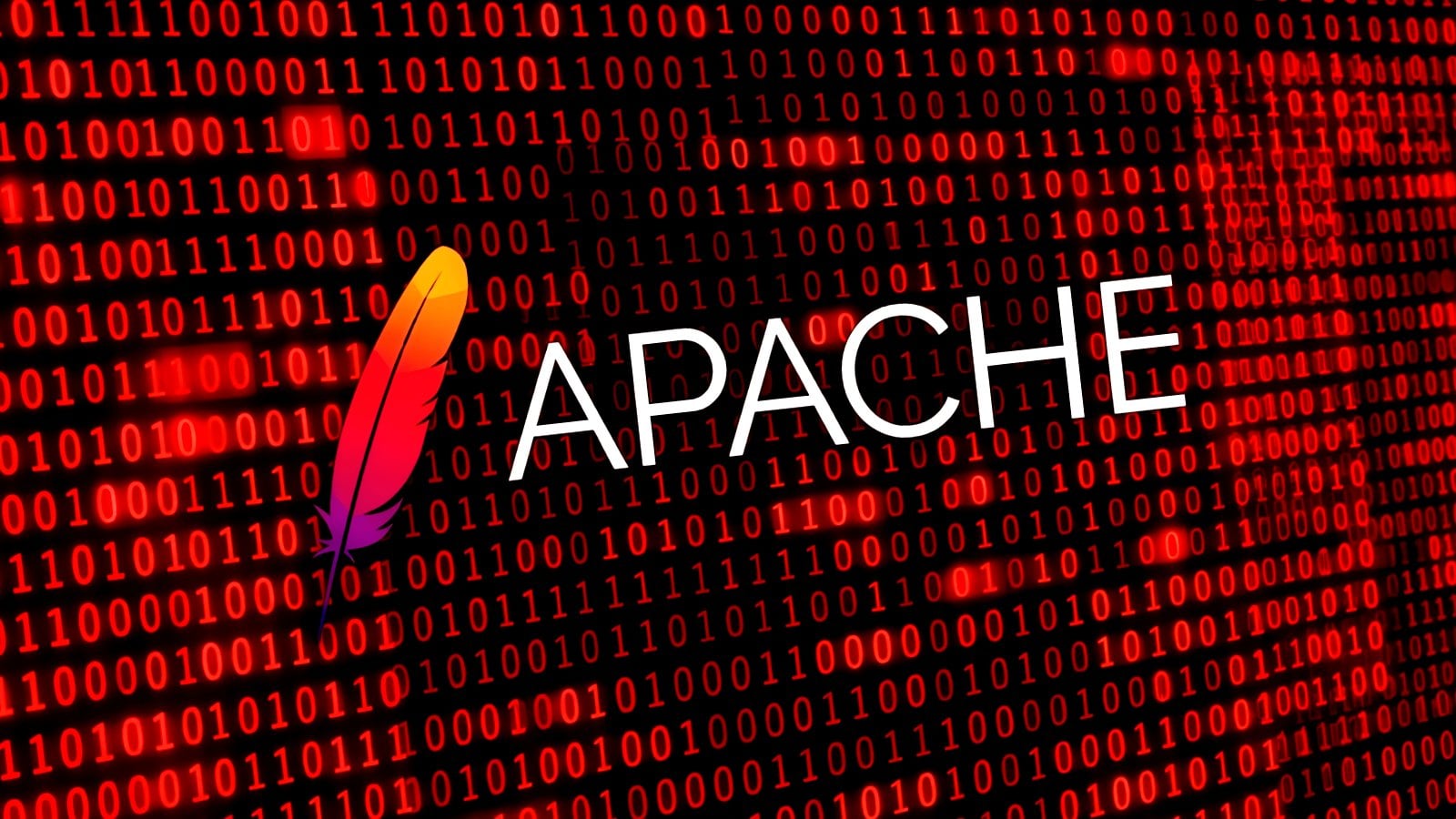
CISA Warns of Actively Exploited Apache ActiveMQ Vulnerability, CVE-2026-34197, Posing Significant Risk to Federal Agencies

The U.S. Cybersecurity and Infrastructure Security Agency (CISA) issued a stern warning on Thursday, April 16, 2026, revealing that a critical security flaw within Apache ActiveMQ, a widely used open-source message broker, is now being actively exploited by malicious actors. This vulnerability, identified as CVE-2026-34197, was patched by Apache maintainers earlier this month, but its 13-year undetected presence and recent exploitation highlight a significant and immediate threat to organizations reliant on this essential middleware.
Apache ActiveMQ serves as a cornerstone for asynchronous communication in countless applications, enabling disparate software systems to exchange data reliably and efficiently. Its popularity across various industries, including government, finance, and technology, makes a vulnerability of this magnitude a matter of national security concern. The fact that this flaw remained dormant for over a decade, only to be discovered and subsequently weaponized, underscores the evolving landscape of cyber threats and the persistent efforts of threat actors to uncover and exploit latent weaknesses.
Discovery and Technical Underpinnings of CVE-2026-34197
The discovery of CVE-2026-34197 is attributed to Naveen Sunkavally, a researcher at Horizon3.ai, who leveraged the capabilities of the Claude AI assistant in his investigation. Sunkavally detailed that the vulnerability arises from insufficient input validation within the Apache ActiveMQ system. This deficiency allows authenticated threat actors to inject malicious code, ultimately leading to the execution of arbitrary commands on the compromised server. The exploitation vector, while requiring some level of authentication, is considered highly impactful due to the pervasive use of ActiveMQ and the critical nature of the data it handles.
Apache maintainers addressed the vulnerability on March 30, 2026, releasing patches for ActiveMQ Classic versions 6.2.3 and 5.19.4. The urgency of this patch cannot be overstated, especially given the agency’s proactive stance on known exploited vulnerabilities.
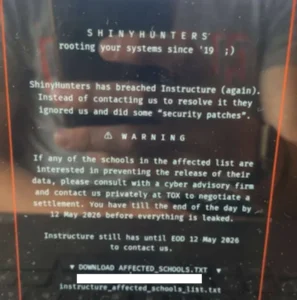
CISA’s Escalated Response: Adding to the KEV Catalog
In response to the escalating threat, CISA officially added CVE-2026-34197 to its highly critical Known Exploited Vulnerabilities (KEV) Catalog. This designation triggers mandatory actions for U.S. Federal Civilian Executive Branch (FCEB) agencies, compelling them to implement necessary patches and mitigations within a strict two-week deadline, by April 30, 2026. This directive is in accordance with Binding Operational Directive (BOD) 22-01, which mandates timely remediation of vulnerabilities identified as actively exploited.
CISA’s alert emphasized the significant risks associated with this vulnerability, stating, "This type of vulnerability is a frequent attack vector for malicious cyber actors and poses significant risks to the federal enterprise." The agency’s directive also extends to cloud services, urging agencies to follow applicable BOD 22-01 guidance or to discontinue the use of the product if mitigations are not feasible.
The Pervasive Reach of Apache ActiveMQ
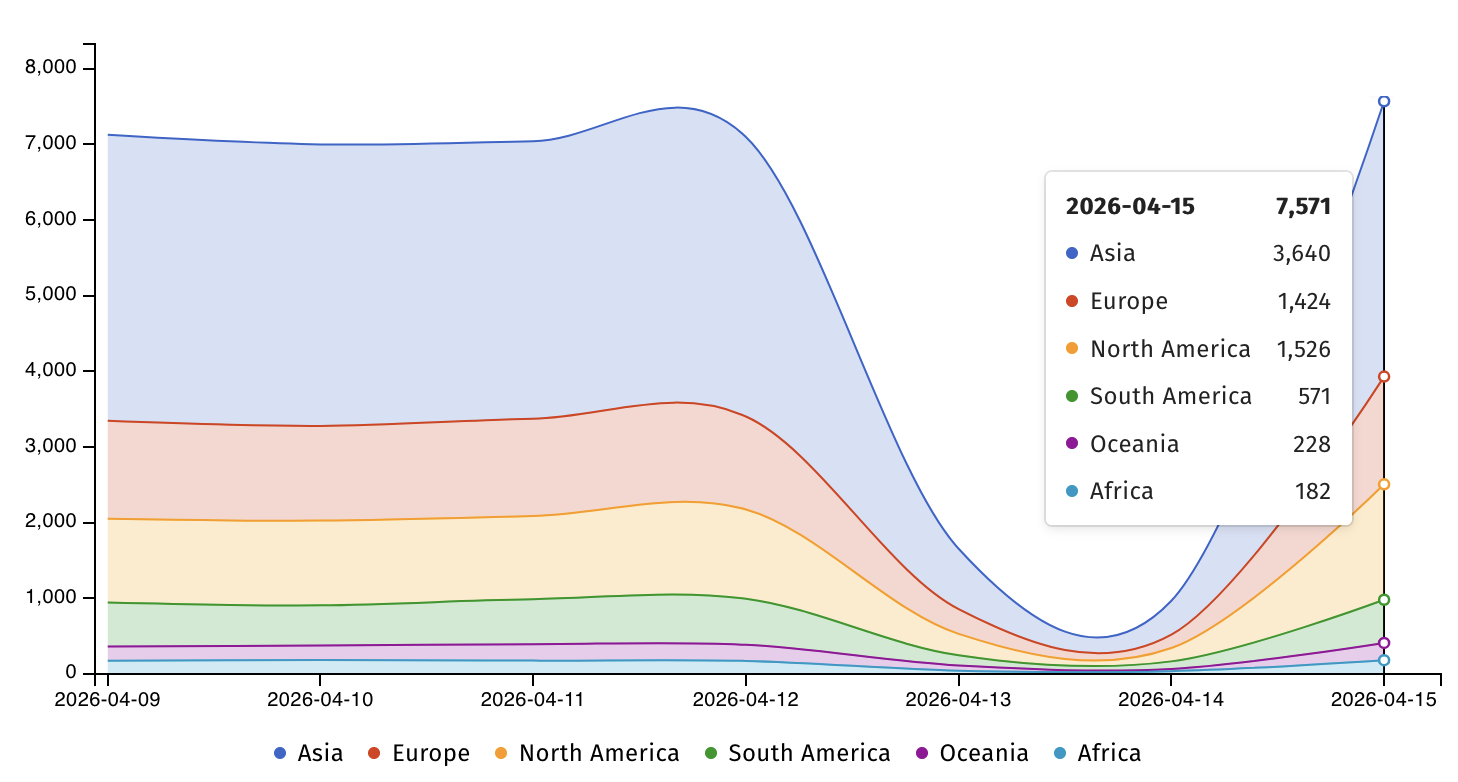
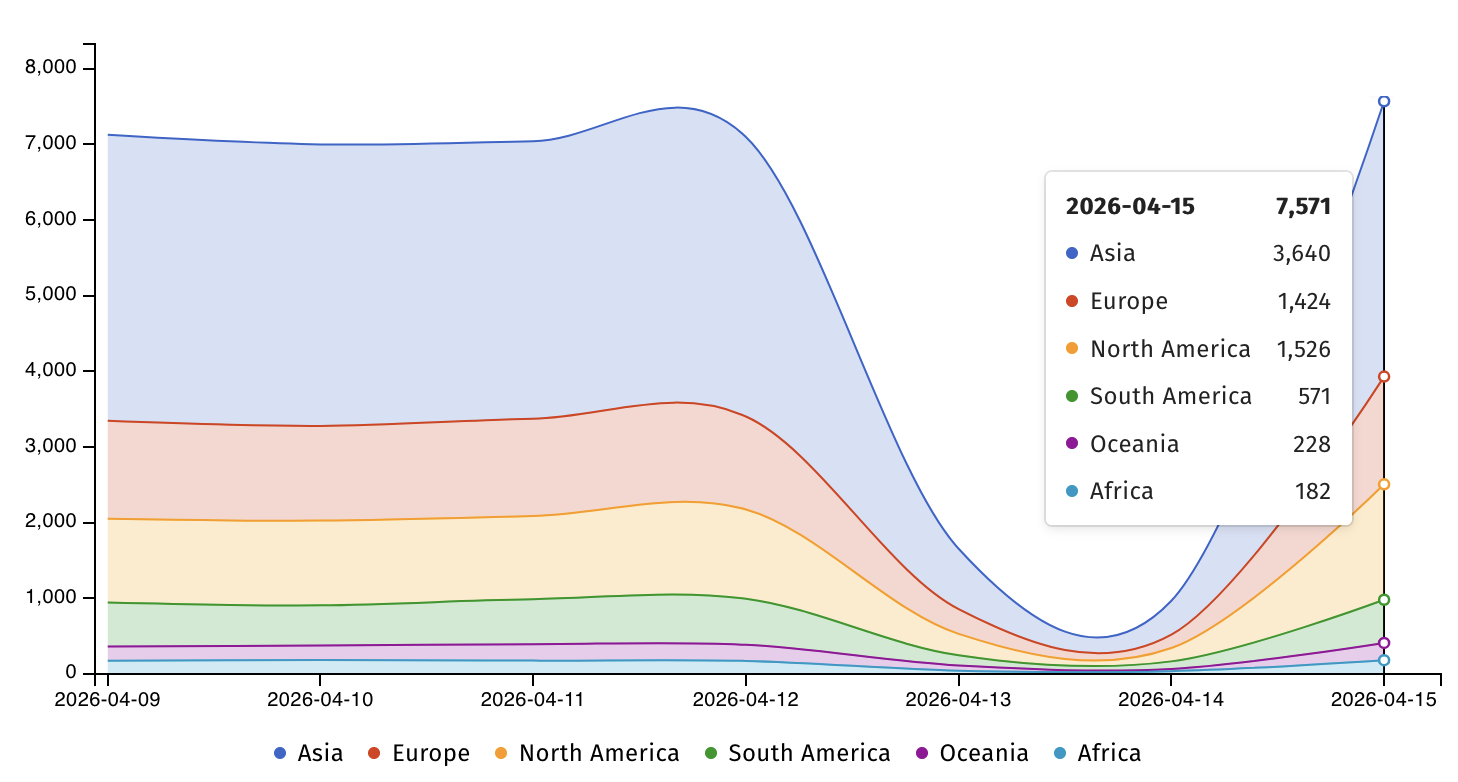
The widespread deployment of Apache ActiveMQ servers worldwide presents a substantial attack surface. According to data from the threat monitoring service ShadowServer, there are currently over 7,500 Apache ActiveMQ servers exposed online. This figure, while a snapshot, indicates a significant number of potential targets that could be vulnerable if not promptly patched. The geographical distribution of these exposed servers, as tracked by ShadowServer, suggests a global exposure, making this a concern for international organizations as well.
Exploitation Tactics and Detection
Horizon3 researchers have provided crucial insights into how to detect signs of exploitation. They recommend a thorough analysis of ActiveMQ broker logs, specifically looking for suspicious connections that utilize the brokerConfig=xbean:http:// query parameter in conjunction with the internal transport protocol, VM. Identifying these patterns can be critical for organizations to determine if they have been compromised.
The Horizon3 team further warned that organizations running ActiveMQ should treat this vulnerability as a high priority. Their advisory highlighted that "ActiveMQ has been a repeated target for real-world attackers, and methods for exploitation and post-exploitation of ActiveMQ are well-known." This historical context adds another layer of concern, suggesting that attackers are already familiar with the ActiveMQ ecosystem and can leverage existing playbooks for further compromise.

A Pattern of Vulnerabilities in Apache ActiveMQ
CVE-2026-34197 is not an isolated incident for Apache ActiveMQ. CISA has previously identified and added two other Apache ActiveMQ vulnerabilities to its KEV Catalog:
- CVE-2023-46604: This vulnerability was notably exploited by the TellYouThePass ransomware gang as a zero-day flaw, demonstrating the immediate and devastating impact of such exploits.
- CVE-2016-3088: This earlier vulnerability also saw exploitation in the wild, indicating a long-standing history of security challenges within the ActiveMQ ecosystem.
The recurrence of actively exploited vulnerabilities in a critical piece of infrastructure like ActiveMQ raises questions about the long-term security posture of the software and the effectiveness of its development and testing processes. The fact that a vulnerability could remain undetected for 13 years is particularly concerning, suggesting potential systemic issues in code review or security auditing.
Broader Implications for the Cybersecurity Landscape
The active exploitation of CVE-2026-34197 serves as a stark reminder of the constant threat posed by sophisticated cyber adversaries. For private-sector organizations, CISA’s call to action is equally pertinent, even though BOD 22-01 specifically targets federal agencies. The agency urged private-sector defenders to prioritize patching this vulnerability and to bolster their network defenses as swiftly as possible.
The implications of such vulnerabilities extend beyond direct system compromise. Successful exploitation can lead to data breaches, denial-of-service attacks, the deployment of ransomware, and the establishment of persistent backdoors for future access. In critical infrastructure sectors, the impact could be far more severe, potentially disrupting essential services.
The discovery of this vulnerability using AI tools like Claude also signals a new era in cybersecurity research, where artificial intelligence is increasingly being employed by both defenders and attackers. This dual-use capability necessitates a continuous evolution of security strategies and the development of advanced threat detection and response mechanisms.
The Path Forward: Mitigation and Resilience
Organizations that rely on Apache ActiveMQ must act with extreme urgency. The recommended mitigation steps include:
- Immediate Patching: Apply the security patches released by Apache for ActiveMQ Classic versions 6.2.3 and 5.19.4.
- Log Analysis: Conduct thorough analysis of broker logs for indicators of compromise, as outlined by Horizon3 researchers.
- Security Audits: Perform comprehensive security audits of ActiveMQ deployments and related infrastructure.
- Network Segmentation: Implement robust network segmentation to limit the lateral movement of attackers in the event of a compromise.
- Access Control: Enforce strict access control policies for ActiveMQ instances, ensuring only authorized personnel and systems can connect.
- Vendor Guidance: Adhere to all vendor-provided mitigation instructions and guidance.
- Alternative Solutions: If patching or mitigation is not immediately feasible, consider discontinuing the use of the vulnerable product or migrating to more secure alternatives.
The ongoing threat landscape demands a proactive and vigilant approach to cybersecurity. The active exploitation of CVE-2026-34197 by threat actors, coupled with CISA’s directive, underscores the critical importance of maintaining up-to-date security measures and responding swiftly to emerging threats. The long-standing nature of this particular vulnerability serves as a potent lesson in the need for continuous vigilance and robust vulnerability management practices across all software systems.