Volt Typhoon Exploits Versa Director: A Cybersecurity Threat
Volt Typhoon Exploits Versa Director, setting the stage for a captivating narrative that delves into the world of sophisticated cyberattacks and the critical role of cybersecurity in protecting critical infrastructure. This story unveils the intricate workings of a threat actor, their motivations, and the vulnerabilities they exploit to infiltrate and disrupt essential systems.
Volt Typhoon, a state-sponsored hacking group, has been targeting critical infrastructure in the United States, utilizing sophisticated techniques to gain access to sensitive data. The group’s operations have raised concerns about the potential for widespread disruption and data breaches, highlighting the need for robust cybersecurity measures to safeguard vital networks.
Volt Typhoon

Volt Typhoon is a sophisticated cyberespionage group that has been active since at least 2019, targeting critical infrastructure in the Asia-Pacific region. The group, believed to be of Chinese origin, has demonstrated a significant level of technical expertise and strategic planning in its operations.
The Threat
Volt Typhoon’s primary objective is to gather intelligence on critical infrastructure, potentially for strategic or economic advantage. The group’s activities have raised concerns about the vulnerability of essential services to cyberattacks, potentially impacting national security and economic stability.
The Volt Typhoon exploits targeting Versa Director are a stark reminder of the evolving cyber threat landscape. While we grapple with these sophisticated attacks, it’s fascinating to see how Apple’s Vision Pro, with its impressive eye-tracking capabilities, could potentially scale back on the need for future glasses-like versions , which could inadvertently impact the evolution of these types of attacks.
The future of cybersecurity is inextricably linked to the development of new technologies, and it’s crucial to anticipate how these innovations will shape the threats we face.
Potential Impact on Critical Infrastructure
Volt Typhoon’s targeting of critical infrastructure presents a serious threat, as it could disrupt essential services like power grids, telecommunications, and transportation networks. Successful attacks could lead to widespread power outages, communication disruptions, and economic losses. For example, in 2015, the Ukrainian power grid was disrupted by a cyberattack, leaving hundreds of thousands of people without electricity.
The Volt Typhoon exploits targeting Versa Director are a stark reminder of the evolving threat landscape. While the focus is often on large-scale attacks like the recent Delta Airlines meltdown, which prompted the CEO to publicly criticize Microsoft and CrowdStrike , it’s important to remember that smaller, more targeted attacks can be equally damaging.
The Volt Typhoon exploits highlight the need for organizations to be vigilant about security, no matter their size or industry.
A similar attack on a critical infrastructure network in the Asia-Pacific region could have devastating consequences.
Origins and Motivations
While the precise origins and motivations of Volt Typhoon remain unclear, evidence suggests a connection to the Chinese government. The group’s targeting of critical infrastructure in the Asia-Pacific region aligns with China’s strategic interests and its increasing focus on cyberespionage.
The group’s activities could be motivated by a desire to gain intelligence on potential adversaries, to disrupt critical infrastructure in times of conflict, or to gain economic advantage.
Data Exfiltration Techniques, Volt typhoon exploits versa director
Volt Typhoon employs a variety of techniques for data exfiltration, including:
- Remote Access Tools (RATs):These tools allow attackers to remotely control infected systems, steal data, and execute commands.
- Command and Control (C&C) Servers:These servers act as communication hubs for attackers, enabling them to manage infected systems and exfiltrate data.
- Data Tunneling:This technique involves hiding data within legitimate network traffic to evade detection by security systems.
- Steganography:This method involves hiding data within seemingly innocuous files, such as images or audio files, to evade detection.
Targets and Victims
Volt Typhoon, a sophisticated cyberespionage campaign, has been actively targeting critical infrastructure and government entities in the United States, specifically focusing on sectors like energy, telecommunications, and transportation. This targeted approach suggests a deliberate and strategic effort to gather sensitive information and potentially disrupt critical operations.
Rationale for Targeting
The choice of targets reflects the strategic importance of these sectors to the United States’ economic and national security. By compromising these critical infrastructure entities, the attackers could gain access to valuable data, disrupt operations, or potentially even manipulate systems for malicious purposes.
Potential Consequences for Targeted Entities
The consequences for targeted entities could be severe, ranging from data breaches and financial losses to operational disruptions and reputational damage. The theft of sensitive information, such as proprietary data, financial records, or critical infrastructure plans, could have significant financial and strategic implications.
Disruptions to critical infrastructure operations could have cascading effects on the economy, national security, and public safety.
Vulnerabilities Exploited by Volt Typhoon
Volt Typhoon has exploited various vulnerabilities to gain access to targeted systems, including:
- Exploiting Software Vulnerabilities:Attackers often leverage known software vulnerabilities to gain initial access to systems. This could involve exploiting unpatched security flaws in operating systems, applications, or network devices.
- Phishing and Social Engineering:Attackers may use phishing emails or social engineering tactics to trick users into revealing sensitive information or granting unauthorized access to systems.
- Weak Passwords and Credentials:Attackers often target systems with weak passwords or reused credentials, which can be easily compromised through brute-force attacks or credential stuffing.
- Misconfigured Security Settings:Attackers may exploit misconfigured security settings on network devices or applications to gain unauthorized access or bypass security controls.
Technical Analysis
Volt Typhoon’s infrastructure and tactics showcase a sophisticated and targeted approach to espionage, underscoring the growing threat posed by advanced persistent threats (APTs). This section delves into the technical aspects of Volt Typhoon’s operations, providing a detailed examination of its infrastructure, malware, reconnaissance techniques, and data exfiltration methods.
Infrastructure
Volt Typhoon’s infrastructure is designed for stealth and persistence, allowing the threat actor to maintain a long-term presence within targeted networks.
- Domain Fronting: Volt Typhoon leverages domain fronting to mask its malicious activity. This technique involves using legitimate domains to host malicious content, making it difficult for security tools to detect and block the traffic. The threat actor registers domains that appear legitimate, but they are actually controlled by Volt Typhoon.
These domains are used to communicate with infected systems, allowing the threat actor to hide their true intentions.
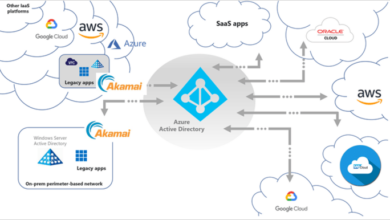
- Cloud-Based Infrastructure: Volt Typhoon heavily relies on cloud-based infrastructure, such as Amazon Web Services (AWS) and Microsoft Azure, to host its command-and-control (C2) servers and data exfiltration channels. This approach offers the threat actor several advantages, including scalability, flexibility, and anonymity.
By using cloud services, Volt Typhoon can easily expand its operations, change its infrastructure, and evade detection.
- VPN Tunnels: To further enhance its stealth, Volt Typhoon uses VPN tunnels to encrypt and obfuscate its communications. These tunnels create a secure and private connection between the threat actor’s infrastructure and the infected systems, making it difficult for security tools to monitor the traffic.
- Multiple Layers of Obfuscation: Volt Typhoon employs multiple layers of obfuscation to make its malicious activity difficult to detect. This includes using code packing, encryption, and other techniques to disguise the true nature of its malware and communications.
Malware
Volt Typhoon utilizes a variety of custom-developed malware to achieve its objectives. These malware families are designed for specific tasks, such as reconnaissance, data exfiltration, and persistence.
The Volt Typhoon exploits targeting the Versa Director are a sobering reminder of the evolving threat landscape. It’s interesting to see how quickly technology becomes obsolete – I was just reading about how Apple has officially classed the iPhone X as vintage, alongside the original HomePod and AirPods.
Just like those devices, the vulnerabilities exploited by Volt Typhoon could be lurking in older systems, making it even more critical to prioritize security updates and patch management.
- Custom Malware Families: Volt Typhoon employs a variety of custom-developed malware families, including those named “BRONZE BUTLER,” “COTTONMOUTH,” and “BLUEBANANA.” These malware families are specifically designed to target critical infrastructure, including power grids, water treatment plants, and transportation systems.
- Persistence Mechanisms: The malware used by Volt Typhoon employs persistence mechanisms to ensure its continued presence on infected systems. This includes techniques such as registry entries, scheduled tasks, and service manipulation. These techniques allow the malware to survive system restarts and reboots, ensuring that the threat actor maintains access to the compromised system.
- Data Exfiltration Capabilities: The malware used by Volt Typhoon is equipped with data exfiltration capabilities, allowing the threat actor to steal sensitive information from compromised systems. This information can include confidential data, system logs, and network traffic.
Reconnaissance and Exploitation
Volt Typhoon employs a range of reconnaissance and exploitation techniques to gain access to targeted networks.
- Vulnerability Scanning: The threat actor conducts vulnerability scans to identify exploitable weaknesses in targeted systems. These scans can reveal vulnerabilities in software, operating systems, and network devices, allowing the threat actor to gain initial access to the network.
- Phishing Attacks: Volt Typhoon utilizes phishing attacks to trick users into providing sensitive information or clicking on malicious links. These attacks often involve sending emails that appear to be from legitimate sources, such as banks or government agencies.
- Exploiting Known Vulnerabilities: Volt Typhoon exploits known vulnerabilities in software and operating systems to gain access to targeted networks. This includes using zero-day exploits, which are vulnerabilities that are unknown to software vendors and have not been patched.
- Credential Harvesting: Volt Typhoon utilizes credential harvesting techniques to steal user credentials, such as passwords and login information. This information can be used to gain access to sensitive data or escalate privileges within the network.
Data Exfiltration
Volt Typhoon employs various methods to exfiltrate stolen data from compromised systems.
- C2 Servers: Volt Typhoon utilizes C2 servers to communicate with infected systems and exfiltrate stolen data. These servers are often hosted in cloud environments, making them difficult to track and identify.
- Data Tunneling: The threat actor uses data tunneling techniques to hide stolen data within legitimate network traffic. This makes it difficult for security tools to detect and block the exfiltration process.
- File Transfer Protocols: Volt Typhoon leverages file transfer protocols, such as FTP and HTTP, to transfer stolen data to its C2 servers. These protocols are often used for legitimate purposes, making it difficult for security tools to distinguish malicious traffic.
- Data Compression and Encryption: To further obfuscate the exfiltration process, Volt Typhoon compresses and encrypts stolen data before transmitting it to its C2 servers. This makes it difficult for security tools to analyze the data and identify its true nature.
Response and Mitigation: Volt Typhoon Exploits Versa Director
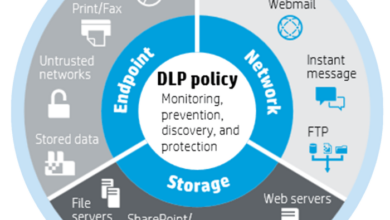
The Volt Typhoon campaign has highlighted the critical need for robust cybersecurity measures and collaborative efforts to counter advanced persistent threats (APTs). Affected entities have implemented various mitigation strategies to minimize the impact of this threat, and government agencies have played a crucial role in coordinating responses and providing guidance.
Steps Taken by Affected Entities
The mitigation measures taken by affected entities vary depending on the nature of the attack and the specific vulnerabilities exploited. However, some common strategies include:
- Disconnecting affected systems:This is a crucial step to prevent further data exfiltration and compromise. It involves isolating compromised systems from the network to contain the spread of the malware.
- Patching vulnerabilities:Applying security patches and updates is essential to address known vulnerabilities that might have been exploited by Volt Typhoon. This involves proactively updating software and operating systems to address known vulnerabilities.
- Implementing security controls:Strengthening security controls, such as firewalls, intrusion detection systems (IDS), and endpoint protection, is vital to detect and prevent future attacks. This includes configuring and maintaining security tools to identify suspicious activity and block malicious traffic.
- Conducting forensic investigations:Thorough forensic analysis is crucial to understand the extent of the compromise and identify the specific tactics, techniques, and procedures (TTPs) used by the attackers. This helps in identifying the source of the attack, the data exfiltrated, and the impact on the organization.
- Recovering compromised data:If data has been exfiltrated, organizations need to take steps to recover the compromised data or mitigate the potential damage. This might involve restoring data from backups or implementing data recovery strategies.
Effectiveness of Mitigation Measures
The effectiveness of mitigation measures depends on factors such as the speed and accuracy of detection, the effectiveness of implemented security controls, and the organization’s ability to recover from the attack.
- Early detection and response:The ability to detect the attack early and respond quickly is crucial in minimizing the impact. Organizations with strong security monitoring and incident response capabilities are better equipped to contain the damage.
- Comprehensive security posture:Organizations with a comprehensive security posture, including robust security controls, vulnerability management, and employee training, are more likely to mitigate the threat effectively. This involves implementing a layered approach to security that encompasses multiple defense mechanisms.
- Data recovery and resilience:The ability to recover compromised data and maintain business continuity is essential. Organizations with effective data backup and recovery strategies are better positioned to withstand the impact of data breaches.
Role of Government Agencies
Government agencies play a critical role in responding to cyber threats, including the Volt Typhoon campaign. Their responsibilities include:
- Sharing threat intelligence:Government agencies collect and share threat intelligence with the private sector, providing insights into attacker TTPs, malware variants, and potential targets. This enables organizations to better understand the threat landscape and proactively defend against attacks.
- Developing cybersecurity standards and guidelines:Government agencies develop and promote cybersecurity standards and best practices to enhance the overall security posture of critical infrastructure and organizations. This helps organizations adopt robust security measures and improve their resilience against cyberattacks.
- Coordinating response efforts:Government agencies play a crucial role in coordinating response efforts between different organizations, including law enforcement, intelligence agencies, and cybersecurity firms. This facilitates information sharing, resource allocation, and collaborative action to address the threat effectively.
- Sanctioning attackers:Government agencies may impose sanctions on individuals or entities involved in cyberattacks to deter future malicious activities. This involves taking legal and economic actions to hold perpetrators accountable for their actions.
Recommendations for Preventing Future Attacks
To prevent future attacks like Volt Typhoon, organizations should consider the following recommendations:
- Implement a zero-trust security model:A zero-trust model assumes that no user or device can be trusted by default. It requires strict authentication, authorization, and continuous monitoring of all network traffic and user activity.
- Invest in security awareness training:Educating employees about cybersecurity best practices, social engineering tactics, and phishing scams is crucial to prevent human error from becoming a vulnerability. This involves regular training programs and awareness campaigns.
- Strengthen incident response capabilities:Organizations should develop and test their incident response plans regularly to ensure they can respond effectively to cyberattacks. This involves establishing clear procedures, assigning roles and responsibilities, and conducting simulations to test their readiness.
- Collaborate with government agencies and industry partners:Sharing information and collaborating with government agencies and other organizations is essential to stay ahead of evolving threats. This includes participating in information sharing forums, joining industry groups, and engaging with cybersecurity experts.
- Embrace a proactive security approach:Instead of waiting for attacks to occur, organizations should adopt a proactive security approach that involves continuously monitoring for vulnerabilities, patching systems regularly, and implementing robust security controls. This requires a culture of security awareness and a commitment to ongoing security improvements.
Impact on Cybersecurity
Volt Typhoon, a sophisticated and persistent threat actor, highlights the evolving nature of cyberattacks and their potential to disrupt critical infrastructure. This incident serves as a stark reminder of the need for robust cybersecurity measures to protect vital systems and data from malicious actors.
Enhanced Security Measures
The emergence of Volt Typhoon necessitates a comprehensive approach to cybersecurity, encompassing a range of enhanced measures.
- Strengthening Network Defenses:Implementing multi-factor authentication, network segmentation, and intrusion detection systems can help mitigate the risk of unauthorized access and data breaches.
- Improving Threat Intelligence:Organizations must actively monitor threat intelligence feeds, analyze suspicious activity, and proactively identify potential vulnerabilities to mitigate the impact of attacks.
- Enhancing Incident Response Capabilities:Developing robust incident response plans, conducting regular simulations, and ensuring prompt communication with stakeholders are crucial for effectively managing cyber incidents.
- Prioritizing Employee Training:Educating employees on cybersecurity best practices, phishing awareness, and the importance of data security is essential for preventing human error and social engineering attacks.
Best Practices for Protecting Critical Infrastructure
Protecting critical infrastructure from cyberattacks requires a multifaceted approach that goes beyond traditional cybersecurity measures.
- Implementing Zero Trust Security:This approach assumes that no user or device can be trusted by default and requires strict verification and authorization before granting access to sensitive systems and data.
- Utilizing Advanced Threat Detection Technologies:Employing artificial intelligence (AI) and machine learning (ML) algorithms can help detect and respond to advanced threats that traditional security tools may miss.
- Strengthening Supply Chain Security:Ensuring the security of software and hardware components used in critical infrastructure is crucial for preventing attacks that exploit vulnerabilities in the supply chain.
- Promoting Collaboration and Information Sharing:Fostering collaboration between government agencies, industry partners, and cybersecurity researchers is essential for sharing threat intelligence and best practices to enhance collective security.
Importance of Threat Intelligence and Proactive Security
In the face of sophisticated threats like Volt Typhoon, proactive security measures and threat intelligence are paramount.
- Continuous Monitoring and Analysis:Organizations must actively monitor their networks for suspicious activity, analyze threat intelligence feeds, and stay informed about emerging threats and vulnerabilities.
- Proactive Vulnerability Management:Identifying and patching vulnerabilities in a timely manner is crucial for preventing attackers from exploiting them. This includes conducting regular vulnerability assessments and implementing automated patching mechanisms.
- Developing Threat Hunting Capabilities:Proactively searching for and identifying malicious activity within an organization’s systems and networks can help detect and neutralize threats before they cause significant damage.
- Investing in Security Expertise:Organizations need to invest in skilled cybersecurity professionals who can develop and implement robust security measures, respond to incidents, and stay ahead of evolving threats.
The Role of Versa Director
Versa Director is a network security platform that plays a crucial role in defending against cyberattacks like Volt Typhoon. It provides a comprehensive approach to security, integrating multiple security technologies and functionalities to enhance overall security posture.
Capabilities of Versa Director in Addressing Cybersecurity Threats
Versa Director offers a wide range of capabilities that are particularly relevant to mitigating threats like Volt Typhoon. These capabilities include:
- SD-WAN (Software-Defined Wide Area Networking):Versa Director’s SD-WAN capabilities enable organizations to establish secure and reliable connections between their locations, even across geographically dispersed networks. This is crucial for organizations with a global presence, as it helps to ensure that all branches and offices are protected from attacks.
- Network Segmentation:Versa Director allows organizations to segment their networks into smaller, isolated zones. This helps to limit the impact of a security breach by preventing attackers from moving laterally within the network. This segmentation strategy is particularly effective in preventing the spread of malware like that used in Volt Typhoon attacks.
- Zero Trust Security:Versa Director incorporates zero-trust principles, which assume that no user or device can be trusted by default. This approach requires all users and devices to be authenticated and authorized before they are granted access to network resources. This helps to prevent unauthorized access and limit the damage that can be caused by a successful attack.
- Advanced Threat Detection and Prevention:Versa Director incorporates advanced threat detection and prevention technologies, such as intrusion detection and prevention systems (IDS/IPS) and next-generation firewalls (NGFWs). These technologies can identify and block malicious traffic, including that associated with Volt Typhoon attacks. This helps to prevent the initial infection of systems and devices.
- Security Orchestration and Automation:Versa Director can automate many security tasks, such as threat intelligence sharing, incident response, and remediation. This helps to improve the efficiency and effectiveness of security operations and reduce the time it takes to respond to attacks. This automation capability is essential for handling complex and fast-evolving threats like Volt Typhoon.
Benefits of Using Versa Director to Mitigate Volt Typhoon-like Attacks
Versa Director provides several benefits for organizations looking to mitigate Volt Typhoon-like attacks:
- Enhanced Security Posture:Versa Director’s comprehensive approach to security helps organizations to strengthen their overall security posture. By combining multiple security technologies and functionalities, Versa Director provides a more robust defense against cyberattacks.
- Improved Threat Detection and Prevention:Versa Director’s advanced threat detection and prevention capabilities help to identify and block malicious traffic, including that associated with Volt Typhoon attacks. This helps to prevent the initial infection of systems and devices.
- Reduced Risk of Data Breaches:Versa Director’s security features, such as network segmentation and zero-trust security, help to reduce the risk of data breaches by limiting the impact of a successful attack. This is particularly important for organizations that handle sensitive data.
- Improved Incident Response:Versa Director’s security orchestration and automation capabilities help to improve incident response times by automating many security tasks. This allows security teams to focus on more strategic activities, such as threat analysis and remediation.
Examples of How Versa Director Can Be Used to Enhance Security Posture
Versa Director can be used in various ways to enhance security posture and mitigate Volt Typhoon-like attacks. Here are a few examples:
- Segmenting Critical Infrastructure Networks:Organizations can use Versa Director to segment their critical infrastructure networks, such as those controlling power grids or water treatment plants, from other parts of the network. This helps to isolate these critical systems from potential attacks and reduce the risk of disruption.
- Implementing Zero Trust Security Policies:Organizations can use Versa Director to implement zero-trust security policies, which require all users and devices to be authenticated and authorized before they are granted access to network resources. This helps to prevent unauthorized access and limit the damage that can be caused by a successful attack.
- Deploying Advanced Threat Detection and Prevention Technologies:Organizations can use Versa Director to deploy advanced threat detection and prevention technologies, such as intrusion detection and prevention systems (IDS/IPS) and next-generation firewalls (NGFWs). These technologies can identify and block malicious traffic, including that associated with Volt Typhoon attacks.
- Automating Security Tasks:Organizations can use Versa Director to automate many security tasks, such as threat intelligence sharing, incident response, and remediation. This helps to improve the efficiency and effectiveness of security operations and reduce the time it takes to respond to attacks.