Cisa Open Source Security Roadmap


CISA’s Open Source Security Roadmap: Fortifying the Digital Backbone
The Cybersecurity and Infrastructure Security Agency (CISA) has released a critical roadmap aimed at enhancing the security of open-source software (OSS), a foundational element of modern technology infrastructure. This initiative, driven by the pervasive reliance on OSS across government, industry, and critical infrastructure, acknowledges the inherent security challenges and seeks to establish a more robust and resilient ecosystem. The roadmap identifies key areas for improvement, including vulnerability management, secure development practices, incident response, and fostering a collaborative security culture. Its overarching goal is to mitigate risks associated with OSS, ensuring its continued beneficial use while safeguarding against potential exploitation. Understanding this roadmap is paramount for any organization that utilizes or contributes to open-source projects.
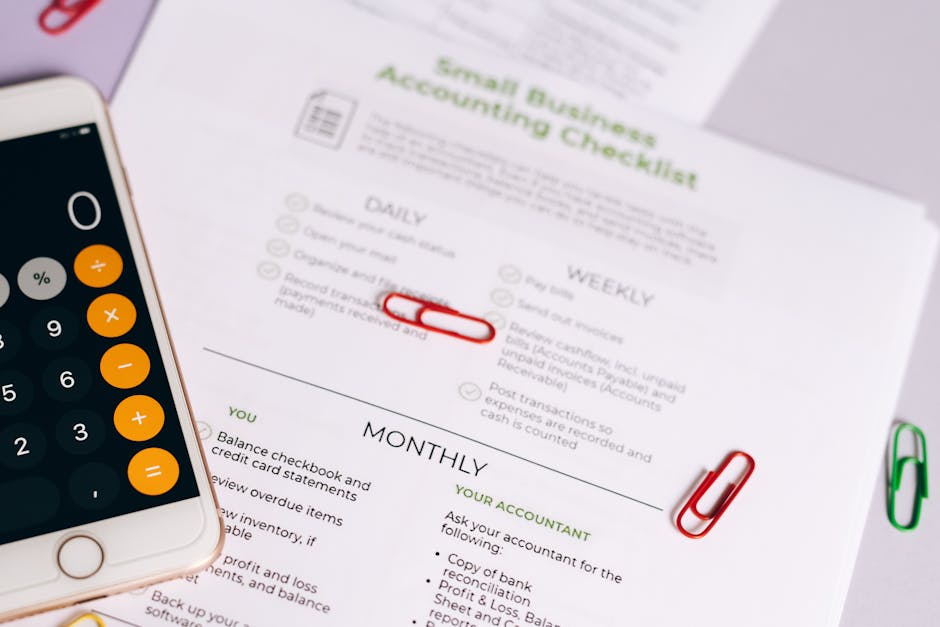
The CISA roadmap is structured around several pillars, each addressing a distinct facet of OSS security. The first pillar, "Understanding and Prioritizing Risks," emphasizes the need for comprehensive awareness of the OSS supply chain. This involves identifying the OSS components in use, understanding their dependencies, and assessing their associated vulnerabilities. CISA advocates for the widespread adoption of Software Bill of Materials (SBOMs) as a fundamental tool for this inventory process. SBOMs provide a detailed list of all the software components and their versions within a given application, enabling organizations to quickly identify their exposure to known vulnerabilities. Without this foundational understanding, effective risk mitigation becomes an exercise in guesswork. The roadmap stresses the importance of a centralized, dynamic inventory that can be continuously updated as software evolves and new vulnerabilities are discovered. This proactive approach moves beyond reactive patching and towards a more strategic risk management posture for OSS.
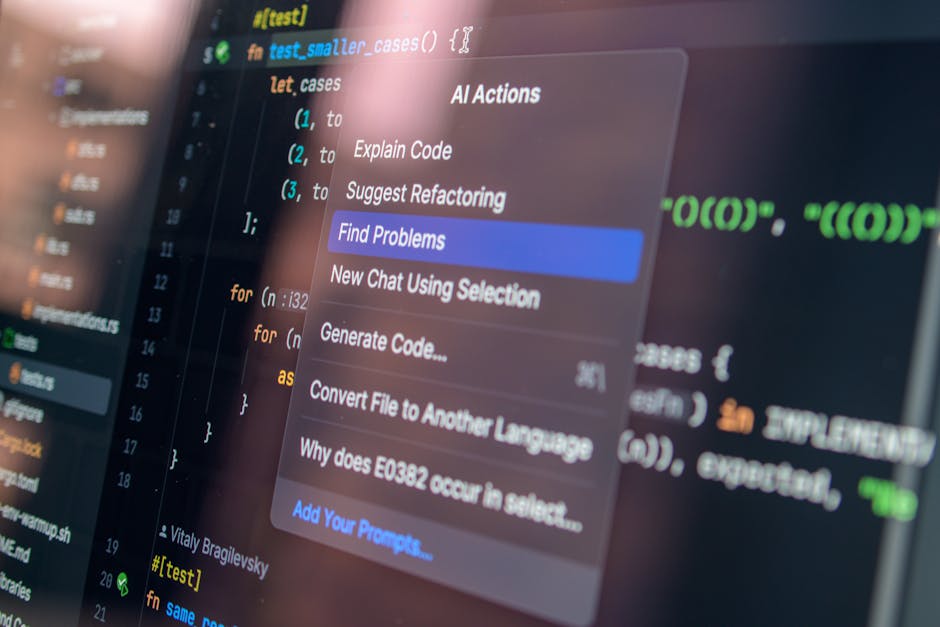
The second pillar, "Improving Secure Development Practices," focuses on embedding security throughout the entire software development lifecycle (SDLC) for OSS. This includes promoting secure coding standards, conducting rigorous security testing (static and dynamic analysis, fuzzing), and implementing robust vulnerability disclosure programs. CISA encourages the development and adoption of secure development checklists and best practices tailored for OSS projects. This pillar also highlights the need for enhanced supply chain security measures, such as verifying the integrity of code contributions and ensuring secure build environments. The concept of "secure by design" is central here, advocating for security to be a primary consideration from the initial design phases of an OSS project, rather than an afterthought. This involves educating developers on common security flaws and providing them with the tools and resources to prevent them. Furthermore, the roadmap emphasizes the importance of secure dependency management, ensuring that third-party libraries and components are themselves secure and regularly updated.
The third pillar, "Enhancing Vulnerability Management and Remediation," addresses the critical need for timely and effective identification, assessment, and mitigation of vulnerabilities in OSS. CISA proposes a more streamlined and collaborative approach to vulnerability reporting and remediation. This includes encouraging project maintainers to adopt structured vulnerability disclosure policies, providing clear channels for reporting, and establishing timelines for fixes. The roadmap also calls for improved tooling and automation to aid in vulnerability scanning and analysis across the vast landscape of OSS. A key aspect is fostering greater transparency around vulnerability disclosures, allowing downstream users to understand the risks and plan their remediation efforts. CISA aims to facilitate better communication between vulnerability researchers, OSS projects, and end-users to accelerate the patching process and reduce the window of exposure. This pillar also acknowledges the resource constraints faced by many OSS projects and explores potential mechanisms for supporting them in their security efforts.
The fourth pillar, "Strengthening Incident Response Capabilities," recognizes that despite best efforts, vulnerabilities will be discovered and exploited. This pillar focuses on improving the ability of organizations and OSS projects to respond effectively to security incidents. This includes developing clear incident response plans, establishing communication protocols for informing affected parties, and conducting post-incident analysis to identify lessons learned. CISA advocates for greater information sharing and collaboration during incidents, enabling a more coordinated and efficient response. The roadmap emphasizes the importance of having established playbooks for common OSS-related incident scenarios. This pillar also touches upon the need for resilient OSS infrastructure that can withstand and recover from attacks. The development of robust backup and recovery strategies, coupled with regular testing, is highlighted as essential for minimizing downtime and data loss.
The fifth pillar, "Fostering a Collaborative Security Culture," underscores that securing OSS is a shared responsibility. This pillar aims to encourage greater collaboration between OSS developers, users, researchers, and government agencies. CISA seeks to promote a culture where security is valued and integrated into the OSS ecosystem. This includes supporting training and education initiatives for OSS developers on security best practices, incentivizing contributions to OSS security, and facilitating open dialogue on security challenges. The roadmap emphasizes the importance of community building and knowledge sharing. CISA envisions a more proactive and engaged community that collectively works towards a more secure OSS future. This can involve funding for security-focused OSS initiatives, establishing best practice working groups, and creating platforms for ongoing discussion and knowledge exchange. The idea is to move away from silos and towards a more interconnected and mutually supportive OSS security environment.
A significant aspect of CISA’s roadmap is the focus on actionable steps and tangible outcomes. It’s not merely a theoretical document but a call to action for various stakeholders. For OSS developers and maintainers, this means prioritizing security in their development processes, adopting secure coding practices, and implementing robust vulnerability disclosure policies. For organizations that consume OSS, it translates to diligently tracking their OSS dependencies using SBOMs, conducting regular security assessments, and proactively updating vulnerable components. For security researchers, it encourages responsible disclosure of vulnerabilities and collaboration with OSS projects. For government agencies, it means leveraging their influence to promote OSS security standards, providing resources and support to OSS projects, and leading by example in their own use of OSS. The roadmap acknowledges that there is no single silver bullet and that a multi-pronged, collaborative approach is necessary for success.
The roadmap also delves into the importance of tooling and automation in enhancing OSS security. This includes the development and adoption of tools for automated code analysis, vulnerability scanning, dependency management, and SBOM generation. CISA recognizes that manual processes are often insufficient to keep pace with the complexity and scale of the OSS ecosystem. By promoting and supporting the development of effective security tools, CISA aims to empower developers and organizations to implement security measures more efficiently and effectively. This also includes encouraging the open-sourcing of security tools themselves, further contributing to the overall security posture of the OSS landscape. The integration of security testing into CI/CD pipelines is also a key recommendation, ensuring that security is continuously evaluated throughout the development process.
Furthermore, CISA’s roadmap addresses the critical need for improved metrics and measurement for OSS security. Without the ability to measure progress, it becomes difficult to assess the effectiveness of initiatives and identify areas for further improvement. CISA advocates for the development of standardized metrics to track vulnerability discovery rates, remediation times, adoption of secure development practices, and overall risk posture of OSS projects. This data-driven approach will enable informed decision-making and help prioritize resources effectively. Transparency in reporting these metrics will also foster accountability and encourage continuous improvement across the OSS ecosystem. The roadmap emphasizes that measurement is not about assigning blame but about identifying opportunities for collective advancement in security.
The roadmap also highlights the potential for leveraging government resources and expertise to support OSS security. This includes providing funding for critical OSS security projects, conducting research into emerging threats and vulnerabilities, and offering technical assistance to OSS projects facing security challenges. CISA aims to act as a catalyst, bringing together stakeholders and resources to address the most pressing OSS security issues. This can involve establishing public-private partnerships, supporting open-source security foundations, and facilitating the sharing of threat intelligence. The roadmap recognizes that government has a significant role to play in ensuring the security of the digital infrastructure that relies heavily on OSS.
Finally, CISA’s Open Source Security Roadmap is a living document, intended to evolve as the OSS landscape and threat environment change. It represents a commitment to the ongoing effort of securing the digital backbone of our society. By providing a clear vision and actionable strategy, CISA aims to foster a more secure, resilient, and trustworthy open-source ecosystem for the benefit of all. The success of this roadmap hinges on the active participation and collaboration of all stakeholders within the OSS community and beyond. Its comprehensive approach addresses the multifaceted challenges of OSS security, paving the way for a more fortified digital future. The roadmap’s emphasis on collaboration, transparency, and continuous improvement positions it as a vital framework for navigating the complex and ever-evolving world of open-source software security.