Bluesky Grapples with Prolonged Cyberattack as Sophisticated DDoS Disrupts Service Across its Platform.
Bluesky’s website and application are currently experiencing significant and prolonged service interruptions, stretching into Friday, following an extensive cyberattack that began earlier in the week. Rose Wang, the chief operating officer for the decentralized social media platform, has formally attributed these widespread issues to an ongoing and sophisticated Distributed Denial-of-Service (DDoS) attack. The incident has left users struggling with intermittent access and functionality, casting a spotlight on the vulnerabilities faced by even emerging social networks in today’s complex cyber threat landscape.
The Cyberattack Unfolds: A Chronology of Disruptions
The initial signs of distress on the Bluesky network emerged on Monday, April 15, around 8:40 p.m. ET, marking the genesis of what would become a multi-day ordeal for the platform and its burgeoning user base. While initial reports were vague, the company later confirmed on Thursday evening that the persistent service outages were indeed the result of a "sophisticated Distributed Denial-of-Service (DDoS) attack." This official acknowledgment came after a period of user frustration and speculation, as the platform struggled to maintain stable operations.
Early on Wednesday, well before the full scope of the situation was publicly detailed, Bryan Newbold, a protocol engineer at Bluesky, provided an early, candid glimpse into the internal struggle, remarking around 3:46 a.m. ET, "oof, our services are getting hit pretty hard tonight." This informal but telling statement underscored the severity of the challenge the Bluesky team was already confronting.

As the attack persisted into Friday, Bluesky’s platform continued to exhibit intermittent functionality. Users reported a range of difficulties, from sluggish loading times to outright error messages preventing access to core features. The company itself acknowledged that the attack was "impacting our operations, with users experiencing intermittent interruptions in service for their feeds, notifications, threads, and search." This broad impact highlights the comprehensive nature of the DDoS assault, targeting multiple layers of the platform’s user-facing infrastructure.
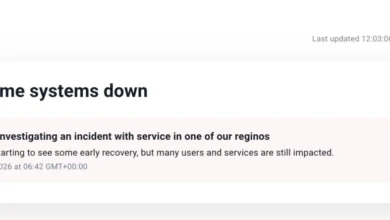
In an effort to keep its community informed, Bluesky committed to providing another update on the status of the attack and its mitigation efforts by 1 p.m. ET on Friday. However, compounding the communication challenges, the network’s dedicated status page, status.bsky.app, which is typically the primary source for real-time operational updates, was itself intermittently inaccessible. A notable typo, "investigating an incident with service in one of our reginos [sic]," observed on a functioning instance of the status page, inadvertently conveyed the hurried and pressured environment in which the Bluesky team was operating.
Understanding Distributed Denial-of-Service (DDoS) Attacks
A Distributed Denial-of-Service (DDoS) attack represents a particularly insidious form of cyber warfare, designed not to infiltrate systems or steal data, but to overwhelm and cripple them. These attacks typically involve an attacker orchestrating a vast network of compromised computers, often referred to as a "botnet," to flood a target server or network with an immense volume of illegitimate traffic. The sheer deluge of junk data overwhelms the target’s capacity, exhausting its resources such as bandwidth, CPU, and memory, thereby rendering the legitimate services unavailable to genuine users.
Unlike data breaches, which focus on unauthorized access to sensitive information, DDoS attacks aim squarely at disrupting availability. While they do not directly compromise private user data, their impact can be profound. For a company, a sustained DDoS attack can lead to significant financial losses due to downtime, damage to reputation, loss of user trust, and considerable costs associated with mitigation and recovery. For users, it translates directly into an inability to access services they rely on, leading to frustration and disengagement.

DDoS attacks vary in sophistication and scale. Volumetric attacks, the most common type, flood the network layer with massive amounts of traffic. Protocol attacks exploit weaknesses in network protocols, consuming server resources. Application-layer attacks target specific web application vulnerabilities, aiming to crash them with seemingly legitimate but malicious requests. The "sophisticated" nature described by Bluesky suggests a multi-vector attack, employing various techniques simultaneously to maximize disruption and complicate defense.
Historically, DDoS attacks have plagued internet services for decades, evolving in complexity and magnitude. Notable incidents include the 2016 Mirai botnet attack, which leveraged IoT devices to take down major internet infrastructure provider Dyn, affecting numerous prominent websites. More recently, attacks have become more frequent and powerful, with some volumetric attacks exceeding terabits per second, posing an existential threat to smaller platforms and significant challenges for even the largest tech giants. The average cost of a single DDoS attack for businesses can range from tens of thousands to hundreds of thousands of dollars, factoring in lost revenue, remediation efforts, and reputational damage.
Bluesky’s Response and the User Experience Under Siege
In the face of this persistent assault, Bluesky has focused its public statements on two critical points: acknowledging the attack’s nature and reassuring users about data security. The company explicitly stated it has not observed "any evidence of unauthorized access to private data," a crucial distinction that helps alleviate fears of a privacy breach, which often accompanies cyber incidents. This reassurance is vital for maintaining user confidence, especially for a platform still in its growth phase.
However, the user experience during this period has been undeniably challenging. The intermittent nature of the outages means that some users might occasionally access the platform, only to encounter severe performance degradation or error messages when attempting specific actions. Common error messages reported include "This feed is currently receiving high traffic and is temporarily unavailable. Please try again later. Message from server: Rate Limit Exceeded." This message directly indicates the server’s inability to process the legitimate requests due to the overwhelming volume of junk traffic, a hallmark of a successful DDoS attack.

Such issues have impacted core functionalities, making it difficult for users to browse their personalized feeds, receive notifications, engage in threads, or utilize the search function. Even popular public feeds, such as "Discover" or the official "Bluesky Team’s feed," have been prone to these "Rate Limit Exceeded" errors, while users’ personal feeds might function sporadically. Attempts to access individual user profiles have also frequently resulted in error messages, forcing users to refresh and retry, often without success. This inconsistent and unreliable service not only frustrates users but also severely impedes their ability to interact with the platform as intended, undermining the very purpose of a social network. The initial lack of an estimated time for a fix further exacerbated user uncertainty, although the promise of a Friday afternoon update signals an ongoing effort to restore stability and communicate progress.
The Decentralized Advantage (and Vulnerability): The AT Protocol
Bluesky’s foundation on the AT Protocol (Authenticated Transfer Protocol) offers a fascinating case study in the resilience and vulnerabilities of decentralized social networks. The AT Protocol is designed to be an open, federated protocol, meaning that different "servers" or "instances" can host user data and interact, theoretically providing a more robust and censorship-resistant architecture than traditional centralized platforms.
Notably, while Bluesky’s main infrastructure has been severely impacted, other communities and services that run their own infrastructure on the underlying AT Protocol have continued to function. A prime example is Blacksky, a community built on the AT Protocol, which reported no significant disruptions to its services. This distinction is crucial: the DDoS attack appears to be targeting Bluesky’s specific infrastructure (its primary "PDS" or Personal Data Server and associated services), rather than the AT Protocol itself.
The Blacksky team informed TechCrunch that the Bluesky outage has led to a "significant spike" in migration requests from Bluesky users over the past 12 hours. This surge suggests that users, frustrated by Bluesky’s downtime, are exploring alternative AT Protocol-based services, a testament to the protocol’s federated design. This trend has been actively promoted by various users, developers, and other ATmosphere founders, such as Sebastian at Eurosky, highlighting the protocol’s inherent ability to allow users to "move" their identities and data to different providers without losing their social graph.

This situation presents a dual narrative: it exposes the vulnerability of any single point of infrastructure, even within a decentralized ecosystem, to targeted cyberattacks. However, it also underscores the potential strength of the AT Protocol’s architecture. By allowing multiple independent services to exist and interoperate, the protocol offers a degree of resilience where the failure of one instance does not necessarily bring down the entire network. Users retain agency to migrate their data, a feature largely absent in centralized platforms. This incident, therefore, serves as a real-world stress test for the practical implications of decentralization in the face of sophisticated cyber threats.
Broader Implications for Bluesky and the Social Media Landscape
The prolonged DDoS attack on Bluesky carries significant implications for the platform’s immediate future and its standing within the competitive social media landscape. For a relatively new platform that recently opened its doors to the public after a lengthy invite-only phase, maintaining consistent uptime and demonstrating reliability is paramount for user acquisition and retention. Prolonged outages can severely hamper growth, erode user trust, and deter potential new users from joining. Users, particularly those migrating from more established (and often more resilient) platforms, expect a stable and functional experience.
The incident also highlights the ongoing, relentless battle against cyberattacks that all online services face. While major platforms like X (formerly Twitter) or Facebook have vast resources dedicated to cybersecurity, emerging players like Bluesky must rapidly scale their defenses to meet increasingly sophisticated threats. This attack serves as a stark reminder that even with innovative decentralized architectures, the underlying infrastructure still needs robust protection against malicious actors.
From a strategic perspective, repeated or severe outages could damage Bluesky’s brand reputation, potentially positioning it as less reliable than its centralized counterparts, despite its technological advantages in decentralization. This perception could hinder its ability to attract and retain a critical mass of users, which is essential for the network effect crucial to social media success. Furthermore, the cost of mitigating such attacks, both in terms of direct technical expenses and indirect losses from user churn, can be substantial for a growing company.

The silver lining, if any, lies in the AT Protocol’s federated nature. The ability of users to migrate to other AT Protocol-based services during Bluesky’s downtime validates a core promise of decentralization – resilience through distributed infrastructure and user sovereignty over their data. This could, paradoxically, strengthen the broader AT Protocol ecosystem by demonstrating its flexibility and encouraging users to understand and utilize its decentralized features. However, it also places pressure on Bluesky, as a flagship application, to fortify its own infrastructure to remain competitive as a primary entry point to this ecosystem.
Moving Forward: Mitigation and Future Resilience
In the immediate aftermath of a DDoS attack, mitigation strategies typically involve a multi-pronged approach. Bluesky’s team is undoubtedly engaged in identifying the attack vectors, filtering malicious traffic, and working with its internet service providers (ISPs) and cloud infrastructure partners to absorb and repel the assault. This includes deploying advanced DDoS protection services, which can detect and automatically divert or scrub malicious traffic before it reaches the core servers. Scaling up server resources to withstand higher traffic loads is another common, albeit expensive, immediate response.
Looking beyond the current crisis, Bluesky will likely need to significantly bolster its long-term cybersecurity posture. This could involve investing in more robust DDoS protection infrastructure, diversifying its server locations and providers, implementing advanced traffic analysis and threat intelligence, and continually auditing its network architecture for potential vulnerabilities. For a decentralized platform, fostering a resilient ecosystem also involves encouraging and supporting the growth of multiple, robust Personal Data Servers (PDS) that users can choose from, further distributing the load and reducing the impact of a targeted attack on any single entity.
The incident underscores that cybersecurity is not a one-time fix but an ongoing, adaptive process. As attack methods evolve, so too must defenses. For Bluesky, this prolonged cyberattack is a critical test of its operational resilience and its commitment to building a stable and trustworthy platform for the future of decentralized social networking. The outcome of its current mitigation efforts, and its subsequent actions to prevent similar incidents, will undoubtedly shape user perception and the platform’s trajectory in the dynamic world of online communication.