Are Password Managers Safe: A Deep Dive into Digital Security
Are password managers safe? This question has become increasingly relevant as we navigate a digital world filled with countless online accounts. Password managers, promising to streamline our logins and enhance security, have gained popularity, but are they truly trustworthy? Let’s delve into the world of password management, exploring its benefits, potential risks, and the future of this evolving technology.
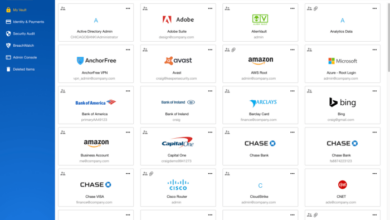
In essence, password managers act as digital vaults, securely storing your passwords and other sensitive information. They can be standalone applications, browser extensions, or mobile apps, offering a variety of features designed to make online life easier and more secure.
But with every advancement in technology, new vulnerabilities emerge, and password managers are no exception. We’ll examine the security measures implemented by reputable password managers, delve into potential risks and breaches, and compare the features and security of popular options.
The Fundamentals of Password Managers
In today’s digital world, where we interact with numerous online services, managing passwords has become a complex and daunting task. Password managers emerge as a powerful solution to streamline and secure this process. They act as a centralized vault for all your passwords, allowing you to generate, store, and access them with ease, while enhancing your online security.
Types of Password Managers
Password managers are available in various forms, catering to different user preferences and needs. They can be broadly categorized into:
- Standalone Password Managers: These are dedicated applications that run independently on your computer or mobile device. Examples include LastPass, 1Password, and Dashlane. Standalone password managers offer comprehensive features, including strong encryption, cross-platform compatibility, and advanced security measures.
- Browser Extensions: These are add-ons that integrate directly into your web browser, providing password management capabilities within your browsing environment. Popular examples include KeePassXC, Bitwarden, and Keeper. Browser extensions are generally lightweight and convenient for managing passwords within your browser.
- Mobile Apps: These are applications designed for smartphones and tablets, offering password management functionalities on the go. Many standalone password managers also provide mobile apps, enabling seamless access to your passwords across devices. Mobile apps are essential for accessing passwords when you’re away from your computer.
Benefits of Using a Password Manager
Utilizing a password manager offers a multitude of benefits, significantly enhancing your online security and convenience.
- Improved Security: Password managers employ strong encryption algorithms to safeguard your passwords, making them virtually impossible to crack without the correct master password. They also encourage the use of unique and complex passwords for each account, reducing the risk of compromised credentials.
- Convenience: Password managers eliminate the need to remember countless passwords. They automatically fill in login credentials, saving you time and effort. This is particularly beneficial when dealing with complex passwords or when accessing multiple accounts frequently.
- Efficiency: Password managers streamline the password management process, reducing the time and effort required to create, store, and access passwords. This allows you to focus on other tasks and improve your overall productivity.
Security Measures and Best Practices

Password managers are designed to enhance your online security, but their effectiveness depends on the strength of their security features and your adherence to best practices.
Encryption, Are password managers safe
Encryption is the cornerstone of password manager security. It transforms your sensitive data into an unreadable format, making it incomprehensible to unauthorized individuals. Reputable password managers use strong encryption algorithms like AES-256, which is considered virtually unbreakable.
Multi-Factor Authentication
Multi-factor authentication (MFA) adds an extra layer of security by requiring you to provide multiple forms of identification before granting access. Password managers often support MFA through methods like:
- One-time passwords (OTPs): These are temporary codes generated by an authenticator app or sent to your phone.
- Biometric authentication: This uses unique biological traits, such as fingerprint or facial recognition, for verification.
- Security keys: These are physical devices that plug into your computer or smartphone and generate a unique code for each login.
Are password managers safe? It’s a question that pops up often, and the answer, like many things in the tech world, depends on context. You’ll want to understand how they work, and that often involves getting comfortable with some basic cloud computing terms.
A great place to start is with this mini glossary of cloud computing terms that breaks down the key concepts. Once you’re familiar with the basics, you can dive deeper into how password managers leverage cloud technology to keep your passwords secure.
Secure Storage
Password managers store your credentials in a secure vault that is protected by strong encryption. This vault is typically stored on your device or in the cloud, depending on the password manager you choose. Reputable password managers use robust security measures to protect their servers and data centers from unauthorized access.
Choosing a Strong Master Password
Your master password is the key to unlocking your password vault. It is crucial to choose a strong and unique master password that is difficult to guess. A strong master password should:
- Be at least 12 characters long.
- Include a combination of uppercase and lowercase letters, numbers, and symbols.
- Avoid common words or phrases.
- Not be reused for other accounts.
We’ve all heard the question: are password managers safe? It’s a valid concern, but with the right precautions, they can be a lifesaver. And speaking of lifesavers, after two weeks with iOS 18, I’m convinced that the new auto-fill feature for password managers could be the biggest quality of life improvement in the next update, as detailed in this article after two weeks with iOS 18 this one change could be the biggest quality of life improvement of the iPhones next software update.
This new feature, combined with the security of a good password manager, makes me feel much more confident about my online security.
Storing Your Master Password Securely
Once you have chosen a strong master password, it is essential to store it securely. Avoid writing it down on paper or storing it in an easily accessible location. Instead, consider:
- Memorizing it: This is the most secure option, but it can be challenging for long and complex passwords.
- Using a password manager: If you are concerned about memorizing your master password, you can use a second password manager to store it securely.
- Using a password safe: A password safe is a physical device that stores your passwords securely, but it is less convenient than a digital solution.
Selecting a Trustworthy Password Manager
Choosing a trustworthy password manager is crucial for ensuring the security of your sensitive data. Here are some factors to consider:
- Security certifications: Look for password managers that have been audited and certified by independent security organizations, such as ISO 27001 or SOC 2.
- Independent audits: Independent audits provide assurance that a password manager’s security practices meet industry standards.
- Open-source code: Open-source password managers allow security experts to review their code for vulnerabilities, which can enhance security.
- Privacy policy: Review the password manager’s privacy policy to understand how it collects, uses, and protects your data.
- Customer support: Choose a password manager with responsive and reliable customer support in case you encounter any issues.
Potential Risks and Vulnerabilities

While password managers offer significant security advantages, they are not immune to potential risks and vulnerabilities. Understanding these risks is crucial for making informed decisions about using password managers and implementing appropriate security measures.
Data Breaches
Data breaches are a significant threat to password managers. If a password manager’s database is compromised, attackers could gain access to a vast amount of sensitive information, including usernames, passwords, and other personal data. This information could be used to access user accounts, commit identity theft, or launch further attacks.
- In 2017, the popular password manager LastPass suffered a data breach that exposed user data, including encrypted passwords. Although the breach was ultimately attributed to a third-party vulnerability, it highlighted the potential risks associated with storing sensitive information in centralized databases.
- In 2019, the password manager Keeper suffered a data breach that exposed user data, including email addresses and encrypted passwords. The breach was attributed to a vulnerability in Keeper’s web application, which allowed attackers to bypass security measures and access user data.
Malware Infections
Malware infections can pose a significant threat to password managers. Malicious software can steal user data, including passwords stored in password managers. This data can then be used to compromise user accounts, steal financial information, or launch further attacks.
You might be wondering if password managers are safe, especially with all the security breaches we hear about. It’s a valid concern, but I think it’s important to remember that even the most secure systems can be compromised. For example, Apple’s next design trick building a modern-day pyramid in Malaysia might sound futuristic, but even a structure like that could be vulnerable to attacks.
Ultimately, it’s about using a reputable password manager, enabling two-factor authentication, and being mindful of your online security practices.
- Keyloggers are a type of malware that can record every keystroke a user makes, including passwords entered into password managers. Keyloggers can be installed through malicious websites, email attachments, or compromised software.
- Trojan horses are disguised as legitimate software but contain malicious code that can steal user data, including passwords stored in password managers. Trojan horses can be spread through email attachments, malicious websites, or compromised software.
Phishing Attacks
Phishing attacks are a common way for attackers to trick users into giving up their passwords. Phishing attacks typically involve sending fake emails or messages that appear to be from legitimate organizations, such as banks or online retailers. These emails or messages often contain links to malicious websites that attempt to steal user credentials.
- Attackers can use phishing emails to trick users into entering their password manager credentials on a fake website. This can give attackers access to the user’s password vault, allowing them to steal all of their passwords.
- Attackers can use phishing emails to trick users into downloading malware that can steal user data, including passwords stored in password managers.
Weak Encryption
Password managers rely on encryption to protect user data. If a password manager uses weak encryption, attackers could potentially decrypt user data, even if the database is not compromised.
- Password managers that use outdated encryption algorithms or weak key lengths are vulnerable to attack. Attackers could potentially use brute force attacks or other techniques to decrypt user data.
- Password managers that do not use strong encryption algorithms, such as AES-256, are at a higher risk of being compromised.
Insecure Storage Practices
Password managers that use insecure storage practices, such as storing passwords in plain text, are vulnerable to attack. If a password manager’s database is compromised, attackers could gain access to user passwords in plain text.
- Password managers that store passwords in plain text are highly vulnerable to attack. Attackers could potentially gain access to the database and steal all of the passwords.
- Password managers that store passwords in a way that is easily reversible are also vulnerable. For example, password managers that use simple hashing algorithms could be compromised by attackers who can reverse the hashing process.
Comparison of Popular Password Managers
Choosing the right password manager can be overwhelming, given the numerous options available. This section delves into a comparison of popular password managers based on their features, pricing, security measures, and user experience. By understanding the strengths and weaknesses of each, you can make an informed decision that aligns with your specific needs and preferences.
Popular Password Managers Compared
This table compares popular password managers based on their features, pricing, security measures, and user experience.
| Password Manager | Features | Pricing | Security |
|---|---|---|---|
| 1Password | Strong encryption, auto-fill, password generation, secure vault, two-factor authentication, emergency access, family sharing, browser extensions, mobile apps | Free plan available, premium plans starting at $3.99/month | AES-256 encryption, zero-knowledge security, security audit, independent security reviews |
| LastPass | Password generation, auto-fill, secure vault, multi-factor authentication, emergency access, shared folders, browser extensions, mobile apps | Free plan available, premium plans starting at $3/month | AES-256 encryption, zero-knowledge security, security audit, independent security reviews |
| Dashlane | Password generation, auto-fill, secure vault, two-factor authentication, dark web monitoring, VPN, identity theft protection, browser extensions, mobile apps | Free plan available, premium plans starting at $4.99/month | AES-256 encryption, zero-knowledge security, security audit, independent security reviews |
| Bitwarden | Password generation, auto-fill, secure vault, two-factor authentication, emergency access, shared folders, browser extensions, mobile apps, open-source | Free plan available, premium plans starting at $10/year | AES-256 encryption, zero-knowledge security, security audit, independent security reviews |
| Keeper | Password generation, auto-fill, secure vault, two-factor authentication, emergency access, breach monitoring, digital vault, browser extensions, mobile apps | Free plan available, premium plans starting at $2.99/month | AES-256 encryption, zero-knowledge security, security audit, independent security reviews |
Overview of Popular Password Managers
This section provides a brief overview of each password manager, highlighting its strengths and weaknesses.
- 1Password:1Password is a popular choice known for its user-friendly interface, robust security features, and comprehensive functionality. Its strengths lie in its family sharing option, which allows multiple users to share passwords and other sensitive information securely. However, its premium plans can be relatively expensive compared to other options.
- LastPass:LastPass is another widely used password manager that offers a balance of features and affordability. It is known for its ease of use and its extensive browser extension support. However, some users have reported issues with its reliability and customer support.
- Dashlane:Dashlane distinguishes itself with its comprehensive security features, including dark web monitoring, VPN, and identity theft protection. It also boasts a user-friendly interface and a wide range of integrations. However, its premium plans can be expensive, and its security features may not be necessary for all users.
- Bitwarden:Bitwarden is an open-source password manager that prioritizes security and privacy. It offers a wide range of features at a competitive price, including a free plan with unlimited passwords. However, its user interface can be less intuitive than some other options, and its customer support is not as robust.
- Keeper:Keeper is known for its strong security features and its focus on data protection. It offers a comprehensive suite of security tools, including breach monitoring and a digital vault. However, its interface can be less user-friendly than some other options, and its premium plans can be expensive.
Alternatives to Password Managers
While password managers offer robust security and convenience, they’re not the only solution for managing your online credentials. If you’re hesitant about using a password manager or simply prefer a different approach, several alternatives exist. Let’s explore these options and their respective pros and cons.
Password Vaults
Password vaults are physical or digital storage spaces where you can securely store your passwords. They offer a basic level of security, especially when compared to simply writing passwords down on a piece of paper.
Digital Password Vaults
Digital password vaults are software applications that allow you to store your passwords in an encrypted database. Some popular options include:
- KeePass:A free, open-source password manager that runs on various platforms. It’s known for its robust security features and flexibility.
- LastPass:A cloud-based password manager that offers cross-platform compatibility and a user-friendly interface.
- Dashlane:A premium password manager that provides features like automatic form filling and password monitoring.
Physical Password Vaults
Physical password vaults are usually small, lockable containers where you can store written passwords. They are relatively inexpensive and offer a basic level of security, especially if the container is strong and the lock is robust.
Physical Notebooks
Using a physical notebook to record your passwords is a straightforward approach. While simple, it comes with inherent security risks.
Pros
- Simplicity:No software or complex setups are required.
- Accessibility:You can access your passwords anytime and anywhere.
Cons
- Security Risks:If the notebook is lost or stolen, your passwords are compromised.
- Limited Functionality:No features like password generation or automatic form filling.
- Organization Challenges:It can be difficult to manage and organize a large number of passwords.
Memory Techniques
Memory techniques, also known as mnemonics, involve using strategies to remember information, including passwords.
Pros
Cons
Scenarios Where Password Managers Might Not Be Ideal
While password managers offer numerous benefits, they might not be the best option in every situation.
Situations to Consider:
- Limited Device Access:If you frequently use devices without internet access, a password manager might not be practical.
- Privacy Concerns:Some users may be uncomfortable with the idea of a third-party service storing their passwords.
- Simple Password Needs:If you only need to manage a few passwords for low-security accounts, a password manager might be overkill.
The Future of Password Management: Are Password Managers Safe

The landscape of password management is constantly evolving, driven by technological advancements and the increasing reliance on digital services. As cyber threats become more sophisticated, the need for robust and user-friendly security solutions is paramount. This section explores emerging trends and potential advancements in password management, highlighting their impact on user security and convenience.
Biometric Authentication
Biometric authentication utilizes unique biological traits to verify user identity, offering a more secure and convenient alternative to traditional passwords. This technology leverages fingerprints, facial recognition, iris scans, and voice recognition to authenticate users, making it difficult for unauthorized individuals to gain access to accounts.
- Increased Security:Biometric authentication significantly enhances security by making it more difficult for unauthorized individuals to access accounts. Unlike passwords, which can be stolen or guessed, biometric data is unique to each individual, making it much harder to compromise.
- Enhanced Convenience:Biometric authentication eliminates the need to remember complex passwords, simplifying the login process. Users can simply use their fingerprints, faces, or voices to access their accounts, streamlining the user experience.
- Growing Adoption:Biometric authentication is rapidly gaining popularity across various platforms and devices. Smartphones, laptops, and online services are increasingly incorporating biometric authentication, making it a ubiquitous security feature.
Passwordless Login
Passwordless login eliminates the need for passwords altogether, relying on alternative authentication methods such as one-time passcodes, security keys, or biometrics. This approach aims to enhance security by removing the vulnerabilities associated with passwords, such as phishing attacks and brute-force attempts.
- Eliminating Password-Related Risks:Passwordless login mitigates the risks associated with passwords, such as forgetting passwords, password reuse, and susceptibility to phishing attacks. By removing the reliance on passwords, users are protected from these vulnerabilities.
- Simplified User Experience:Passwordless login streamlines the authentication process, eliminating the need to remember and manage complex passwords. Users can simply use a trusted device or biometric authentication to access their accounts.
- Industry-Wide Adoption:Major technology companies and industry standards organizations are actively promoting passwordless login solutions. The FIDO Alliance, for example, has developed open standards for passwordless authentication, facilitating widespread adoption.
Decentralized Storage
Decentralized storage solutions, such as blockchain technology, offer a more secure and transparent way to manage passwords. Instead of storing passwords on centralized servers, decentralized storage distributes password data across multiple nodes, making it more difficult for hackers to access.
- Enhanced Security:Decentralized storage distributes password data across multiple nodes, making it more resistant to data breaches. Even if one node is compromised, the remaining nodes will still hold the password data, ensuring its integrity.
- Increased Transparency:Decentralized storage offers increased transparency, allowing users to track and verify the access and modification of their password data. This transparency fosters trust and accountability.
- Potential for Innovation:Decentralized storage technology is still evolving, but it holds immense potential for transforming password management. Future advancements in blockchain and other decentralized technologies could lead to even more secure and user-friendly solutions.