One Overlooked Element Of Executive Safety Data Privacy
The Unseen Perimeter: Executive Data Privacy as a Strategic Imperative
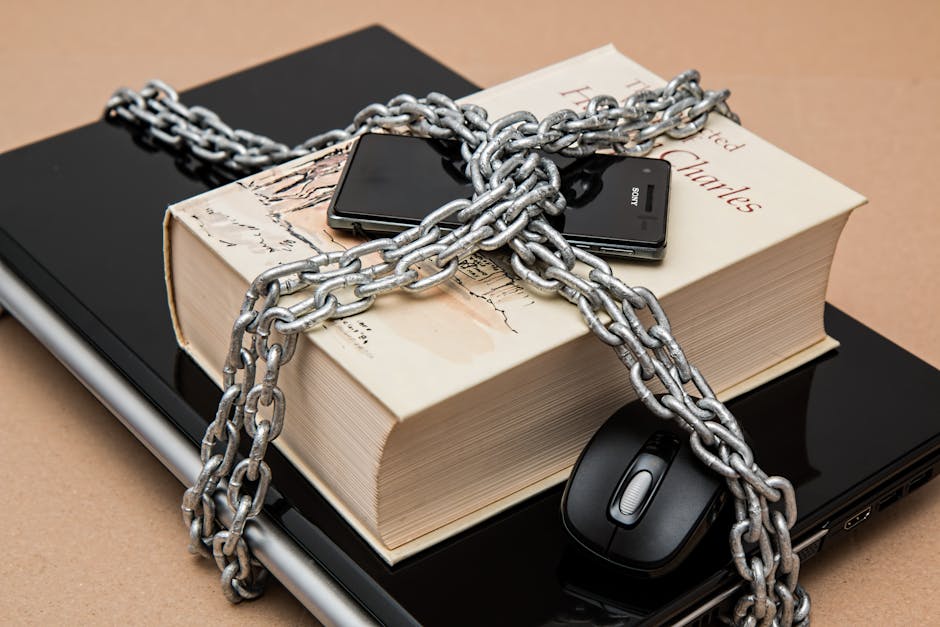
In the relentless pursuit of organizational security, the focus often gravitates towards the robust firewalls, advanced intrusion detection systems, and comprehensive employee cybersecurity training. While these are undeniably critical pillars, a significant and often overlooked element of executive safety, and by extension, organizational privacy, lies within the domain of executive data privacy. This encompasses the meticulous safeguarding of personal and professional information that, when exposed, can create vulnerabilities not just for the individual leader, but for the entire enterprise. The digital footprint of an executive is a rich tapestry of sensitive data, from their professional affiliations and travel itineraries to their financial holdings and personal communication channels. The compromise of this information is not merely a personal inconvenience; it can be a sophisticated vector for targeted attacks, reputational damage, and even corporate espionage, impacting stock prices, intellectual property, and strategic decision-making.
The insidious nature of executive data privacy breaches stems from the unique position executives occupy within an organization. They are often the repositories of highly confidential information, privy to merger and acquisition discussions, R&D secrets, and sensitive personnel matters. Furthermore, their public profiles, while necessary for leadership and brand representation, also present a larger attack surface. The very attributes that make them visible and influential – their network of contacts, their speaking engagements, their media appearances – become potential points of exploitation. Threat actors understand that compromising an executive’s data can provide a gilded key to unlock a wealth of organizational secrets. This isn’t just about phishing emails; it’s about sophisticated social engineering, deepfake impersonations, and targeted data exfiltration campaigns that leverage publicly available or illicitly obtained personal information. The consequences extend beyond financial loss, reaching into the realm of regulatory non-compliance and the erosion of trust, both internally and externally.
One of the most prevalent and underestimated threats to executive data privacy is the proliferation of personally identifiable information (PII) across public and semi-public digital landscapes. Executives, in their professional lives, often engage with a multitude of platforms and services. This can include professional networking sites like LinkedIn, which, while invaluable for career advancement, can also reveal extensive professional histories, current roles, and valuable connections. Beyond professional realms, personal online accounts, often less stringently secured, can house a treasure trove of data. Social media platforms, online shopping accounts, and even loyalty program registrations can inadvertently expose details such as home addresses, birthdates, family members’ names, and vacation plans. This information, seemingly innocuous in isolation, can be aggregated by malicious actors to construct detailed profiles, enabling highly targeted attacks. For instance, knowing an executive’s travel dates can facilitate a sophisticated "vishing" (voice phishing) attack, where a scammer, posing as a travel agent or hotel representative, attempts to elicit further sensitive information by referencing their upcoming trip. The lack of proactive data minimization and robust privacy controls around these seemingly benign digital interactions creates an unaddressed vulnerability.
Furthermore, the interconnectedness of digital identities exacerbates this risk. Many executives, for convenience, reuse passwords across multiple platforms. A single data breach on a less secure platform can compromise the credentials for more critical corporate accounts. This password fatigue is a universal human trait, but for executives, the stakes are exponentially higher. The ability to gain access to an executive’s email, cloud storage, or internal communication tools can grant attackers a direct pathway to sensitive corporate data, strategic plans, and confidential communications. The ease with which credentials can be brute-forced or acquired through credential stuffing attacks, fueled by data dumps from previous breaches, makes this a persistent and potent threat. The onus is not just on the executive to maintain strong, unique passwords, but on the organization to implement robust identity and access management (IAM) policies, including multi-factor authentication (MFA) as a non-negotiable standard for all executive-level access.
The concept of "digital housekeeping" for executives is often neglected. This involves a conscious and ongoing effort to audit, prune, and secure their online presence. Many executives are unaware of the extent of their personal information available through data brokers and people search engines. These services aggregate data from public records, social media, and other sources, creating detailed dossiers on individuals. A simple online search can reveal an executive’s past addresses, phone numbers, and even family connections, all readily accessible to anyone willing to pay a small fee. Organizations have a responsibility to educate their executives about these risks and to provide resources for managing their digital footprint. This could include services that help identify and remove PII from data broker websites, or guidance on configuring privacy settings across all online accounts. The proactive removal of extraneous personal data from the public domain significantly reduces the attack surface available to malicious actors, making it harder for them to build comprehensive profiles for exploitation.
Social engineering, a cornerstone of many cyberattacks, thrives on the exploitation of human psychology and readily available information. For executives, this often manifests in highly personalized attacks. Threat actors may leverage information gleaned from their digital footprint – a recent conference attendance, a shared interest in a particular hobby, or a known personal acquaintance – to craft convincing phishing emails or impersonation attempts. For example, an attacker might send an email seemingly from a trusted colleague, referencing a recent meeting or project, and request an urgent action that involves divulging sensitive information or transferring funds. The sophistication of these attacks is escalating with the use of AI-powered tools, capable of generating highly realistic text and even voice impersonations. The lack of awareness regarding the depth and breadth of their publicly accessible data makes executives particularly susceptible to these tailored social engineering schemes.
The perimeter of executive safety is not solely defined by technological defenses; it is increasingly characterized by the security of their personal digital lives. The lines between personal and professional have blurred, and with it, the vulnerability has expanded. Consider the increasing use of personal devices for work purposes, often without adequate security controls. While convenient, this practice can expose corporate data to risks associated with personal account compromises or malware infections on the personal device. Furthermore, the personal communications of executives, whether through encrypted messaging apps or less secure email platforms, can be a target. A compromise here could reveal sensitive strategic discussions, internal disagreements, or personal vulnerabilities that could be leveraged for blackmail or reputational damage. The organization must extend its security consciousness to encompass the personal digital habits of its leaders, providing clear guidelines and support for secure personal device usage and communication practices.
Data privacy laws and regulations, while primarily focused on customer and employee data, also have implications for executive privacy. Breaches of executive data can lead to regulatory scrutiny and potential penalties, especially if the compromised information pertains to company-sensitive matters that fall under data protection regulations. For instance, if an executive’s personal data is leaked and it contains information related to protected health information (PHI) or financial data, the organization could face significant compliance issues. Proactive executive data privacy measures are not just about mitigating direct threats; they are also about ensuring broader organizational compliance and reducing the risk of indirect regulatory repercussions.
The concept of "digital guardianship" for executives is emerging as a critical component of executive safety. This involves dedicated support and resources to actively manage and protect their digital identities. This could be integrated into executive protection programs, encompassing physical security as well as digital. Services might include proactive threat intelligence monitoring for executive-related information, secure communication platforms, and expert guidance on digital hygiene. The organization’s commitment to executive data privacy signals a sophisticated understanding of modern security threats and a dedication to safeguarding its most valuable assets – its leadership.
The financial implications of compromised executive data are substantial. Beyond the direct costs of remediation and incident response, there are indirect costs associated with reputational damage, loss of investor confidence, and potential stock price depreciation. A high-profile data breach involving an executive can trigger widespread public distrust, making it difficult for the company to attract talent, secure partnerships, and maintain customer loyalty. The long-term erosion of brand value can be far more damaging than the immediate financial losses. Therefore, investing in robust executive data privacy is not an expense, but a strategic investment in the stability and continued success of the organization.
In conclusion, executive data privacy is a critical, yet frequently overlooked, element of modern organizational security. It extends beyond traditional cybersecurity measures to encompass the meticulous safeguarding of personal and professional digital footprints. The interconnectedness of digital lives, the prevalence of PII, and the sophistication of social engineering tactics necessitate a proactive and comprehensive approach. Organizations must move beyond basic security protocols and embrace strategies that include digital housekeeping, robust IAM policies, and the concept of digital guardianship. By recognizing and actively addressing the unseen perimeter of executive data privacy, organizations can significantly mitigate risks, protect their leadership, and preserve their most valuable assets.
