Iran-Backed Hacktivist Group Handala Claims Responsibility for Widespread Cyberattack Against Medical Technology Giant Stryker
A sophisticated cyberattack, attributed to an Iran-linked hacktivist group known as Handala, has crippled the global operations of Stryker, a prominent medical technology company. The group claims to have executed a data-wiping attack, impacting over 200,000 systems, servers, and mobile devices across 79 countries where Stryker operates. This incident has led to the shutdown of offices worldwide and significant disruptions for healthcare providers relying on Stryker’s essential medical equipment and supplies.
The scale of the attack became apparent with reports emerging from Ireland, a major operational hub for Stryker outside the United States. Over 5,000 workers in the region were reportedly sent home as the company grappled with the fallout. Concurrently, a voicemail message at Stryker’s U.S. headquarters in Kalamazoo, Michigan, indicated a "building emergency," a veiled reference to the ongoing cyber crisis.
Stryker, a publicly traded company (NYSE: SYK) with reported global sales of $25 billion last year, is a critical player in the medical and surgical equipment market. Its extensive product portfolio includes orthopedic implants, surgical instruments, neurotechnology, and spine systems, serving hospitals and healthcare facilities across the globe. The company employs approximately 56,000 individuals in 61 countries, underscoring the far-reaching implications of this cyber intrusion.
The Handala Manifesto and Alleged Motives
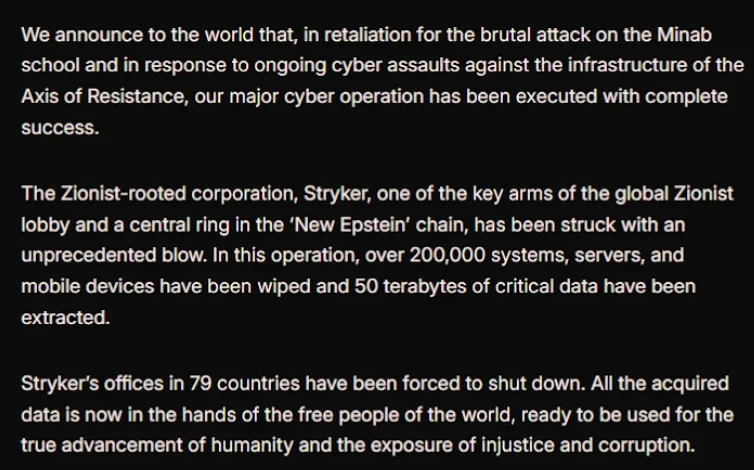
In a detailed statement disseminated via Telegram, the Handala group asserted its responsibility for the widespread disruption. The group claimed to have erased data from a vast number of Stryker’s digital assets, stating, "All the acquired data is now in the hands of the free people of the world, ready to be used for the true advancement of humanity and the exposure of injustice and corruption." This rhetoric suggests a motive rooted in information warfare and a desire to expose perceived wrongdoing.
Handala explicitly linked its attack to a retaliatory action against a missile strike that occurred on February 28th. This strike reportedly hit an Iranian school, resulting in the deaths of at least 175 individuals, predominantly children. Subsequent reporting by The New York Times, citing an ongoing military investigation, attributed the deadly Tomahawk missile strike to the United States. This connection highlights a potential geopolitical dimension to the cyberattack, positioning Handala as an instrument of Iranian state-sponsored cyber operations.
Attribution and Technical Sophistication
The attribution of the attack to Handala is bolstered by research from cybersecurity firm Palo Alto Networks. In a recent profile of Iranian cyber activities, Palo Alto Networks identified Handala as a group with links to Iran’s Ministry of Intelligence and Security (MOIS). The firm assesses Handala as one of several online personas utilized by Void Manticore, an entity with documented ties to the MOIS, suggesting a state-backed operation. Handala reportedly emerged in late 2023, and its activities have previously included hack-and-leak operations, primarily targeting Israel, but also extending to other regions when strategically advantageous.
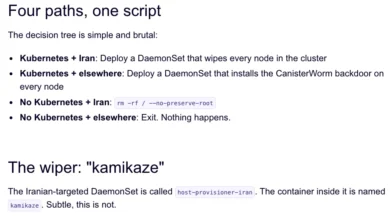
The technical execution of the attack appears to have been particularly effective and alarming. While traditional wiper malware is designed to overwrite data, evidence suggests Handala leveraged a more sophisticated approach. A trusted source with knowledge of the incident, speaking anonymously to KrebsOnSecurity, indicated that the perpetrators likely utilized Microsoft Intune, a cloud-based device management service, to issue a "remote wipe" command. This capability allowed them to remotely erase data from all connected devices, including those owned by employees and managed by Stryker’s IT infrastructure. The use of Intune, a legitimate IT management tool, highlights the attackers’ ability to exploit trusted systems for malicious purposes, a tactic often employed by advanced persistent threat (APT) actors.
Supporting this technical assessment, discussions on cybersecurity forums, including Reddit, revealed that Stryker employees were reportedly instructed to urgently uninstall Intune, further corroborating its role in the attack. This reliance on a widespread enterprise management tool amplifies the potential impact and underscores the challenge of securing complex, interconnected IT environments.
Broader Targeting and Ideological Framing
Palo Alto Networks’ research indicates that Handala’s cyber operations have historically focused on Israel, with occasional expansions to other targets when aligned with specific agendas. The group has previously claimed responsibility for attacks against fuel systems in Jordan and an Israeli energy exploration company. The firm characterizes Handala’s recent activities as "opportunistic and ‘quick and dirty’," often exploiting supply-chain vulnerabilities to reach downstream victims. The posting of "proof" of their exploits serves to amplify their credibility and intimidate targets.
In its manifesto, Handala referred to Stryker as a "Zionist-rooted corporation." This characterization may stem from Stryker’s 2019 acquisition of OrthoSpace, an Israeli medical device company. This framing aligns with the broader geopolitical narratives often employed by state-sponsored or state-aligned cyber actors.
Immediate Operational Impact and Employee Disruption
The immediate consequences of the attack have been severe for Stryker’s operations and its global workforce. News reports from the Irish Examiner detailed how Stryker staff in Cork were communicating via WhatsApp for updates on when they could return to work. An unnamed employee described the network as completely down, with even personal devices running Microsoft Outlook being wiped. The login pages on compromised devices were reportedly defaced with the Handala logo, serving as a digital calling card for the attackers.
The "building emergency" message at U.S. headquarters, coupled with the mass work-from-home directives in Ireland, paints a picture of a company struggling to regain control of its digital infrastructure. The duration of these disruptions remains uncertain, raising concerns about the long-term impact on Stryker’s business continuity.
Supply Chain Vulnerabilities and Healthcare System Concerns
Beyond Stryker’s internal operations, the cyberattack has ignited significant concerns regarding its potential impact on the broader healthcare supply chain. As a major supplier of critical medical devices and surgical supplies, disruptions to Stryker’s services could have life-threatening consequences for patients.
A healthcare professional from a prominent U.S. university medical system, speaking on condition of anonymity, revealed their inability to order essential surgical supplies normally sourced through Stryker. "This is a real-world supply chain attack," the expert stated, emphasizing that "Pretty much every hospital in the U.S. that performs surgeries uses their supplies." This sentiment underscores the interconnectedness of the healthcare ecosystem and the cascading effects of a cyberattack on a critical supplier.
The American Hospital Association (AHA) has acknowledged the reports of the cyberattack and is actively monitoring the situation. John Riggi, national advisor for the AHA, stated that while they are not currently aware of any direct impacts or disruptions to U.S. hospitals, this could change if the attack’s duration extends. The AHA is coordinating with hospitals and federal agencies to assess the threat and its potential ramifications for hospital operations.
Further underscoring the immediate impact, a memo from the state of Maryland’s Institute for Emergency Medical Services Systems indicated that Stryker had reported a "global network disruption" affecting some of its computer systems. In response to the attack, some hospitals have proactively disconnected from Stryker’s online services, including LifeNet. LifeNet is a crucial platform that enables paramedics to transmit EKGs to emergency physicians, facilitating expedited treatment for heart attack patients. The memo advised that in the absence of ECG transmission capabilities, hospitals should initiate radio consultations and describe ECG findings. This demonstrates how a cyberattack on a medical technology company can directly impede emergency medical care protocols.
Analysis of Implications
The Handala attack on Stryker represents a significant escalation in the cyber threat landscape, particularly concerning critical infrastructure and the healthcare sector. The group’s alleged use of a legitimate IT management tool like Microsoft Intune to execute a mass data-wipe operation highlights the evolving tactics of sophisticated threat actors. This approach bypasses traditional perimeter defenses and strikes at the heart of an organization’s managed endpoints.
The attack also underscores the growing trend of cyber operations being intertwined with geopolitical tensions. The stated motivation for the attack, directly linked to a missile strike with U.S. involvement, suggests that cyber capabilities are increasingly being employed as a tool of statecraft and retaliation. This blurs the lines between state-sponsored espionage, sabotage, and hacktivism.
The potential for cascading supply chain disruptions within the healthcare industry is a paramount concern. Stryker’s role as a provider of essential medical equipment means that prolonged downtime could lead to shortages of critical supplies, impacting patient care and potentially leading to adverse health outcomes. The proactive measures taken by some hospitals to disconnect from Stryker’s services, while necessary for immediate security, also illustrate the operational challenges posed by such disruptions.
The incident serves as a stark reminder of the vulnerabilities inherent in our increasingly digitized world. For organizations like Stryker, robust cybersecurity defenses are not merely a technical requirement but a fundamental component of patient safety and public health. The reliance on cloud-based management tools, while offering efficiency, also introduces new attack vectors that must be meticulously secured and monitored.
The ongoing investigation into the attack and its full impact is crucial. As the situation develops, it will be important to monitor the extent of data loss, the timeline for recovery, and any potential long-term consequences for Stryker and the global healthcare ecosystem it serves. The international community and cybersecurity firms will undoubtedly be scrutinizing the actions of Handala and its alleged state sponsors, seeking to understand the motivations, capabilities, and future intentions of these threat actors. This incident underscores the persistent and evolving nature of cyber threats and the critical need for continuous vigilance and adaptation in cybersecurity strategies.
Timeline of Events
- February 28, 2026: A missile strike hits an Iranian school, killing at least 175 people, predominantly children. The New York Times later reports, citing an investigation, that the United States is responsible for this strike.
- Late 2023: The hacktivist group Handala surfaces, with cybersecurity firm Palo Alto Networks linking it to Iran’s Ministry of Intelligence and Security (MOIS).
- Prior to March 12, 2026: Handala claims responsibility for attacks against fuel systems in Jordan and an Israeli energy exploration company.
- March 11, 2026 (Morning): News reports emerge from Ireland detailing Stryker workers being sent home due to a cyberattack. A voicemail at Stryker’s U.S. headquarters mentions a "building emergency." The Irish Examiner reports widespread network outages and device wiping.
- March 11, 2026 (Afternoon): A manifesto posted by Handala on Telegram claims responsibility for a data-wiping attack impacting Stryker in 79 countries, affecting over 200,000 systems. The group links the attack to the February 28th missile strike.
- March 11, 2026 (Update): The American Hospital Association (AHA) confirms awareness of the cyberattack and is assessing potential impacts.
- March 11, 2026 (Update): A memo from Maryland’s Institute for Emergency Medical Services Systems indicates Stryker reported a "global network disruption" and that some hospitals have disconnected from Stryker’s online services, including LifeNet.
- March 12, 2026 (Morning): Further reporting details the technical aspects of the attack, suggesting the use of Microsoft Intune for remote wiping. Discussions on social media platforms indicate Stryker employees were advised to uninstall Intune.
This developing story continues to be monitored for further updates on the impact and recovery efforts.