Mobile Device Management Problems & Solutions
Mobile device management problems solutions are essential for businesses of all sizes. With the increasing use of mobile devices in the workplace, it’s more important than ever to ensure that these devices are secure and managed effectively. Imagine a world where employees can work from anywhere, access company data on their personal phones, and collaborate seamlessly with colleagues.
This is the reality of today’s mobile workforce, but it also presents unique challenges.
From securing sensitive data to managing device updates and ensuring compliance, organizations face a complex landscape of mobile device management problems. This blog post delves into the common challenges, explores effective solutions, and guides you through choosing the right mobile device management strategy for your needs.
The Growing Need for Mobile Device Management

The modern workplace is increasingly mobile, with employees relying on smartphones, tablets, and laptops to access company data and applications. This shift has created a complex landscape for IT departments, demanding new strategies to manage and secure these devices. The need for Mobile Device Management (MDM) solutions has become paramount as organizations grapple with the challenges and risks associated with unmanaged mobile devices.
The Rise of Mobile Devices in the Workplace
The increasing adoption of mobile devices in the workplace is a significant factor driving the demand for MDM solutions. Employees are demanding the flexibility to work from anywhere, anytime, using their preferred devices. Businesses are embracing this trend, recognizing the benefits of mobile technology, such as increased productivity, improved communication, and enhanced customer service.
According to a recent study by Gartner, 80% of organizations are expected to have a BYOD (Bring Your Own Device) policy in place by 2025.
The Increasing Complexity of Managing Mobile Devices
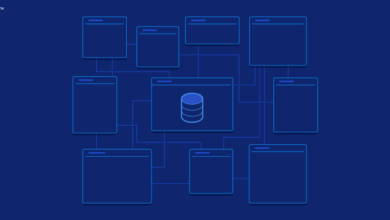
Managing mobile devices presents a unique set of challenges. The diversity of operating systems, device models, and applications requires a comprehensive and flexible MDM solution. Organizations must be able to manage device settings, enforce security policies, distribute applications, and monitor device usage across a wide range of devices.
The complexity of managing mobile devices is further amplified by the increasing number of devices being used in the workplace.
Risks Associated with Unmanaged Mobile Devices
Unmanaged mobile devices pose significant risks to organizations. These risks include:
- Data Breaches:Unsecured devices can become entry points for malicious actors, leading to data theft and breaches.
- Loss or Theft:Mobile devices are prone to loss or theft, potentially exposing sensitive company data to unauthorized access.
- Malware Infections:Unmanaged devices are vulnerable to malware infections, which can disrupt operations and compromise sensitive data.
- Compliance Violations:Organizations are often subject to industry-specific regulations that require secure data handling practices, which can be difficult to achieve without proper mobile device management.
Common Mobile Device Management Problems
Mobile device management (MDM) solutions are essential for organizations to secure and manage their mobile workforce. However, there are common challenges that can arise when implementing and using MDM solutions.
Mobile Device Security Challenges
Mobile devices are increasingly vulnerable to security threats, making it crucial to implement robust security measures. Here are some common mobile device security challenges:
- Data Breaches:Unauthorized access to sensitive data stored on mobile devices can lead to significant financial and reputational damage. Organizations must implement strong authentication measures, such as multi-factor authentication and biometrics, to prevent unauthorized access.
- Malware and Viruses:Mobile devices are susceptible to malware and viruses that can steal data, disrupt operations, or compromise the device’s security. Organizations should implement comprehensive security solutions that include anti-malware software and regular security updates.
- Lost or Stolen Devices:Losing or having a mobile device stolen can result in data breaches and unauthorized access. Organizations should implement remote wipe capabilities that allow them to erase all data from a lost or stolen device.
- Unsecured Wi-Fi Networks:Connecting to unsecured Wi-Fi networks can expose mobile devices to man-in-the-middle attacks and data theft. Organizations should educate users about the risks of using unsecured Wi-Fi networks and encourage them to use virtual private networks (VPNs) when connecting to public Wi-Fi.
- Unpatched Devices:Outdated operating systems and applications can have vulnerabilities that can be exploited by attackers. Organizations should implement a policy for timely security updates and patches to ensure that all devices are running the latest software versions.
Mobile Device Deployment and Update Complexities
Deploying and managing mobile devices can be complex, especially in large organizations with diverse device types and operating systems.
- Device Heterogeneity:Organizations often have a mix of different mobile device types, including iPhones, Android devices, and Windows phones. Managing different device types and operating systems can be challenging, as each platform has its own unique requirements and limitations.
- App Management:Managing the installation and updates of mobile applications can be complex, especially as organizations often need to deploy different apps to different user groups.
- Software Updates:Keeping mobile devices updated with the latest software versions can be a challenge, as updates can be large and time-consuming to download and install. Organizations need to ensure that all devices are running the latest software versions to protect against security vulnerabilities.
Finding the right mobile device management solution can be a real headache, especially when you’re dealing with a large and diverse workforce. But with the recent advancements in technology, like the Vision Pro’s impressive eye-tracking capabilities, we might be seeing a shift in how we interact with devices.
This impressive vision pro feature will scale back on apples future glasses like version , which could mean that future mobile device management solutions will need to adapt to these new paradigms. Ultimately, the key to effective mobile device management lies in finding the right balance between security, user experience, and technological innovation.
- User Provisioning:Provisioning new users with mobile devices and configuring them with the necessary applications and settings can be a time-consuming process. Organizations should implement streamlined user provisioning processes to ensure that new users can access the devices and applications they need quickly and efficiently.
Mobile Device Data Management Challenges
Managing data stored on mobile devices is critical to ensure data security and compliance.
- Data Security:Organizations need to ensure that sensitive data stored on mobile devices is encrypted and protected from unauthorized access.
- Data Backup and Recovery:Organizations should implement a strategy for backing up data stored on mobile devices and restoring it in case of device loss or failure.
- Data Compliance:Organizations must comply with data privacy regulations, such as the General Data Protection Regulation (GDPR), which require specific data handling practices for mobile devices.
- Data Usage Monitoring:Organizations need to monitor data usage on mobile devices to identify potential security risks or compliance violations.
Solutions for Mobile Device Management Problems
Addressing mobile device management (MDM) challenges effectively requires a proactive approach that combines strategic planning, robust security measures, and best practices for data management. By implementing a comprehensive MDM strategy, organizations can mitigate risks, enhance productivity, and ensure the secure use of mobile devices.
Designing a Comprehensive Mobile Device Management Strategy
A well-designed MDM strategy serves as the foundation for managing mobile devices effectively. This strategy should encompass various aspects, including device enrollment, security policies, application management, data protection, and user access control.
- Device Enrollment: Implementing a streamlined device enrollment process is crucial for managing mobile devices effectively. This process should be user-friendly and allow for easy integration of new devices into the MDM system.
- Security Policies: Implementing robust security policies is essential for protecting sensitive data and preventing unauthorized access to mobile devices. These policies should address various aspects, including password complexity, screen lock timeout, data encryption, and remote wipe capabilities.
- Application Management: Managing applications on mobile devices is vital for ensuring that only authorized apps are installed and used. This includes controlling app access, restricting app downloads, and managing app updates.
- Data Protection: Protecting sensitive data on mobile devices is paramount. This involves implementing data encryption, enforcing data loss prevention (DLP) policies, and ensuring secure data storage and transmission.
- User Access Control: Implementing user access control mechanisms is crucial for limiting user privileges and preventing unauthorized access to sensitive information. This includes restricting user access to specific apps, data, and functionalities.
Effective Mobile Device Security Solutions
There are several effective mobile device security solutions available in the market, each with its own set of features and capabilities.
- Mobile Device Management (MDM) Solutions: MDM solutions provide comprehensive control over mobile devices, enabling organizations to manage device configurations, enforce security policies, and monitor device usage. Popular MDM solutions include Microsoft Intune, VMware Workspace ONE, and Citrix Endpoint Management.
- Endpoint Detection and Response (EDR) Solutions: EDR solutions offer advanced threat detection and response capabilities for mobile devices. They monitor device activity, identify suspicious behavior, and provide real-time threat alerts and remediation options.
- Mobile Threat Defense (MTD) Solutions: MTD solutions specialize in detecting and mitigating mobile threats, including malware, phishing attacks, and data breaches. These solutions use machine learning and artificial intelligence to identify and neutralize potential threats.
- Multi-Factor Authentication (MFA): Implementing MFA adds an extra layer of security to mobile device access. MFA requires users to provide multiple forms of authentication, such as a password and a one-time code, to gain access to sensitive data.
Best Practices for Managing Mobile Device Data
Effective data management practices are essential for protecting sensitive information on mobile devices.
- Data Encryption: Encrypting data on mobile devices is crucial for preventing unauthorized access. This involves using strong encryption algorithms to scramble data, making it unreadable without the proper decryption key.
- Data Loss Prevention (DLP) Policies: Implementing DLP policies helps prevent the unauthorized transfer of sensitive data outside the organization. These policies can monitor data movement, identify sensitive information, and block unauthorized data transfers.
- Secure Data Storage: Ensuring secure data storage on mobile devices is essential. This includes using encrypted storage solutions, backing up data regularly, and implementing access controls to restrict data access.
- Regular Data Backup: Regularly backing up data on mobile devices is essential for data recovery in case of device loss or damage. This involves creating backups of critical data, such as contacts, messages, photos, and documents, to a secure location.
Choosing the Right Mobile Device Management Solution
With so many mobile device management (MDM) solutions available, choosing the right one for your organization can be a daunting task. The best solution for you will depend on your specific needs, budget, and the size and complexity of your mobile device fleet.
Factors to Consider When Selecting a Mobile Device Management Solution
When selecting an MDM solution, it’s crucial to consider several key factors to ensure the chosen solution aligns with your organizational requirements.
Keeping your mobile devices secure is crucial, especially with the ever-evolving threat landscape. While we’re focusing on mobile device management problems, it’s important to be aware of broader cybersecurity threats like those posed by generative AI, which can be used to create highly sophisticated ransomware.
For example, a recent article on generative AI ransomware threats in the UK highlights the growing risk. Returning to mobile device management, implementing robust security measures like strong passwords, multi-factor authentication, and regular software updates is essential to mitigate these risks and protect your data.
- Device Support:Ensure the solution supports the types of devices used in your organization, including smartphones, tablets, laptops, and wearables. Different MDM solutions may have varying levels of support for different operating systems, such as iOS, Android, Windows, and macOS.
- Features and Functionality:Evaluate the features offered by the MDM solution and ensure they meet your needs. Some essential features include device enrollment, remote wipe, app management, security policies, data encryption, and compliance reporting.
- Ease of Use and Administration:The MDM solution should be easy to use and manage, both for IT administrators and end users. Consider the complexity of the user interface, the availability of comprehensive documentation, and the level of technical support provided.
- Scalability:Select a solution that can scale to accommodate your future growth. Consider the number of devices you expect to manage and the potential for expansion.
- Integration:Ensure the MDM solution integrates seamlessly with your existing IT infrastructure, such as Active Directory, your email server, and other enterprise applications.
- Security and Compliance:Security and compliance are critical considerations. The MDM solution should offer robust security features, such as data encryption, access control, and compliance reporting. Choose a solution that meets the relevant industry standards and regulations.
- Cost:Evaluate the cost of the MDM solution, including licensing fees, support costs, and any additional expenses. Consider the long-term cost of ownership and the value the solution provides.
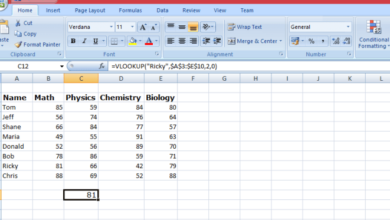
Evaluating Mobile Device Management Software
To aid in the selection process, consider using a checklist to evaluate different MDM solutions based on your requirements.
- Device Support:What types of devices and operating systems are supported by the solution?
- Features:What key features are offered, including device enrollment, remote wipe, app management, security policies, data encryption, and compliance reporting?
- Ease of Use:How user-friendly is the solution for administrators and end users?
- Scalability:Can the solution accommodate future growth in the number of devices?
- Integration:Does the solution integrate with your existing IT infrastructure?
- Security and Compliance:What security features and compliance certifications does the solution offer?
- Cost:What are the licensing fees, support costs, and other associated expenses?
- Vendor Reputation:Research the vendor’s reputation, track record, and customer support.
- Trial Period:Request a trial period to evaluate the solution in your environment.
Implementing Mobile Device Management Solutions: Mobile Device Management Problems Solutions
Implementing a mobile device management (MDM) solution requires a well-defined plan and a systematic approach to ensure a successful transition and optimal utilization of the solution. This section will delve into the key steps involved in implementing an MDM solution, providing a comprehensive guide for configuring and deploying the solution effectively.
Choosing the Right MDM Solution
Selecting the right MDM solution is a crucial first step. This involves evaluating various factors such as the size and complexity of your organization, the types of mobile devices used, and the specific security and management features required. Once you’ve chosen an MDM solution, you need to acquire the necessary licenses and ensure that the solution is compatible with your existing infrastructure and security policies.
Planning for Implementation
Planning is essential for a smooth and successful MDM implementation. This involves identifying the scope of the implementation, defining clear objectives, and establishing a timeline for the project. You should also consider the impact of the MDM solution on your existing IT infrastructure, including any potential changes to network configurations or user access policies.
Configuring the MDM Solution
After choosing and acquiring the MDM solution, you need to configure it to meet your specific requirements. This involves setting up user accounts, defining device policies, and configuring security settings. The configuration process should be tailored to your organization’s unique needs and security protocols.
Deploying the MDM Solution
Deployment of the MDM solution involves installing the necessary software on both the mobile devices and the management server. This process can be done manually or automated using tools provided by the MDM vendor. It’s crucial to ensure that the deployment process is smooth and efficient, minimizing any disruption to users.
User Training and Support
Providing adequate user training and support is essential for successful MDM adoption. Users should be trained on how to use the MDM solution, understand the policies enforced, and access support resources. This can be done through online documentation, interactive tutorials, or in-person training sessions.
Managing mobile devices can be a headache, especially when you’re dealing with a diverse range of operating systems and applications. One recent example of this challenge is Valve’s decision to drop Mac support for its biggest titles , leaving many users scrambling for alternative solutions.
Fortunately, robust mobile device management solutions can help you stay ahead of the curve, ensuring compatibility and security across your entire fleet of devices.
Monitoring and Optimization
After deploying the MDM solution, it’s crucial to monitor its performance and optimize it for efficiency. This involves tracking device usage, analyzing security events, and making adjustments to policies and configurations as needed. Regular monitoring helps identify potential issues and ensures the MDM solution remains effective in meeting your security and management objectives.
Managing Mobile Device Data
Mobile device data management is crucial for organizations of all sizes. It encompasses a comprehensive approach to protecting, securing, and managing data stored on employee-owned or company-issued mobile devices. Effective data management ensures business continuity, protects sensitive information, and complies with data privacy regulations.
Creating a Comprehensive Mobile Device Data Management Plan
A well-defined mobile device data management plan Artikels policies, procedures, and strategies for handling data on mobile devices. This plan should be tailored to the specific needs and risks of the organization.
- Data Inventory and Classification:The plan should identify all types of data stored on mobile devices, classify them based on sensitivity, and define appropriate access controls.
- Data Security Policies:Clearly defined policies should Artikel acceptable use of mobile devices, data sharing practices, and password requirements.
- Data Encryption:The plan should mandate encryption for all sensitive data stored on mobile devices, ensuring data confidentiality even if devices are lost or stolen.
- Data Backup and Recovery:Regular backups of mobile device data should be implemented to ensure data can be restored in case of device failure or data loss.
- Data Deletion and Retention Policies:Policies should Artikel procedures for securely deleting data from mobile devices when they are no longer in use or when employees leave the organization.
Methods for Encrypting and Securing Mobile Device Data
Data encryption is a fundamental aspect of mobile device data management. It involves converting data into an unreadable format, making it inaccessible to unauthorized individuals.
- Device-Level Encryption:Operating systems like iOS and Android offer built-in encryption capabilities that encrypt the entire device storage, protecting all data on the device.
- App-Level Encryption:Some applications provide their own encryption mechanisms, protecting specific data within the app. This is particularly important for apps handling sensitive information like financial data or personal health records.
- File-Level Encryption:This approach encrypts individual files, allowing users to selectively protect sensitive documents. Several third-party encryption tools are available for this purpose.
Strategies for Backing Up and Restoring Mobile Device Data
Regular data backups are essential to mitigate data loss risks. They provide a copy of data that can be used to restore devices or recover lost data.
- Cloud-Based Backups:Services like iCloud, Google Drive, and Dropbox offer convenient cloud storage solutions for backing up mobile device data. These services automatically sync data across multiple devices, ensuring data availability.
- Local Backups:Users can manually back up data to external storage devices like USB drives or SD cards. This method provides a physical copy of data, which can be useful in situations where cloud access is limited.
- Mobile Device Management (MDM) Solutions:Some MDM solutions include features for backing up and restoring mobile device data. These solutions can automate the backup process and provide centralized control over data recovery.
Mobile Device Security Best Practices
Mobile device security is crucial in today’s interconnected world, where sensitive data is constantly at risk. Organizations and individuals alike must implement robust security measures to protect their devices and the information they hold. This involves adopting a comprehensive approach that encompasses various security best practices.
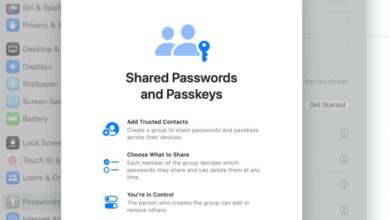
Strong Passwords and Multi-Factor Authentication
Strong passwords and multi-factor authentication are essential for safeguarding access to mobile devices and the data they contain. A strong password should be at least 12 characters long, combining uppercase and lowercase letters, numbers, and symbols.
- It is advisable to avoid using personal information such as birthdays or names in passwords.
- Using a password manager can help you generate and store strong, unique passwords for different accounts.
Multi-factor authentication adds an extra layer of security by requiring users to provide more than one form of identification before granting access.
- This can involve a combination of something you know, such as a password, and something you have, such as a physical token or a smartphone.
- Multi-factor authentication significantly reduces the risk of unauthorized access, even if one authentication factor is compromised.
“Multi-factor authentication should be enabled for all sensitive accounts, including email, banking, and social media.”
Mobile Device Security Software, Mobile device management problems solutions
Mobile device security software plays a vital role in protecting devices from malware, data breaches, and other threats. These applications can provide features such as:
- Antivirus and anti-malware protection: Detecting and removing malicious software that can steal data, compromise device performance, or allow unauthorized access.
- Data encryption: Encrypting sensitive data stored on the device, making it unreadable to unauthorized individuals.
- App permissions management: Controlling which apps have access to specific device features and data, such as contacts, location, and camera.
- Remote device management: Enabling administrators to remotely wipe data, lock devices, or track their location in case of loss or theft.
The Future of Mobile Device Management
The landscape of mobile device management (MDM) is constantly evolving, driven by technological advancements and the increasing reliance on mobile devices in both personal and professional settings. As we move forward, MDM solutions will need to adapt to meet new challenges and opportunities.
Emerging Trends in Mobile Device Management
Several key trends are shaping the future of MDM:
- Artificial Intelligence (AI) and Machine Learning (ML):AI and ML will play an increasingly important role in MDM. These technologies can be used to automate tasks, detect and respond to security threats, and optimize device performance. For example, AI-powered MDM solutions can analyze device usage patterns to identify potential security risks or recommend configuration changes to improve battery life.
- Zero Trust Security:Zero trust security models assume that no user or device can be trusted by default. MDM solutions will need to incorporate zero trust principles to ensure that only authorized users and devices have access to sensitive data.
- The Rise of the Internet of Things (IoT):The proliferation of IoT devices is creating new challenges for MDM. MDM solutions will need to be able to manage a wider range of devices, including wearables, smart home devices, and industrial equipment.
- Cloud-Based MDM:Cloud-based MDM solutions are becoming increasingly popular due to their scalability, flexibility, and cost-effectiveness. These solutions allow organizations to manage devices from anywhere in the world, and they can be easily scaled to meet the needs of growing businesses.
Impact of New Technologies on Mobile Device Management
Emerging technologies are transforming the way we manage mobile devices:
- 5G:The rollout of 5G networks will enable faster data speeds and lower latency, which will have a significant impact on mobile device management. 5G will enable new MDM features, such as real-time device monitoring and remote device control.
- Blockchain:Blockchain technology can be used to improve the security of MDM solutions. Blockchain can be used to create an immutable record of device data, making it more difficult for hackers to tamper with or steal information.
- Edge Computing:Edge computing is a distributed computing paradigm that brings computation and data storage closer to the source of the data. This will enable MDM solutions to manage devices more efficiently, even in remote locations with limited connectivity.
Predictions for the Future of Mobile Device Management
Here are some predictions for the future of MDM:
- Increased Automation:MDM solutions will become increasingly automated, with AI and ML playing a key role in tasks such as device provisioning, security updates, and troubleshooting.
- Enhanced Security:MDM solutions will continue to evolve to address emerging security threats. This will include the adoption of zero trust security models, advanced threat detection and response capabilities, and increased use of biometrics and multi-factor authentication.
- Personalized Device Management:MDM solutions will become more personalized, allowing organizations to tailor their management policies to the specific needs of different users and devices.
- Greater Focus on User Experience:MDM solutions will need to provide a more user-friendly experience for both administrators and end users. This will include simplifying device management tasks and providing more intuitive user interfaces.