Cybersecurity
-

Blast Radius Vulnerability: Understanding the Impact and Mitigation
Blastradius vulnerability radius protocol – Blast radius vulnerability radius protocol sets the stage for this enthralling narrative, offering readers a…
Read More » -

Akamai Report: LockBit & Cl0p Expand Ransomware Efforts
Akamai report lockbit cl0p expand ransomware efforts – Akamai Report: LockBit & Cl0p Expand Ransomware Efforts – the title itself…
Read More » -

ISC2 Cybersecurity AI Survey: A Look at the Future of Security
The ISC2 Cybersecurity AI Survey takes a deep dive into the evolving landscape of cybersecurity, exploring the growing influence of…
Read More » -

Europe Malware Enforcement Op: Combating Cybercrime
Europe Malware Enforcement Op sets the stage for this enthralling narrative, offering readers a glimpse into a story that is…
Read More » -

Nine Ethical Hacking Courses: Your Path to Cybersecurity
Nine ethical hacking courses offer a gateway to the fascinating world of cybersecurity. As technology continues to evolve, the need…
Read More » -

Okta Customer Identity Trends: Shaping the Future of Security and Experience
Okta customer identity trends are reshaping how organizations approach security and customer experience. In a world where data breaches are…
Read More » -
Ransomware Gangs Harassment Victims Increasing: A Growing Threat
Ransomware gangs harassment victims increasing is a disturbing trend that’s escalating rapidly. These cybercriminals are no longer content with simply…
Read More » -

Cyber Security Tips for Business Travelers
Cyber security tips business travel – Cyber Security Tips for Business Travelers: In today’s interconnected world, business travel is a…
Read More » -
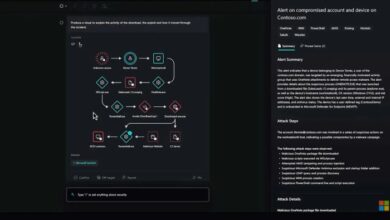
Microsoft Security Copilot Experience Center: Your Security Ally
Microsoft Security Copilot Experience Center is your one-stop shop for comprehensive security solutions, empowering you to navigate the complex world…
Read More »



