Cybersecurity
-

Contis Fragmentation: More Dangerous Than Ever?
Conti reforms into several smaller groups are they now more dangerous than ever – Conti’s reforms into several smaller groups…
Read More » -

Microsoft Octo Tempest Threat Actor: A Cybersecurity Threat
Microsoft Octo Tempest threat actor is a sophisticated and persistent cyber threat group known for its targeted attacks against various…
Read More » -

Cyber Security Trends UK: Navigating the Evolving Threat Landscape
Cyber Security Trends UK takes center stage as the digital world evolves, presenting a landscape of constant change. From the…
Read More » -

Cisco Talos Uncovers New Malware from Lazarus Group
Cisco talos lazarus group new malware – Cisco Talos, the threat intelligence arm of Cisco, has uncovered a new malware…
Read More » -

Cybersecurity: FBI & Homeland Security United
Cybersecurity fbi homeland security – Cybersecurity: FBI & Homeland Security United – these three entities are intertwined in a complex…
Read More » -

Zero Trust Security Tips: Protecting Your Digital Assets
Zero Trust security tips are essential in today’s digital landscape, where threats are constantly evolving. The traditional perimeter-based security model…
Read More » -

Def Con Hackers Embrace Generative AI
Def Con hackers generative AI sets the stage for this enthralling narrative, offering readers a glimpse into a story that…
Read More » -
Israel Threat Actors Target Organizations with Email Attacks
Israel threat actors email attacks are a growing concern for organizations in the region. These attacks often leverage sophisticated phishing…
Read More » -

CBA AI Cybersecurity: An Interview with Andrew Pade
Cba ai cybersecurity andrew pade interview – CBA AI Cybersecurity: An Interview with Andrew Pade delves into the crucial role…
Read More » -
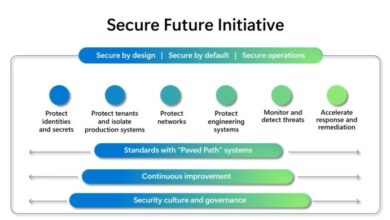
Microsoft Secure Future Initiative Report: Shaping a Safer Digital World
The Microsoft Secure Future Initiative Report delves into the ever-evolving landscape of cybersecurity, highlighting the crucial role technology plays in…
Read More »


