address these vulnerabilities, so it’s essential to keep software updated to mitigate the risk of infection.
- USB Drives and Removable Media: Data stealing malware can also be spread through infected USB drives, external hard drives, or other removable media. If an infected device is connected to a computer, the malware can spread to the system without the user’s knowledge.
Malware Propagation and Spread
Once data stealing malware has infected a device, it can spread to other systems on the same network or even to external networks. Here’s how:
- Network Sharing: Some data stealing malware can exploit network shares to spread to other devices on the same network. This allows the malware to access and steal data from multiple computers without the user’s knowledge.
- Exploiting Network Vulnerabilities: Attackers can use vulnerabilities in network devices, such as routers and switches, to gain access to the network and spread malware. This allows them to infect multiple systems without targeting individual users.
- Social Engineering: Attackers often use social engineering techniques to trick users into spreading malware. This might involve sending malicious emails that appear to be from a trusted source, or using fake websites to trick users into downloading malware.
Techniques to Bypass Security Measures
Data stealing malware is often designed to evade detection by security software. Here are some techniques attackers use to bypass security measures:
- Code Obfuscation: Attackers use code obfuscation techniques to make the malware’s code difficult to understand and analyze. This makes it harder for security software to detect and block the malware.
- Rootkit Techniques: Rootkits are designed to hide malware from detection by security software. They can modify the operating system to conceal the malware’s presence and prevent it from being detected.
- Exploiting Security Software Vulnerabilities: Attackers might exploit vulnerabilities in security software to bypass its defenses. This allows them to install malware or modify the software to prevent it from detecting malicious activity.
- Using Legitimate Tools: Attackers can use legitimate tools, such as scripting languages or network protocols, to carry out malicious activities. This can make it difficult for security software to detect and block the malware.
Data Exfiltration Techniques
Data exfiltration is the process by which stolen data is transferred from the compromised system to a location controlled by the attacker. This is the final stage of the data stealing malware lifecycle, and it’s crucial for the attacker to achieve their objectives.
Attackers employ various techniques to exfiltrate data, each with its own advantages and disadvantages.
Covert Channels
Covert channels are communication channels that are hidden from standard security monitoring tools. Attackers use them to exfiltrate data discreetly, avoiding detection. Here are some common covert channel techniques:
- DNS Tunneling:Attackers can use DNS requests to exfiltrate data. They encode the stolen data within DNS queries and send them to a DNS server under their control. The server then decodes the data and retrieves it. This method is particularly effective because DNS traffic is typically allowed through firewalls and is often not closely monitored.
- HTTP Tunneling:Similar to DNS tunneling, attackers can use HTTP requests to exfiltrate data. They can embed stolen data within the headers or body of HTTP requests. This method leverages the fact that HTTP traffic is ubiquitous and is often not subject to strict scrutiny.
- TCP/IP Protocol:Attackers can use standard TCP/IP protocols like ICMP (Internet Control Message Protocol) to exfiltrate data. They can modify the data packets to carry stolen information and send them to a remote server. This technique is effective because it uses legitimate network protocols and can blend in with normal network traffic.
Remote Access Tools, Data stealing malware study
Remote access tools (RATs) provide attackers with remote access to compromised systems. This allows them to exfiltrate data directly, manage the system, and potentially deploy additional malware. RATs can be used to:
- Transfer Files:RATs allow attackers to download and upload files from the compromised system. This enables them to easily exfiltrate stolen data.
- Execute Commands:RATs give attackers the ability to execute commands on the compromised system. This allows them to gather sensitive information, delete files, and even modify system settings.
- Monitor Activity:Some RATs allow attackers to monitor user activity on the compromised system, including keystrokes, screen captures, and webcam footage. This information can be valuable for intelligence gathering and identity theft.
Obfuscation Techniques
Attackers employ various obfuscation techniques to conceal their activities and evade detection. These techniques make it difficult for security tools to identify and analyze malicious traffic:
- Data Encoding:Attackers can encode stolen data using various algorithms to make it appear as random noise. This makes it difficult for security tools to recognize the data as sensitive information.
- Traffic Encryption:Attackers can encrypt the stolen data before exfiltration. This makes it difficult for security tools to decrypt and analyze the data. However, encrypted traffic can still be suspicious, especially if it’s directed to an unusual destination.
- Traffic Fragmentation:Attackers can break down the stolen data into small fragments and send them over multiple connections. This makes it difficult to track the entire data stream and identify the exfiltration activity.
- Randomization:Attackers can randomize the timing and destination of data exfiltration to avoid predictable patterns. This makes it harder for security tools to identify the malicious activity.
Challenges in Identifying and Tracking Data Exfiltration
Identifying and tracking data exfiltration presents significant challenges:
- Volume of Network Traffic:The volume of network traffic makes it difficult to identify malicious activity amidst legitimate traffic. Attackers can leverage this to blend their exfiltration activities with normal network operations.
- Evolving Techniques:Attackers constantly evolve their techniques, making it difficult for security tools to keep up. This requires continuous updates and improvements in security solutions to effectively detect and prevent data exfiltration.
- Lack of Visibility:Organizations may lack visibility into their network traffic, especially in complex environments. This can make it difficult to detect and track exfiltration attempts, especially if attackers are using sophisticated techniques.
- Limited Resources:Organizations may have limited resources to invest in security tools and expertise. This can make it difficult to implement robust security measures to prevent data exfiltration.
Detection and Prevention

The battle against data stealing malware requires a multi-layered approach, encompassing proactive security measures and effective detection mechanisms. A robust defense strategy involves employing advanced endpoint security solutions, fostering user awareness, and implementing best practices to fortify systems and networks.
Endpoint Security Solutions
Endpoint security solutions play a crucial role in detecting and preventing data stealing malware. These solutions act as the first line of defense against malicious threats, providing real-time protection for individual devices and networks. Endpoint security solutions often incorporate various features, including:
- Antivirus and Anti-malware Software:These programs scan files and processes for known malware signatures, identifying and removing threats before they can compromise systems. They utilize various detection techniques, including signature-based detection, heuristic analysis, and behavioral analysis.
- Firewall:Firewalls act as a barrier between a device and external networks, filtering incoming and outgoing traffic. They block unauthorized connections and prevent malicious actors from accessing sensitive data. Modern firewalls often include advanced features like intrusion detection and prevention systems (IDS/IPS) to detect and block suspicious activities.
- Endpoint Detection and Response (EDR):EDR solutions go beyond traditional antivirus software by providing continuous monitoring and threat hunting capabilities. They collect and analyze data from endpoints, identifying suspicious activities and potential threats that might have evaded traditional antivirus detection. EDR systems can also automate incident response actions, such as isolating infected devices or quarantining malicious files.
The recent study on data stealing malware highlighted the growing threat of sophisticated attacks targeting personal information. It’s a sobering reminder of the importance of robust security measures, especially when considering devices like the iPad Pro and Surface Pro.
For those looking for a powerful tablet alternative, you might want to check out this in-depth comparison of the M4 iPad Pro and Surface Pro 11 m4 ipad pro vs surface pro 11 how does microsofts ipad pro alternative stack up to make an informed decision about which device best suits your security needs and workflow.
- Data Loss Prevention (DLP):DLP solutions are specifically designed to prevent sensitive data from leaving the organization’s network. They monitor data flows, identify confidential information, and block attempts to exfiltrate data through unauthorized channels. DLP solutions can be deployed on endpoints, servers, and network gateways to ensure data security.
User Education and Awareness
User education and awareness are essential in preventing data stealing malware infections. Educating users about common malware threats, infection vectors, and best practices for online safety can significantly reduce the risk of falling victim to these attacks.
- Phishing Awareness:Phishing attacks are a common method used to trick users into revealing sensitive information or downloading malware. Educating users about phishing tactics, such as recognizing suspicious emails, websites, or social media messages, is crucial. Users should be trained to verify the legitimacy of requests for personal information and to be cautious when clicking on links or opening attachments from unknown sources.
- Password Security:Strong and unique passwords are essential for protecting online accounts and preventing unauthorized access. Users should be encouraged to create complex passwords, avoid using the same password across multiple accounts, and enable multi-factor authentication whenever possible.
- Software Updates:Software vulnerabilities can be exploited by attackers to gain access to systems and steal data. Regularly updating software, including operating systems, applications, and security tools, is essential for patching vulnerabilities and staying ahead of emerging threats.
- Social Engineering Awareness:Social engineering attacks exploit human psychology to trick users into providing sensitive information or granting access to systems. Educating users about social engineering tactics, such as impersonation, baiting, and pretexting, can help them avoid falling victim to these attacks.
Best Practices for Securing Systems and Networks
Implementing best practices for securing systems and networks is crucial for preventing data theft. These practices encompass a range of security measures that strengthen defenses and minimize vulnerabilities.
- Strong Passwords and Multi-Factor Authentication:Implementing strong password policies and encouraging the use of multi-factor authentication are essential for protecting accounts and preventing unauthorized access. This involves requiring users to create complex passwords, avoid using the same password across multiple accounts, and enabling multi-factor authentication whenever possible.
- Regular Security Audits and Vulnerability Assessments:Regular security audits and vulnerability assessments help identify and address security weaknesses in systems and networks. These assessments involve scanning systems for vulnerabilities, identifying misconfigurations, and recommending remediation steps. By proactively addressing vulnerabilities, organizations can minimize the risk of data theft.
- Network Segmentation:Network segmentation involves dividing a network into smaller, isolated segments to limit the impact of a security breach. By segregating sensitive data and critical systems, organizations can prevent attackers from gaining access to valuable information even if one segment is compromised.
This approach helps contain the spread of malware and limits the potential damage.
- Data Encryption:Encrypting sensitive data at rest and in transit is essential for protecting it from unauthorized access. Data encryption transforms data into an unreadable format, making it difficult for attackers to decipher even if they gain access to the data. Encryption can be implemented at various levels, including disk encryption, database encryption, and network encryption.
- Security Awareness Training:Regularly conducting security awareness training for employees is essential for fostering a security-conscious culture. Training programs should cover topics such as phishing attacks, social engineering tactics, best practices for password security, and reporting suspicious activities. By raising awareness and providing employees with the knowledge and skills to identify and respond to security threats, organizations can reduce the risk of data theft.
Mitigation and Response

The effectiveness of any security strategy depends on its ability to mitigate the impact of attacks. This section will explore the critical steps to take when a data stealing malware infection is detected, focusing on incident response and recovery.
Incident Response and Recovery
A comprehensive incident response plan is essential for minimizing the damage caused by data stealing malware. It Artikels the steps to be taken when an attack is detected, ensuring a swift and effective response.
- Containment:The first priority is to isolate the infected system or network to prevent further spread of the malware. This may involve disconnecting the affected device from the network, shutting down relevant services, or implementing network segmentation.
- Analysis:A thorough analysis of the attack is necessary to understand the malware’s capabilities, the data it has stolen, and the infection vector used. This analysis involves examining system logs, network traffic, and potentially analyzing the malware itself.
- Data Recovery:Once the malware is contained, efforts should be made to recover any stolen data. This may involve restoring backups, using data recovery tools, or collaborating with forensic experts.
- Remediation:After data recovery, the infected system needs to be fully remediated. This involves removing the malware, patching vulnerabilities, and implementing stronger security measures to prevent future attacks.
- Communication:Transparent communication with affected individuals and stakeholders is crucial. This includes informing them about the incident, the steps taken to mitigate the impact, and the measures being implemented to prevent future attacks.
Data Recovery and Forensic Analysis
Data recovery is a crucial step in the incident response process. It aims to restore lost or compromised data, minimizing the impact of the attack. Forensic analysis, on the other hand, plays a vital role in understanding the attack, identifying the attackers, and gathering evidence for potential legal action.
- Data Recovery Techniques:Various techniques can be employed to recover stolen data. These include restoring backups, using data recovery tools, and collaborating with forensic experts. The choice of technique depends on the type of data lost, the severity of the attack, and the available resources.
- Forensic Analysis:Forensic analysis involves collecting and examining digital evidence to reconstruct the attack, identify the attackers, and gather evidence for legal action. This process often involves analyzing system logs, network traffic, and potentially the malware itself.
- Importance of Forensic Analysis:Forensic analysis is crucial for understanding the attack, identifying the attackers, and gathering evidence for potential legal action. It can help organizations improve their security posture by identifying vulnerabilities exploited by the attackers and implementing measures to prevent future attacks.
Case Studies
Real-world examples of data stealing malware attacks provide valuable insights into the tactics employed by attackers, the vulnerabilities exploited, and the devastating consequences of such incidents. Examining these cases helps us understand the evolving landscape of cybercrime and develop effective countermeasures to protect individuals and organizations.
The NotPetya Ransomware Attack
The NotPetya ransomware attack, which began in June 2017, targeted businesses worldwide, causing billions of dollars in damage. Disguised as a legitimate software update, NotPetya spread rapidly, encrypting files and demanding ransom payments. This attack had a significant impact on various industries, including shipping, pharmaceuticals, and energy.
- Method:The attack leveraged a vulnerability in a Ukrainian accounting software called M.E.Doc. Attackers used a phishing email to distribute the malware, which then exploited the vulnerability to spread laterally within networks. The malware used a combination of techniques, including file encryption, network propagation, and data destruction, to cripple targeted systems.
- Impact:The attack disrupted operations for numerous businesses, leading to significant financial losses and operational downtime. Some companies, particularly those in the shipping and logistics industry, experienced lasting disruptions to their supply chains. The attack highlighted the importance of robust security measures, including regular software updates, strong password policies, and multi-factor authentication.
- Lessons Learned:The NotPetya attack demonstrated the potential for ransomware to cause widespread damage and disruption. It also highlighted the importance of implementing a comprehensive cybersecurity strategy that includes regular security assessments, incident response planning, and data backups.
The Equifax Data Breach
In 2017, Equifax, a major credit reporting agency, experienced a massive data breach that exposed the personal information of over 147 million individuals. The breach involved the theft of sensitive data, including Social Security numbers, birth dates, and credit card numbers.
- Method:The attackers exploited a vulnerability in the Apache Struts web application framework, which was used by Equifax. The vulnerability allowed attackers to gain unauthorized access to the company’s systems and steal sensitive data. Equifax was criticized for its slow response to the breach and its handling of the aftermath.
- Impact:The Equifax data breach had a profound impact on millions of individuals, putting them at risk of identity theft and fraud. The company faced significant legal and financial consequences, including class-action lawsuits and regulatory fines.
- Lessons Learned:The Equifax data breach emphasized the need for organizations to prioritize data security and to implement robust security measures, including regular vulnerability scans, patch management, and incident response plans. The breach also highlighted the importance of transparency and communication with affected individuals in the event of a data breach.
Emerging Trends
The landscape of data stealing malware is constantly evolving, driven by the relentless pursuit of attackers to find new ways to exploit vulnerabilities and evade detection. This evolution is fueled by advancements in technology, particularly the emergence of artificial intelligence (AI) and machine learning (ML).
These technologies are being weaponized by attackers to enhance the effectiveness of their malware, making it more sophisticated, adaptable, and difficult to counter.
Use of AI and ML in Data Stealing Malware
The integration of AI and ML into data stealing malware is revolutionizing the threat landscape. Attackers are leveraging these technologies to automate various aspects of their operations, from identifying targets to evading security measures.
- Automated Target Identification:AI-powered malware can analyze vast amounts of data to identify potential targets based on factors like their vulnerability profile, network infrastructure, and sensitive information. This enables attackers to focus their efforts on high-value targets, increasing their chances of success.
- Adaptive Malware:AI algorithms can enable malware to adapt to changes in security environments, such as new anti-virus signatures or network configurations. This dynamic adaptation makes it harder for traditional security solutions to detect and neutralize threats.
- Enhanced Data Exfiltration:AI-powered malware can use machine learning to optimize data exfiltration techniques, ensuring that stolen data is transmitted discreetly and effectively. This involves selecting the most suitable channels and methods for data transfer, minimizing the risk of detection.
- Automated Exploitation:AI and ML can automate the process of identifying and exploiting vulnerabilities in software and systems. This reduces the need for human intervention, allowing attackers to launch attacks more efficiently and at scale.
New Techniques and Tactics
Attackers are constantly innovating, developing new techniques and tactics to bypass security measures and steal sensitive data. Some of the emerging trends include:
- Living off the Land (LOLBin):Attackers are increasingly relying on legitimate system tools and utilities to carry out their operations. This technique, known as LOLBin, helps them avoid detection by security solutions that focus on identifying malicious software.
- Fileless Malware:Fileless malware operates entirely in memory, making it difficult to detect and remove. This type of malware can be injected into legitimate processes or exploit system vulnerabilities to execute its malicious code without leaving any traces on disk.
- Supply Chain Attacks:Attackers are targeting software supply chains to compromise trusted software packages. This allows them to distribute malicious code to a wide range of users, infecting their systems without their knowledge.
- Zero-Day Exploits:These are vulnerabilities in software that are unknown to the vendor and have not been patched. Attackers can exploit these vulnerabilities before security solutions have been updated, gaining access to systems and data.
- Ransomware with Data Stealing Capabilities:Attackers are combining ransomware with data stealing capabilities, making it even more lucrative for them. In these attacks, victims are not only forced to pay a ransom to recover their data but also face the risk of their sensitive information being leaked online.
Future of Data Stealing Malware
The future of data stealing malware is likely to be characterized by increased sophistication, automation, and stealth. AI and ML will continue to play a crucial role in driving these trends, enabling attackers to develop more advanced and evasive malware.
“The future of cyberattacks will be increasingly driven by AI and ML, making it even more challenging for organizations to defend themselves. We need to invest in new technologies and strategies to stay ahead of the curve.”
[Expert Name], Cybersecurity Expert
The potential impact of these trends is significant. Organizations and individuals need to be prepared for a new wave of data stealing attacks that are more targeted, automated, and difficult to detect.







