Epic Games Ceo Calls Apple Find My Super Creepy Surveillance Tech That Shouldnt Exist


Epic Games CEO Calls Apple’s Find My "Super Creepy Surveillance Tech" That Shouldn’t Exist
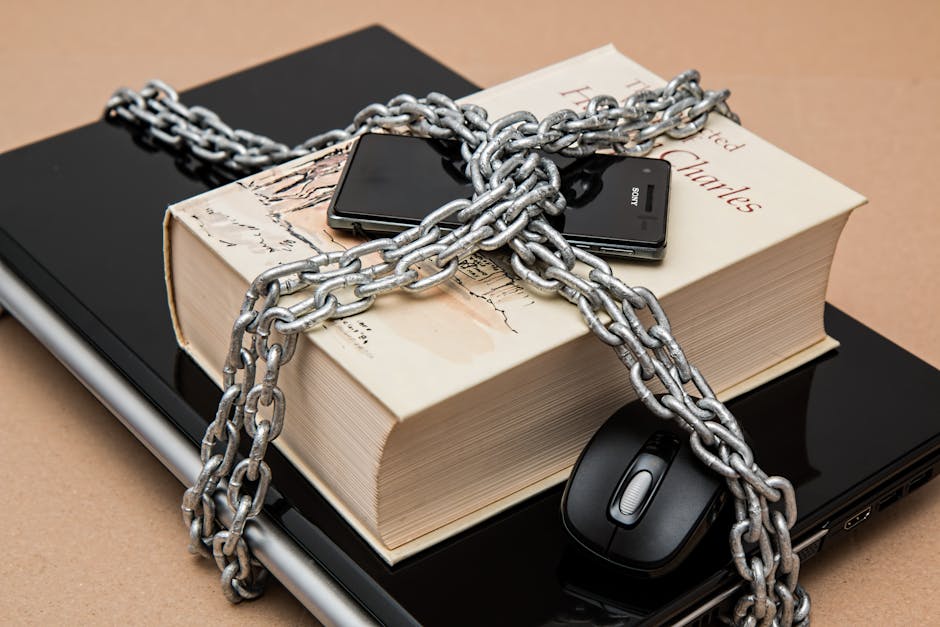
The assertion by Epic Games CEO Tim Sweeney that Apple’s "Find My" service constitutes "super creepy surveillance tech" that "shouldn’t exist" has ignited a fierce debate within the tech industry and among consumers. This strong condemnation, delivered directly from the head of a company locked in a protracted legal battle with Apple, raises critical questions about privacy, device functionality, and the broader implications of ubiquitous location tracking. Sweeney’s pronouncements are not merely rhetorical flourishes; they reflect a deep-seated concern over the power Apple wields through its integrated ecosystem and the potential for misuse, even if unintended, of the data generated by its services. Understanding the gravity of these claims requires a thorough examination of the "Find My" network, its technical underpinnings, Apple’s stated privacy protections, and the arguments put forth by critics like Sweeney.
At its core, the "Find My" network is designed to help users locate lost or stolen Apple devices. It leverages a vast, crowdsourced network of hundreds of millions of Apple devices worldwide. When a device is offline, it can still be located by sending out a Bluetooth signal. This signal is detected by nearby Apple devices, which then anonymously and securely relay the location of the lost device back to its owner. This ingenious, albeit controversial, system operates in the background, requiring no active participation from the users whose devices are contributing to the network. The privacy architecture, as described by Apple, is built upon end-to-end encryption. This means that only the owner of the lost device can see its location. Apple itself, and any third party, is purportedly unable to access this information. Each device participating in the network is assigned a rotating public key, ensuring that even if a device’s location is intercepted, it cannot be linked back to the original owner without their private key. Furthermore, the Bluetooth signal is encrypted and does not contain personally identifiable information, aiming to prevent unauthorized tracking of individuals.
However, the sheer scale and interconnectedness of the "Find My" network are precisely what fuel Sweeney’s alarm. He argues that the ability of a single entity, Apple, to possess the infrastructure that can pinpoint the location of millions of devices, even if ostensibly anonymized and encrypted, presents an inherent risk. The argument is not necessarily that Apple is actively conducting mass surveillance, but rather that the potential for such surveillance, or for data breaches that could compromise this sensitive information, is too great. This perspective aligns with broader concerns about the consolidation of power and data in the hands of major tech corporations. From this viewpoint, the "Find My" network represents an unprecedented level of passive data collection and a powerful tool for tracking individuals, regardless of their intent. The "creepy" aspect, as Sweeney describes it, stems from the idea that your location is constantly being broadcast and, in theory, could be aggregated and analyzed, even if Apple insists it isn’t.
The context of Epic Games’ ongoing dispute with Apple is crucial to understanding Sweeney’s vocal criticism. Epic has accused Apple of monopolistic practices regarding its App Store, particularly its requirement for developers to use Apple’s in-app purchase system, which incurs a commission. Sweeney and Epic have argued that this creates an unfair marketplace and stifles competition. The "Find My" critique can be seen as an extension of this broader challenge to Apple’s control and its perceived exploitative business model. By labeling "Find My" as surveillance tech, Sweeney is attempting to frame Apple’s core services in a negative light, potentially influencing public perception and regulatory scrutiny. This is a strategic maneuver designed to amplify his company’s anti-Apple stance by highlighting what he portrays as a privacy transgression.
Beyond the privacy arguments, there are also technical and ethical considerations regarding consent and transparency. While users opt into "Find My" when setting up their Apple devices, the passive nature of its network functionality means that individuals whose devices are not lost are still contributing to the system without explicit, ongoing consent for each location ping. The argument is that the broad collection of location data, even when anonymized, creates a profile of movement and association that could be valuable to malicious actors or even to governments under certain circumstances. The "shouldn’t exist" sentiment suggests that some technological capabilities, regardless of their purported benefits, may cross an ethical boundary due to their inherent potential for misuse. This is a philosophical argument about technological determinism and the responsibility of creators to anticipate and mitigate negative societal impacts.
Apple, of course, vehemently defends "Find My," emphasizing its user-centric design and robust privacy safeguards. They highlight that the system is opt-in and that users have control over location sharing settings. The company consistently promotes its commitment to privacy as a cornerstone of its product philosophy, differentiating itself from competitors who they argue monetize user data more directly. Apple points to the fact that the location data is end-to-end encrypted and that the network is designed to be decentralized, meaning no single entity has access to a comprehensive map of all device locations. The Bluetooth signals are short-range and encrypted, making them difficult to intercept and even harder to decipher. Furthermore, Apple argues that the benefits of "Find My" – reuniting people with their lost belongings, deterring theft, and even aiding in emergency situations – far outweigh the hypothetical risks. The ability to track a stolen iPhone, for example, can be instrumental in its recovery and in the apprehension of criminals.
The debate over "Find My" is not monolithic. There are valid points on both sides. The technological innovation behind the crowdsourced network is undeniable, offering a powerful solution for a common problem. However, Sweeney’s concerns about the potential for mass surveillance, the erosion of privacy in an increasingly connected world, and the concentration of power in the hands of a few tech giants are equally legitimate. The "super creepy" label, while provocative, resonates with a growing public unease about how personal data is collected, used, and potentially exposed. The fact that this criticism comes from the CEO of a company in direct conflict with Apple adds a layer of strategic intent, but it does not invalidate the underlying privacy concerns.
The implications of this debate extend beyond Apple and Epic. It forces us to consider the ethical boundaries of technological advancement. As devices become more integrated into our lives and capable of collecting ever-increasing amounts of data, the question of who controls that data and how it is protected becomes paramount. The "Find My" network, while ostensibly a benign tool, serves as a potent example of how seemingly innocuous features can raise profound questions about privacy and surveillance in the digital age. The future of such technologies may depend on a delicate balance between innovation, user empowerment, and robust regulatory oversight. The ongoing legal and public relations battles are likely to continue to shape the narrative, forcing both consumers and policymakers to grapple with these complex issues. Whether "Find My" is ultimately viewed as a lifesaver for lost devices or a sophisticated surveillance tool will likely depend on evolving perceptions of privacy and the actions taken by both technology companies and governmental bodies. Sweeney’s outspoken criticism has undoubtedly pushed this critical conversation into the spotlight, demanding a deeper examination of the technologies that are woven into the fabric of our daily lives.