
Carbon Black vs CrowdStrike: Which Endpoint Security Solution is Right for You?
Carbon Black vs CrowdStrike – two titans in the endpoint security arena. Both offer powerful solutions to combat modern cyber threats, but each has its own strengths and weaknesses. Understanding the differences between these two industry leaders is crucial for any organization seeking robust endpoint protection.
This blog post will delve into a detailed comparison of Carbon Black and CrowdStrike, covering everything from their product offerings and technology to their market presence and customer support. We’ll explore the key factors to consider when choosing between these two solutions, helping you make the best decision for your unique security needs.
Carbon Black vs CrowdStrike: A Deep Dive
In the ever-evolving landscape of cybersecurity, Carbon Black and CrowdStrike stand as prominent players, offering robust endpoint protection solutions. While both companies share a common goal of safeguarding organizations against sophisticated threats, their approaches and capabilities differ significantly. Understanding these differences is crucial for businesses seeking the most effective security solution for their specific needs.
Key Areas of Competition
Carbon Black and CrowdStrike compete directly in several key areas, including:
- Endpoint Detection and Response (EDR):Both companies provide EDR solutions that monitor endpoint activity, detect malicious behavior, and enable rapid incident response.
- Threat Intelligence:Carbon Black and CrowdStrike leverage extensive threat intelligence feeds to proactively identify and mitigate emerging threats.
- Security Orchestration, Automation, and Response (SOAR):Both offer SOAR capabilities to streamline security workflows, automate tasks, and accelerate incident response.
- Cloud Security:As organizations increasingly adopt cloud-based services, both Carbon Black and CrowdStrike have expanded their offerings to secure cloud environments.
Product Offerings
Both Carbon Black and CrowdStrike are leading cybersecurity vendors, offering a wide range of products to protect organizations from various cyber threats. Their product portfolios are designed to address different aspects of endpoint security and threat detection and response.This section delves into the product offerings of Carbon Black and CrowdStrike, comparing and contrasting their features and functionalities.
It explores the strengths and weaknesses of each vendor’s products, providing insights into their key differentiators.
Carbon Black Products
Carbon Black offers a comprehensive endpoint security platform that includes several products designed to protect against various cyber threats. Its key product offerings include:
- Carbon Black Endpoint (CBE):CBE is a next-generation endpoint protection platform that combines endpoint detection and response (EDR), threat prevention, and vulnerability assessment capabilities. It leverages machine learning and behavioral analysis to identify and respond to malicious activities on endpoints.
- Carbon Black Cloud (CBC):CBC is a cloud-based security platform that provides a unified view of endpoint security data. It offers centralized management, reporting, and analytics capabilities, enabling organizations to gain insights into their security posture and respond to threats effectively.
- Carbon Black Response (CBR):CBR is a dedicated EDR solution that provides advanced threat hunting and incident response capabilities. It allows security teams to investigate suspicious activities, identify attackers, and remediate threats quickly.
- Carbon Black App Control:This product provides application whitelisting and control capabilities, restricting unauthorized applications from running on endpoints. It helps prevent malware from executing and reduces the attack surface.
CrowdStrike Products
CrowdStrike offers a cloud-native platform that provides a comprehensive suite of endpoint security products. Its core product offerings include:
- CrowdStrike Falcon:Falcon is a cloud-based endpoint protection platform that integrates various security capabilities, including EDR, threat prevention, and vulnerability management. It leverages a cloud-native architecture and artificial intelligence (AI) to detect and respond to threats in real time.
- CrowdStrike Falcon Prevent:Falcon Prevent provides endpoint protection capabilities, blocking known and unknown threats from accessing endpoints. It uses a combination of signature-based detection, behavioral analysis, and machine learning to prevent malicious activities.
- CrowdStrike Falcon Discover:Falcon Discover is a vulnerability management solution that identifies and prioritizes vulnerabilities across endpoints. It helps organizations assess their security posture and prioritize remediation efforts.
- CrowdStrike Falcon Insight:Falcon Insight is a threat intelligence and hunting platform that provides security teams with insights into malicious activities and potential threats. It uses a combination of AI, machine learning, and human expertise to identify and investigate suspicious behaviors.
Key Strengths and Weaknesses
Both Carbon Black and CrowdStrike offer strong endpoint security solutions, but they have different strengths and weaknesses:
Carbon Black Strengths:
- Strong EDR Capabilities:Carbon Black’s EDR solution, CBR, is highly regarded for its advanced threat hunting and incident response capabilities. It provides deep visibility into endpoint activities and enables security teams to investigate threats quickly and effectively.
- On-Premise Deployment Option:Carbon Black offers an on-premise deployment option, which can be advantageous for organizations with strict data residency requirements or concerns about cloud connectivity.
- Mature Technology:Carbon Black has been in the endpoint security market for a long time, and its technology is mature and well-established.
Carbon Black Weaknesses:
- Complexity:Carbon Black’s platform can be complex to manage, especially for organizations with limited security expertise.
- Limited Cloud Integration:While Carbon Black offers a cloud-based platform, its integration with other cloud security tools may be limited compared to CrowdStrike.
CrowdStrike Strengths:
- Cloud-Native Architecture:CrowdStrike’s cloud-native platform provides a scalable and flexible solution that can adapt to changing security needs.
- Strong AI and Machine Learning:CrowdStrike leverages advanced AI and machine learning capabilities to detect and respond to threats in real time. This helps the platform stay ahead of emerging threats and adapt to new attack techniques.
- Extensive Integrations:CrowdStrike integrates seamlessly with various cloud security tools and services, providing a comprehensive security solution.
CrowdStrike Weaknesses:
- Limited On-Premise Deployment:CrowdStrike primarily focuses on cloud-based deployments, which may not be suitable for all organizations.
- Higher Price Point:CrowdStrike’s pricing can be higher compared to Carbon Black, especially for large deployments.
Technology and Innovation

Both Carbon Black and CrowdStrike are industry leaders in endpoint security, continuously innovating to stay ahead of evolving cyber threats. They leverage cutting-edge technologies and approaches to provide comprehensive protection, threat detection, and response capabilities.
Choosing between Carbon Black and CrowdStrike is a tough call, especially with all the recent security news. It’s hard to ignore the google is in huge trouble over its billion dollar iphone deal story, which highlights the vulnerability of even the biggest tech giants.
So, when evaluating endpoint security solutions, we need to consider not only the features and pricing but also the vendor’s track record and overall security posture. Ultimately, the best choice depends on your specific needs and risk tolerance.
Endpoint Security Approaches
Carbon Black and CrowdStrike employ distinct approaches to endpoint security, each with its strengths and weaknesses.
- Carbon Blackutilizes a traditional agent-based approach, installing software on endpoints to monitor and control their behavior. This approach provides deep visibility into endpoint activities and allows for granular control over security policies. Carbon Black’s agents are lightweight and have minimal performance impact, making them suitable for various endpoint types.
- CrowdStrikerelies on a cloud-native approach, leveraging a lightweight agent and a powerful cloud platform for threat detection and response. This approach offers scalability, flexibility, and rapid deployment, enabling faster threat identification and remediation. CrowdStrike’s cloud platform centralizes data analysis and provides real-time insights into endpoint activity, facilitating proactive threat hunting and response.
Threat Detection and Response Capabilities
Both companies offer advanced threat detection and response capabilities, employing sophisticated technologies to identify and mitigate threats.
- Carbon Blackutilizes machine learning and behavioral analysis to detect suspicious activities and potential threats. Its endpoint detection and response (EDR) platform provides real-time visibility into endpoint activity, enabling security teams to investigate and respond to threats promptly. Carbon Black’s EDR platform also includes threat intelligence feeds and vulnerability management capabilities, further enhancing threat detection and response.
- CrowdStrikeleverages its Falcon platform, a cloud-native EDR solution that combines artificial intelligence (AI), machine learning, and threat intelligence to identify and respond to threats. CrowdStrike’s platform automatically detects and investigates suspicious activity, providing security teams with actionable insights and enabling rapid response.
Its cloud-based architecture ensures scalability and flexibility, enabling efficient threat detection and response across diverse environments.
Impact on the Cybersecurity Landscape, Carbon black vs crowdstrike
The innovative technologies and approaches employed by Carbon Black and CrowdStrike have significantly impacted the cybersecurity landscape.
- Enhanced Threat Detection and Response: Both companies’ solutions have significantly improved threat detection and response capabilities, enabling organizations to identify and mitigate threats more effectively. Their advanced technologies and cloud-based platforms provide real-time visibility into endpoint activity, allowing for faster threat identification and response.
- Shift towards Cloud-Native Security: CrowdStrike’s cloud-native approach has accelerated the shift towards cloud-based security solutions. This trend has led to increased adoption of cloud-native EDR platforms, offering scalability, flexibility, and rapid deployment advantages. Cloud-based security solutions also provide centralized data analysis and threat intelligence, enabling organizations to gain comprehensive insights into their security posture.
- Focus on Proactive Threat Hunting: Both companies emphasize proactive threat hunting, leveraging their advanced technologies and threat intelligence to identify and address potential threats before they can cause harm. This proactive approach has become increasingly crucial in today’s dynamic threat landscape, where attackers are constantly evolving their tactics.
Market Presence and Customer Base
Understanding the market presence and customer base of Carbon Black and CrowdStrike is crucial for evaluating their strengths and competitive landscape. Both companies cater to a diverse clientele, but their strategies and target segments differ.
Market Share and Customer Base
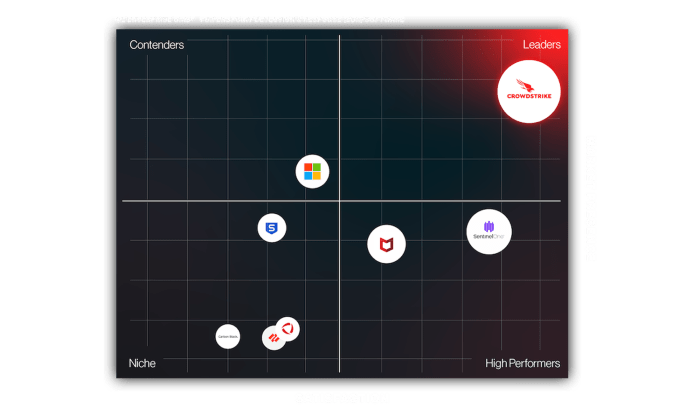
Carbon Black and CrowdStrike are major players in the endpoint security market, though their market share varies. According to Gartner, CrowdStrike holds a larger market share than Carbon Black, with a global presence and a significant customer base across various industries.
Carbon Black, while still a significant player, has a more focused approach and caters to specific customer segments.
Industry Verticals and Customer Segments
Both companies target a wide range of industry verticals, including:
- Financial Services
- Healthcare
- Government
- Manufacturing
- Retail
- Technology
However, their customer segmentation differs. CrowdStrike focuses on large enterprises, while Carbon Black targets a broader range of businesses, including mid-sized companies and smaller organizations.
Competitive Advantages and Challenges
- CrowdStrike’s competitive advantage lies in its cloud-native platform, which offers scalability, agility, and rapid deployment. It also boasts a strong brand reputation and a robust threat intelligence network. However, its high pricing and reliance on a subscription model may pose challenges for some organizations.
- Carbon Black, on the other hand, offers a more flexible pricing model and a wider range of deployment options, including on-premises and cloud-based solutions. Its focus on endpoint security and threat prevention provides a strong value proposition. However, its technology might be perceived as less innovative compared to CrowdStrike’s cloud-based platform.
Pricing and Value Proposition
Both Carbon Black and CrowdStrike offer robust security solutions, but their pricing models and value propositions differ significantly. Understanding these differences is crucial for businesses to make informed decisions based on their specific needs and budgets.
Pricing Models
The pricing models of Carbon Black and CrowdStrike vary, reflecting their distinct product offerings and target customer segments.
- Carbon Blackprimarily utilizes a per-endpoint pricing model. This means that customers pay a fixed price for each device protected by the solution. This model is straightforward and predictable, making it suitable for organizations with a clear understanding of their endpoint inventory.
- CrowdStrike, on the other hand, employs a subscription-based modelthat encompasses a range of services, including endpoint protection, threat intelligence, and incident response. This model offers flexibility, allowing customers to choose the features they need and pay accordingly.
Value Proposition
The value proposition of each solution depends on factors such as the size and complexity of the organization, the specific security challenges faced, and the desired level of protection.
- Carbon Blackemphasizes comprehensive endpoint securitywith a focus on prevention, detection, and response. Its strong endpoint protection capabilities make it a suitable choice for organizations seeking to bolster their defenses against sophisticated threats.
- CrowdStrikeprioritizes cloud-native securityand threat intelligence. Its focus on real-time threat detection and rapid response makes it a compelling option for organizations looking to mitigate the impact of advanced cyberattacks.
Cost-Benefit Analysis
The cost-benefit analysis of Carbon Black and CrowdStrike involves considering the following factors:
- Initial Investment: Carbon Black’s per-endpoint pricing model can lead to a higher initial investment, especially for large organizations. CrowdStrike’s subscription-based model might be more cost-effective in the short term, depending on the chosen features.
- Ongoing Costs: Both solutions have recurring costs associated with maintenance, updates, and support. The long-term cost implications should be carefully evaluated.
- Return on Investment (ROI): The value proposition of each solution should be assessed in terms of its ability to prevent security breaches, reduce downtime, and minimize the financial impact of cyberattacks.
Key Decision-Making Factors
Several key factors influence the decision-making process for customers:
- Security Needs: Organizations with stringent security requirements and a high tolerance for risk might prefer Carbon Black’s comprehensive endpoint protection. Organizations with a strong focus on cloud security and threat intelligence might find CrowdStrike’s capabilities more aligned with their needs.
- Budget: The initial investment and ongoing costs of each solution should be considered within the context of the organization’s budget.
- Technical Expertise: The level of technical expertise within the organization can impact the ease of deployment and management of each solution.
- Scalability: Both solutions offer scalability, but their capabilities might differ depending on the size and complexity of the organization’s infrastructure.
Deployment and Integration

The deployment and integration of security solutions are crucial factors for organizations, impacting their ability to quickly and effectively implement protections. This section delves into the deployment models and integration capabilities of Carbon Black and CrowdStrike, highlighting their ease of implementation, compatibility with existing infrastructure, and potential challenges.
Deployment Models
The deployment models of Carbon Black and CrowdStrike differ significantly, offering organizations flexibility in choosing the approach that best suits their needs.
Choosing between Carbon Black and CrowdStrike for endpoint security can be a tough call, especially when considering the various features and pricing models. But let’s take a quick break from that decision and talk about something exciting – the upcoming OLED iPad Pro bezels are the thinnest pro models have ever been and a new matte finish option is on the way ! Back to Carbon Black vs.
CrowdStrike, ultimately, the best choice depends on your specific needs and budget. Both offer robust protection, so it’s important to carefully evaluate their strengths and weaknesses before making a decision.
- Carbon Black:Carbon Black offers a variety of deployment options, including agent-based, sensor-based, and cloud-based deployments. Agent-based deployments involve installing agents on endpoints, providing real-time threat detection and response. Sensor-based deployments use sensors to monitor network traffic and identify malicious activity.
Cloud-based deployments leverage the cloud to provide centralized management and analysis of endpoint data.
- CrowdStrike:CrowdStrike primarily focuses on cloud-based deployments, relying on lightweight agents that communicate with the CrowdStrike Falcon platform in the cloud. This approach eliminates the need for on-premises infrastructure, simplifying deployment and management.
Integration Capabilities
Both Carbon Black and CrowdStrike offer robust integration capabilities, enabling seamless integration with existing security tools and workflows.
- Carbon Black:Carbon Black boasts a wide range of integrations with popular security information and event management (SIEM) systems, threat intelligence platforms, and other security tools. This allows organizations to consolidate security data and automate incident response processes.
- CrowdStrike:CrowdStrike also offers extensive integration capabilities, supporting integrations with leading SIEMs, orchestration and automation platforms, and other security tools. These integrations enhance the effectiveness of CrowdStrike’s platform by providing comprehensive threat visibility and automated response capabilities.
Ease of Implementation
The ease of implementation varies between Carbon Black and CrowdStrike, depending on the chosen deployment model and existing infrastructure.
- Carbon Black:While Carbon Black’s agent-based deployments require agent installation on endpoints, the process is generally straightforward and well-documented. However, deploying sensors can be more complex, requiring network configuration and potentially impacting network performance.
- CrowdStrike:CrowdStrike’s cloud-based approach simplifies implementation, as it eliminates the need for on-premises infrastructure and reduces the complexity of deployment. The lightweight agents are easy to install and require minimal configuration.
Compatibility with Existing Infrastructure
Compatibility with existing infrastructure is crucial for seamless integration and minimal disruption to operations.
Choosing between Carbon Black and CrowdStrike can feel like picking a favorite superhero. Both are powerful, but their strengths lie in different areas. It’s exciting to think that Apple might be preparing to take on the laptop market with their iPad, as described in this article, future ipad updates could add powerful new mac like features over the next two years apples tablet again sets its sights on replacing your laptop.
If that happens, maybe we’ll see a new wave of security solutions tailored specifically for iPad-based workflows, perhaps even a Carbon Black or CrowdStrike version!
- Carbon Black:Carbon Black offers good compatibility with various operating systems, including Windows, macOS, and Linux. However, compatibility with specific hardware and software configurations may require additional considerations.
- CrowdStrike:CrowdStrike also supports a wide range of operating systems, including Windows, macOS, and Linux. The cloud-based architecture further enhances compatibility, as it eliminates the need for specific hardware or software dependencies.
Challenges and Considerations
Deployment and integration of security solutions can present challenges and considerations for organizations.
- Performance Impact:Agent-based deployments, such as those offered by Carbon Black, can potentially impact endpoint performance. It’s important to carefully consider the impact of agents on resource utilization and ensure that they do not hinder critical operations.
- Network Complexity:Deploying sensors, as used in Carbon Black’s sensor-based deployments, can introduce complexity to network infrastructure. Careful planning and configuration are essential to ensure that sensor deployments do not interfere with network performance or security.
- Cloud Dependency:CrowdStrike’s reliance on cloud-based infrastructure can raise concerns about data privacy and security. Organizations need to carefully assess the cloud provider’s security measures and ensure that their data is adequately protected.
- Integration Complexity:Integrating security solutions with existing tools and workflows can be complex and time-consuming. Organizations should carefully consider the integration process, including the required configurations, data mapping, and potential compatibility issues.
Security Posture and Threat Intelligence
Both Carbon Black and CrowdStrike offer robust security posture and threat intelligence capabilities. These features are critical for organizations to proactively identify, prevent, and respond to evolving cyber threats.
Threat Detection and Prevention
Carbon Black and CrowdStrike employ distinct approaches to threat detection and prevention, each leveraging unique technologies and methodologies.
- Carbon Black: Carbon Black’s endpoint protection platform (EPP) focuses on endpoint security and leverages its signature-based and behavioral analysis techniques to detect and prevent malware. It excels in detecting known threats and suspicious activities. Carbon Black’s approach is primarily focused on preventing known attacks and protecting against common threats.
- CrowdStrike: CrowdStrike’s endpoint detection and response (EDR) solution, Falcon, utilizes a cloud-native approach, relying heavily on machine learning and artificial intelligence (AI) to detect and prevent threats. Its ability to analyze and correlate data from multiple endpoints, coupled with its real-time threat intelligence feeds, enables proactive threat hunting and rapid response.
CrowdStrike’s approach emphasizes proactive threat hunting and prevention, utilizing AI to detect and respond to emerging and unknown threats.
Threat Intelligence
Both vendors provide access to threat intelligence feeds and resources to enhance their security posture.
- Carbon Black: Carbon Black offers a comprehensive threat intelligence platform that provides access to threat indicators, attack patterns, and vulnerability information. It also integrates with various third-party intelligence feeds to enrich its threat detection capabilities. Carbon Black’s approach to threat intelligence focuses on providing actionable insights and threat context to help organizations make informed security decisions.
- CrowdStrike: CrowdStrike’s Falcon platform integrates with its global threat intelligence network, providing real-time insights into emerging threats and attack trends. This network leverages data from millions of endpoints and continuously monitors for new attack vectors and malicious activity. CrowdStrike’s approach emphasizes real-time threat intelligence and proactive threat hunting, enabling rapid detection and response to emerging threats.
Remediation and Response
Both Carbon Black and CrowdStrike provide capabilities for threat remediation and response.
- Carbon Black: Carbon Black’s EPP platform offers tools for isolating infected endpoints, removing malware, and restoring system integrity. Its focus is on containing threats and restoring affected systems to a secure state. Carbon Black’s approach to remediation emphasizes isolation and containment, preventing further damage and facilitating recovery.
- CrowdStrike: CrowdStrike’s Falcon platform provides a comprehensive suite of tools for threat investigation, response, and remediation. Its cloud-native architecture allows for rapid response and remediation actions, including containment, isolation, and eradication of threats. CrowdStrike’s approach to remediation emphasizes proactive threat hunting, rapid response, and automated remediation actions, minimizing the impact of cyberattacks.
Effectiveness in Addressing Evolving Cyber Threats
Both Carbon Black and CrowdStrike continuously evolve their solutions to address emerging threats and attack techniques.
- Carbon Black: Carbon Black regularly updates its threat intelligence feeds, signature databases, and behavioral analysis models to stay ahead of evolving threats. Its focus on known threats and suspicious activities makes it effective in addressing traditional malware and exploit-based attacks.
Carbon Black’s approach is well-suited for organizations that require robust protection against known threats and common attack vectors.
- CrowdStrike: CrowdStrike’s AI-powered threat detection and response capabilities enable it to adapt to new threats and attack techniques. Its cloud-native architecture allows for rapid updates and continuous improvement of its threat intelligence and detection models. CrowdStrike’s approach is particularly effective in addressing emerging threats, zero-day exploits, and advanced attack techniques.
Customer Support and Services
Both Carbon Black and CrowdStrike are recognized for their robust customer support and services, aiming to provide a comprehensive experience for their clients. This section will delve into their offerings, focusing on the quality and responsiveness of their support channels, as well as the availability of training and resources for customers.
Support Channels and Responsiveness
Both vendors offer a range of support channels to cater to diverse customer needs. These channels typically include:
- Phone Support:Both Carbon Black and CrowdStrike provide 24/7 phone support, ensuring immediate assistance for critical issues.
- Email Support:Customers can reach out to support teams via email for non-urgent inquiries or for detailed explanations.
- Online Support Portals:Both vendors maintain comprehensive online support portals, providing access to knowledge bases, FAQs, and troubleshooting guides. These portals often include community forums where users can interact with each other and share experiences.
- Live Chat:CrowdStrike offers live chat support, allowing for real-time interactions with support agents. This feature is particularly useful for quick queries and immediate assistance.
In terms of responsiveness, both vendors strive for prompt resolutions. However, CrowdStrike’s live chat feature provides a more immediate response compared to Carbon Black’s reliance on email and phone support for initial interactions.
Training and Resources
Both Carbon Black and CrowdStrike prioritize customer education and provide comprehensive training and resources to empower users.
- On-demand Training:Both vendors offer a wide array of on-demand training materials, including videos, tutorials, and documentation, covering various aspects of their products and services. These resources are accessible through their online portals and learning management systems.
- Live Webinars:Both vendors conduct regular live webinars, covering new product features, best practices, and industry trends. These webinars provide opportunities for interactive learning and Q&A sessions.
- In-person Training:Both vendors offer in-person training courses, allowing for hands-on experience and deeper engagement with their products. These courses are typically available at various locations or on-site at customer premises.
- Professional Services:Both Carbon Black and CrowdStrike provide professional services, including implementation assistance, custom configurations, and ongoing support. These services are particularly valuable for complex deployments and customized security solutions.
While both vendors offer comprehensive training and resources, CrowdStrike’s focus on continuous learning and its extensive library of on-demand materials may provide a slight edge in terms of accessibility and flexibility.
Future Outlook
Both Carbon Black and CrowdStrike are well-positioned to capitalize on the growing demand for robust cybersecurity solutions. The future holds significant opportunities for both companies, driven by the evolving threat landscape and the adoption of emerging technologies.
Impact of Emerging Technologies and Trends
The rapid evolution of technology presents both challenges and opportunities for cybersecurity vendors. Artificial intelligence (AI), machine learning (ML), and automation are transforming the way organizations approach security.
- AI and ML are playing an increasingly important role in threat detection and response. These technologies can analyze vast amounts of data to identify suspicious activities and predict potential attacks. Both Carbon Black and CrowdStrike are investing heavily in AI and ML capabilities to enhance their platform’s effectiveness.
For instance, CrowdStrike’s Falcon platform leverages AI to detect and respond to threats in real-time, while Carbon Black’s CB Predictive Security uses AI to identify and prioritize vulnerabilities.
- The rise of cloud computing and the adoption of Software-as-a-Service (SaaS) models have also significantly impacted the cybersecurity landscape. Cloud-based security solutions offer several advantages, such as scalability, flexibility, and reduced infrastructure costs. Both Carbon Black and CrowdStrike have embraced the cloud, offering their solutions as SaaS platforms.
Carbon Black’s Cloud Workload Protection Platform (CWPP) provides comprehensive security for cloud workloads, while CrowdStrike’s Falcon platform offers cloud-native protection for various cloud environments, including AWS, Azure, and Google Cloud.
- The increasing adoption of Internet of Things (IoT) devices and the growing interconnectedness of businesses have created new security challenges. IoT devices often lack robust security features, making them vulnerable to attacks. Both Carbon Black and CrowdStrike are expanding their offerings to address the security needs of IoT devices.
For example, CrowdStrike’s Falcon platform includes IoT security capabilities, while Carbon Black offers solutions for securing industrial control systems (ICS).
Key Factors Shaping Future Success
Several key factors will shape the future success of Carbon Black and CrowdStrike:
- Innovation and R&D:Continued investment in research and development will be crucial for both companies to stay ahead of the curve in the ever-evolving cybersecurity landscape. This includes developing new technologies, enhancing existing products, and staying ahead of emerging threats.
- Strategic Partnerships:Forming strategic partnerships with other technology providers, such as cloud service providers and managed security service providers (MSSPs), will enable both companies to expand their reach and offer more comprehensive solutions. This also allows for greater integration and interoperability across different security tools and platforms.
- Customer Focus:Providing excellent customer support and services will be critical to retaining existing customers and attracting new ones. This includes offering personalized support, providing timely updates and patches, and ensuring seamless integration with existing IT infrastructure.
- Talent Acquisition and Retention:Attracting and retaining top cybersecurity talent will be essential for both companies to maintain their competitive edge. This requires offering competitive salaries and benefits, providing opportunities for professional development, and fostering a positive and supportive work environment.







