Why Antivirus Programs Are Now the Problem, Not the Solution
Why antivirus programs have become the problem not the solution is a question that has been circulating in the cybersecurity community for a while now. As cyber threats evolve and become more sophisticated, traditional antivirus programs struggle to keep pace, leaving our digital lives vulnerable.
The truth is, antivirus programs are no longer enough to protect us from the latest cyber threats. They’re designed to identify and remove known threats, but they can’t keep up with the rapid pace of malware development. This leaves us exposed to new and emerging threats that can bypass traditional defenses.
Limitations of Traditional Antivirus Solutions

Traditional antivirus solutions, while playing a crucial role in cybersecurity for decades, face significant limitations in the face of modern cyber threats. These limitations stem from their reliance on signature-based detection methods, which struggle to keep pace with the rapid evolution of malware and the emergence of new attack vectors.
It’s ironic, isn’t it? Antivirus programs were supposed to be our saviors, but they’ve become more like the virus themselves, slowing down our systems and hindering productivity. Perhaps the answer lies in understanding how to leverage collaborative platforms like Confluence, which can streamline workflows and foster a more efficient environment.
Learn more about what Confluence is and why it’s beneficial for businesses. By embracing these modern tools, we can move beyond the limitations of traditional antivirus programs and create a more secure and efficient digital landscape.
Signature-Based Detection Limitations, Why antivirus programs have become the problem not the solution
Signature-based detection is the cornerstone of traditional antivirus programs. This method relies on identifying known malware by comparing its unique characteristics, known as signatures, to a database of known threats. While effective against known malware, this approach has inherent limitations.
Antivirus programs, once our digital guardians, are now often part of the problem. They slow down our devices, drain our batteries, and sometimes even conflict with legitimate software. The future, however, looks brighter with the advent of google passkeys chrome android , a more secure and seamless way to log in.
By shifting focus from constant scanning to a more proactive approach, we can leave the days of bulky antivirus software behind and embrace a truly secure digital experience.
- Limited Effectiveness Against Zero-Day Threats:Signature-based detection struggles against zero-day threats, which are new malware variants not yet identified and added to antivirus databases. These threats can exploit vulnerabilities before security patches are available, making them particularly dangerous.
- False Positives:Signature-based detection can lead to false positives, where legitimate files are incorrectly flagged as malicious. This can disrupt workflows and cause unnecessary stress for users.
- Malware Polymorphism:Malware authors employ techniques like polymorphism to obfuscate their creations, making them difficult to detect by signature-based methods. Polymorphic malware can alter its code structure without changing its functionality, evading traditional antivirus solutions.
Keeping Up with Rapid Malware Evolution
The rapid evolution of malware poses a significant challenge for traditional antivirus solutions. Malware authors constantly adapt their techniques, creating new variants and exploiting emerging vulnerabilities.
Antivirus programs, once our digital saviors, are now often the source of the problem. They bog down our systems with constant updates and resource-intensive scans, while still failing to catch the latest threats. It’s like trying to secure your valuables in a flimsy lockbox when you could be storing them in a much more secure location, like elsies super secret storage cabinet.
Instead of relying on outdated technology, we need to embrace a more proactive approach to cybersecurity, focusing on user education and robust security practices.
- Exploiting New Vulnerabilities:Malware authors often exploit newly discovered vulnerabilities in software, hardware, or operating systems. Antivirus programs need to update their databases quickly to detect and mitigate these threats.
- Emerging Malware Families:New malware families, with unique attack vectors and obfuscation techniques, emerge regularly. Antivirus programs must adapt to these new threats, requiring constant updates and improvements to their detection engines.
- Malware Delivery Mechanisms:Malware authors employ diverse delivery mechanisms, such as phishing emails, malicious websites, and exploit kits, to distribute their creations. Traditional antivirus solutions need to be vigilant in identifying and blocking these delivery channels.
Challenges in Detecting Fileless Attacks and Memory-Based Attacks
Fileless attacks and memory-based attacks pose significant challenges for traditional antivirus solutions. These attacks do not rely on malicious files but instead exploit system vulnerabilities or manipulate legitimate processes to achieve their objectives.
- Fileless Attacks:Fileless attacks leverage legitimate system tools or scripts to execute malicious code directly in memory, bypassing traditional file-based antivirus scanning. These attacks are often difficult to detect as they do not involve the creation of malicious files.
- Memory-Based Attacks:Memory-based attacks, also known as in-memory attacks, target the computer’s memory, bypassing traditional file-based antivirus solutions. These attacks can inject malicious code into legitimate processes, making them difficult to detect and prevent.
The Rise of Endpoint Detection and Response (EDR): Why Antivirus Programs Have Become The Problem Not The Solution
Traditional antivirus solutions, while offering some protection, are struggling to keep up with the ever-evolving landscape of cyber threats. This has led to the emergence of Endpoint Detection and Response (EDR), a more advanced approach to cybersecurity that provides comprehensive protection against modern attacks.
EDR’s Advantages Over Traditional Antivirus
EDR solutions offer several advantages over traditional antivirus programs. They go beyond signature-based detection, which relies on identifying known threats, to actively monitor and analyze endpoint behavior, enabling them to identify and respond to previously unknown threats.
- Proactive Threat Detection:EDR solutions utilize behavioral analysis and machine learning to detect suspicious activities, such as unusual file access patterns or network communication, that might indicate a malicious attack. This proactive approach allows for early detection and response, minimizing the impact of attacks.
- Comprehensive Threat Visibility:EDR provides a centralized view of all endpoint activity, enabling security teams to monitor and analyze data from multiple sources, including system logs, network traffic, and user behavior. This comprehensive visibility allows for a more holistic understanding of threats and their impact.
- Automated Incident Response:EDR solutions can automate threat response actions, such as isolating infected endpoints, quarantining malicious files, or blocking suspicious connections. This automation streamlines the incident response process, minimizing human intervention and reducing the time to contain threats.
- Improved Security Posture:By providing detailed insights into endpoint activity and threat behavior, EDR enables security teams to identify vulnerabilities and improve their overall security posture. This proactive approach helps organizations stay ahead of emerging threats and reduce their risk of cyberattacks.
EDR’s Use of Behavioral Analysis and Machine Learning
EDR solutions employ advanced techniques to detect and respond to threats, including behavioral analysis and machine learning.
- Behavioral Analysis:EDR solutions continuously monitor endpoint activity and analyze patterns in user behavior, system processes, and network communication. They identify deviations from normal behavior, such as unusual file access patterns or attempts to connect to known malicious servers, as potential indicators of compromise.
- Machine Learning:EDR leverages machine learning algorithms to analyze vast amounts of data and identify patterns that might indicate malicious activity. These algorithms learn from historical data and adapt to new threats, enabling EDR solutions to detect and respond to previously unknown attacks.
EDR’s Effectiveness in Identifying and Remediating Advanced Attacks
EDR solutions are particularly effective in identifying and remediating advanced attacks, such as targeted attacks and zero-day exploits. These attacks often bypass traditional antivirus defenses by using novel techniques that are not yet known to signature-based solutions.
- Targeted Attacks:EDR solutions can detect and respond to targeted attacks, such as phishing campaigns and malware delivered through social engineering, by analyzing user behavior and network traffic. They can identify suspicious emails, websites, or downloads that might indicate a targeted attack and take appropriate action to prevent infection.
- Zero-Day Exploits:EDR solutions can detect and respond to zero-day exploits, which target vulnerabilities that have not yet been patched, by analyzing system behavior and identifying suspicious activity that might indicate exploitation. They can isolate infected endpoints, block malicious communication, and remediate the exploit before it can cause significant damage.
Examples of EDR in Action
EDR solutions have been instrumental in identifying and remediating advanced attacks in real-world scenarios.
- The NotPetya Ransomware Attack:EDR solutions helped organizations identify and contain the NotPetya ransomware attack, which spread rapidly across the globe in 2017. By analyzing network traffic and endpoint behavior, EDR solutions were able to identify infected systems and isolate them from the network, preventing further spread of the ransomware.
- The WannaCry Ransomware Attack:EDR solutions played a crucial role in mitigating the WannaCry ransomware attack, which exploited a vulnerability in Microsoft Windows. EDR solutions were able to identify and block the exploit before it could cause widespread damage, helping organizations protect their systems and data.
The Role of User Awareness and Best Practices
The most effective security solution is a combination of technology and user awareness. Even the most robust antivirus software can be bypassed if users fall prey to common phishing scams or unknowingly download malicious files. It is essential to educate users about the evolving threat landscape and equip them with the necessary knowledge and skills to protect themselves and their organizations.
User Behaviors Contributing to Security Vulnerabilities
User behavior plays a significant role in security breaches. Unintentional actions or a lack of awareness can create vulnerabilities that malicious actors can exploit. Here are some common user behaviors that can lead to security incidents:
- Clicking on suspicious links:Users often click on links in emails or messages from unknown senders, leading to malware infections. This is a common tactic used in phishing attacks, where attackers try to trick users into revealing sensitive information or downloading malicious software.
- Opening attachments from unknown senders:Similar to clicking on suspicious links, opening attachments from unknown senders can expose systems to malware. Attackers often disguise malicious files as legitimate documents, presentations, or spreadsheets to deceive users.
- Using weak passwords:Choosing easy-to-guess passwords or using the same password across multiple accounts can make it easier for attackers to gain access to systems and data. Strong passwords should be at least 12 characters long and include a combination of uppercase and lowercase letters, numbers, and symbols.
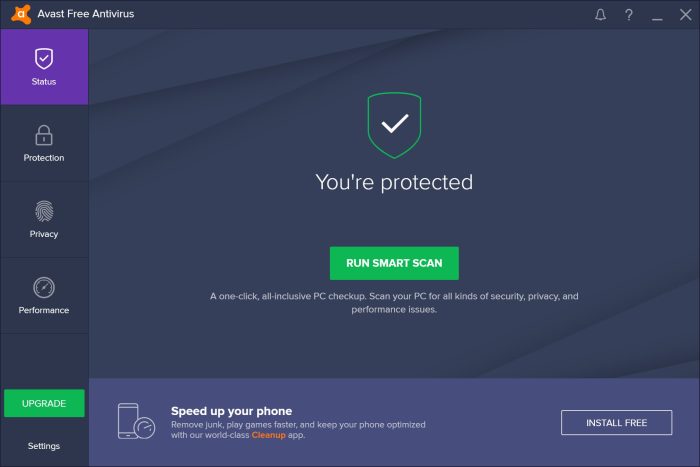
- Ignoring security warnings:Users may ignore security warnings from their antivirus software or web browser, thinking they are false positives. These warnings are often legitimate and should be taken seriously.
- Downloading software from untrusted sources:Downloading software from untrusted sources, such as cracked or pirated websites, can expose systems to malware. Always download software from reputable vendors and verify the authenticity of the source.
- Sharing sensitive information on public Wi-Fi:Public Wi-Fi networks are often unsecured, making it easy for attackers to intercept sensitive information, such as login credentials or financial data. Avoid accessing sensitive information on public Wi-Fi networks.
- Failing to update software:Software updates often include security patches that fix vulnerabilities that could be exploited by attackers. Regularly updating software is crucial for maintaining system security.







