Why Antivirus Programs Have Become The Problem Not The Solution
The Antivirus Paradox: From Protector to Peril
For decades, antivirus software has been positioned as the ironclad guardian of our digital lives, the essential bulwark against a ceaseless onslaught of malware. Yet, a disquieting reality has emerged: in many critical aspects, antivirus programs have transitioned from being the solution to becoming a significant part of the problem. This evolution is not a sudden betrayal but a gradual consequence of the ever-changing threat landscape, the inherent limitations of signature-based detection, the pervasive issues of false positives and performance degradation, and the unsettling rise of antivirus software itself as a lucrative target and vector for attack. Understanding this paradox is crucial for navigating the modern cybersecurity ecosystem effectively, as a misplaced reliance on traditional antivirus can foster a false sense of security, leaving users vulnerable to sophisticated threats that bypass its antiquated defenses.
The fundamental flaw in the traditional antivirus model lies in its reactive nature. For the vast majority of its existence, antivirus has operated on a signature-based detection system. This method requires the antivirus software to maintain a massive database of known malware signatures – unique digital fingerprints of malicious code. When a file is scanned, its signature is compared against this database. If a match is found, the file is flagged as malicious and quarantined or deleted. The problem is that this approach is inherently reactive. It can only detect threats that have already been identified, analyzed, and cataloged. Cybercriminals, constantly innovating and evolving their attack vectors, can easily generate new malware variants, polymorphic viruses that change their code with each infection, and zero-day exploits that are entirely unknown to security vendors. By the time a signature is created for a new threat, countless systems may have already been compromised. This "race to catch up" means that signature-based antivirus is perpetually a step behind the most advanced and prevalent threats, rendering it a highly ineffective defense against contemporary malware.
Beyond the signature limitation, the sheer volume and velocity of new malware appearing daily overwhelm signature-based systems. Security researchers and automated systems work tirelessly to identify and analyze new threats, but the output of malicious code far outstrips the ability to create and distribute updated signature databases to every endpoint. This constant influx of new threats means that even with regular updates, there’s a significant window of vulnerability between a new malware variant’s emergence and its inclusion in an antivirus definition file. Furthermore, many modern malware strains employ sophisticated evasion techniques, such as fileless malware that operates purely in memory, or deliberately delaying their execution to avoid detection during scans. These methods are specifically designed to circumvent the static analysis employed by signature-based antivirus, rendering it blind to their presence.
The performance impact of traditional antivirus software is another significant drawback, often leading users to disable or neglect its protective features, thereby increasing their vulnerability. Antivirus programs, by their very nature, are resource-intensive. They constantly run in the background, monitoring system processes, scanning files on access and execution, and performing periodic deep scans. This continuous activity can consume substantial CPU and RAM resources, leading to noticeable slowdowns in system performance, increased application loading times, and a generally sluggish user experience. For users with older or less powerful hardware, this performance degradation can be particularly pronounced, making their computers frustrating to use. In an effort to regain performance, many users opt to disable real-time protection, reduce scan frequencies, or even uninstall the antivirus software altogether, inadvertently leaving themselves exposed to the very threats the software is intended to protect against. This creates a perverse incentive where the "solution" actively encourages its own deactivation.
False positives, where legitimate software or files are mistakenly identified as malicious, further erode user trust and contribute to the antivirus problem. These errors can cause significant disruption, preventing users from accessing essential applications, deleting critical system files, or even causing system instability. The process of rectifying a false positive can be time-consuming and complex, often requiring manual intervention, submission of samples to the antivirus vendor, and waiting for a fix. Repeated false positives can lead to user frustration and a diminished willingness to heed the antivirus’s warnings, potentially causing them to ignore genuine threats when they do arise. This desensitization to security alerts, bred by a history of inaccurate flagging, is a dangerous consequence of poorly tuned antivirus engines.
The rise of sophisticated, fileless, and memory-resident malware has rendered traditional signature-based detection largely obsolete. These advanced threats operate without writing traditional files to disk, making them invisible to scanners that primarily focus on file analysis. Instead, they execute directly in system memory, often leveraging legitimate system tools and processes to achieve their malicious objectives. Examples include PowerShell-based attacks, macro-enabled documents that download and execute payloads in memory, and exploits that inject malicious code into running processes. Antivirus solutions that rely solely on signature databases are ill-equipped to detect such threats, as there are no discrete files to scan for matching signatures. This leaves users protected against yesterday’s threats but vulnerable to today’s most prevalent attack vectors.
Furthermore, the very nature of antivirus software, being a highly privileged program with deep access to the operating system, makes it an attractive target for attackers. If an attacker can compromise the antivirus software itself, they gain a powerful foothold within the system, allowing them to disable security measures, exfiltrate data, or deploy further malware undetected. Historically, numerous vulnerabilities have been discovered in popular antivirus products, allowing attackers to exploit these weaknesses to gain elevated privileges or execute arbitrary code. The proprietary nature of much antivirus code makes independent auditing difficult, and the constant pursuit of new detection methods can sometimes introduce unintended security flaws. This means that the very tool designed to protect the system can, in fact, become its weakest link.
The widespread deployment of antivirus software also contributes to a centralized attack surface for malicious actors. Instead of targeting individual user machines randomly, attackers can focus their efforts on finding vulnerabilities in popular antivirus platforms. A successful exploit against a widely used antivirus product could potentially compromise millions of machines simultaneously, offering a highly efficient and impactful attack vector. This has led to a scenario where antivirus vendors are not just facing individual malware threats but are also engaged in a constant battle against sophisticated adversaries seeking to subvert their own security products.
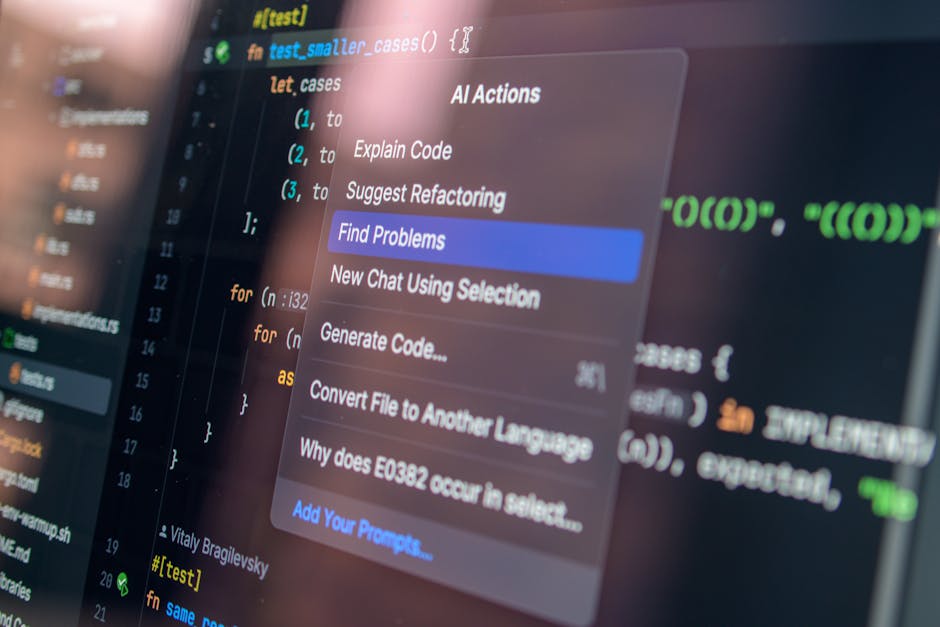
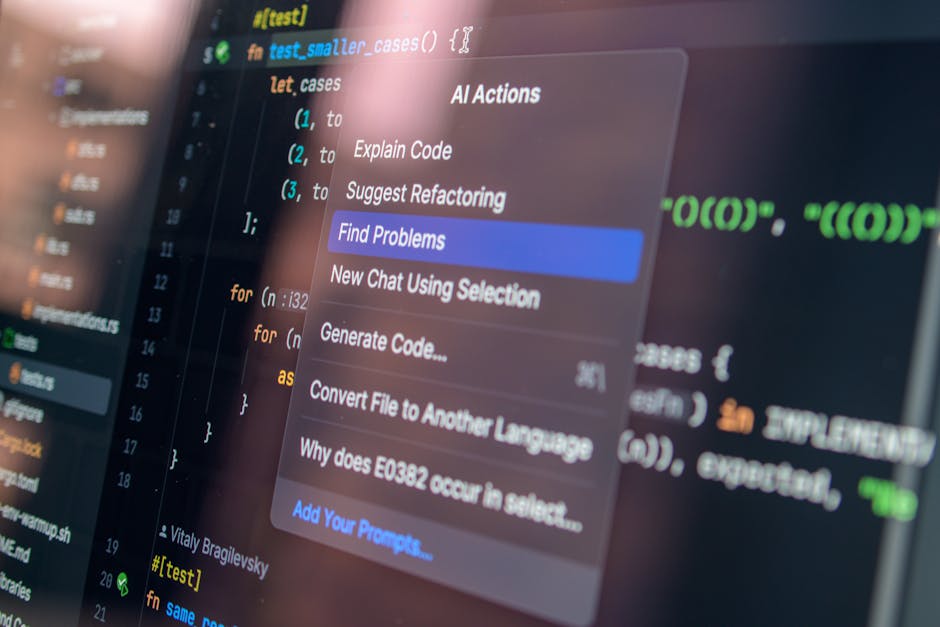
The dominance of traditional antivirus has also stifled innovation in alternative and more effective cybersecurity solutions. The market has been so saturated with signature-based products that other promising technologies, such as behavioral analysis, machine learning-based anomaly detection, sandboxing, and endpoint detection and response (EDR) solutions, have struggled to gain widespread adoption or have been relegated to niche markets. These newer approaches are designed to detect threats based on their behavior and characteristics rather than relying on pre-existing signatures, making them far more adept at identifying unknown and evolving malware. However, the inertia of the existing antivirus market and the established customer base for traditional products have created a significant barrier to entry for these more advanced solutions.
The "security suite" model, where antivirus is bundled with firewalls, parental controls, and other utilities, further exacerbates the problem by creating complex and often poorly integrated software packages. These suites can introduce additional performance overhead and potential conflicts with other software installed on the system. The marketing of these comprehensive suites often implies a holistic security solution, leading users to believe they are fully protected when, in reality, the core antivirus component may be failing to address modern threats. The perceived value of these bundled solutions can mask the underlying deficiencies of the primary protection mechanism.
Moreover, the business model of many antivirus companies, which often relies on recurring subscription fees for updates and support, creates a vested interest in the continued existence of threats that can be "detected" by their software. While no reputable company intentionally creates malware, the pressure to demonstrate ongoing value and justify subscription renewals can inadvertently create an environment where the focus remains on identifying and "quarantining" threats rather than fundamentally preventing them or fostering a more inherently secure computing environment. The economic incentive is often tied to the continued existence of the problem rather than its eradication.
The widespread use of antivirus software has also led to a dangerous over-reliance on its capabilities, fostering a false sense of security among users. Many individuals and organizations believe that simply having an antivirus program installed is sufficient to protect them from all cyber threats. This mindset can lead to complacency, making users less diligent about practicing good cybersecurity hygiene, such as keeping software updated, using strong and unique passwords, being cautious about email attachments and links, and implementing robust backup strategies. When the antivirus fails to detect a sophisticated threat, the user is left exposed and often unaware of the compromise until significant damage has occurred. This reliance on a single, often inadequate, layer of defense is a critical cybersecurity failing.
The solution is not to abandon all security measures but to evolve our approach. Modern cybersecurity requires a layered defense strategy that moves beyond traditional signature-based antivirus. This includes adopting endpoint detection and response (EDR) solutions that employ advanced behavioral analysis and machine learning to identify anomalous activity. Network security measures like next-generation firewalls, intrusion detection and prevention systems, and web application firewalls are crucial. User education remains paramount, fostering a culture of cybersecurity awareness and promoting safe online practices. Furthermore, embracing principles of secure development and regular vulnerability patching across all software is essential to reduce the attack surface in the first place. The future of cybersecurity lies in proactive, intelligence-driven, and behavior-aware solutions, not in the increasingly obsolete signature-based guardians of the past.



