TeamPCP Targets Iran with Data-Wiping Worm, Exploits Cloud Vulnerabilities and Supply Chains
A financially motivated cybercrime group known as TeamPCP has escalated its operations by unleashing a sophisticated worm designed to inflict data destruction within Iran. This campaign, which materialized over the past weekend, leverages the group’s established tactics of exploiting poorly secured cloud services and targeting critical software supply chains. The worm specifically targets systems configured with Iran’s time zone or Farsi as the default language, aiming to wipe data and potentially extort victims.
TeamPCP, a relatively new but aggressive actor in the cyber threat landscape, has demonstrated a pattern of industrializing existing vulnerabilities and misconfigurations into a potent cloud-native exploitation platform. Their modus operandi involves compromising corporate cloud environments through self-propagating worms that exploit weaknesses in exposed Docker APIs, Kubernetes clusters, and Redis servers, as well as the React2Shell vulnerability. Once inside a victim’s network, TeamPCP attempts lateral movement to siphon authentication credentials, which they then use for extortion, often communicated via Telegram.
The Rise of TeamPCP: A Cloud-Native Threat Actor
Security researchers have been tracking TeamPCP’s activities, with initial profiles emerging in January. A report by the security firm Flare highlighted that the group’s strength lies not in novel exploits but in the large-scale automation and integration of well-known attack techniques. "TeamPCP’s strength does not come from novel exploits or original malware, but from the large-scale automation and integration of well-known attack techniques," wrote Assaf Morag of Flare. "The group industrializes existing vulnerabilities, misconfigurations, and recycled tooling into a cloud-native exploitation platform that turns exposed infrastructure into a self-propagating criminal ecosystem."
Flare’s analysis indicated that TeamPCP predominantly targets cloud infrastructure over end-user devices, with a significant majority of compromised servers hosted on Azure (61%) and AWS (36%), accounting for 97% of their targets. This focus on cloud infrastructure underscores the group’s understanding of modern IT environments and their inherent security challenges. Their strategy of weaponizing exposed control planes rather than relying on endpoint exploitation allows for a broader and more impactful reach within organizations.
A String of Supply Chain Attacks: Trivy and KICS Compromised
TeamPCP’s operational sophistication was further evidenced by a series of supply chain attacks that have targeted popular software tools. On March 19th, the group executed a significant attack against Trivy, a vulnerability scanner developed by Aqua Security. Malicious code was injected into official releases of Trivy available on GitHub Actions, a platform used for automating software development workflows.
Aqua Security confirmed the compromise and stated that the harmful files had been subsequently removed. However, security firm Wiz noted that the attackers managed to publish malicious versions capable of stealing sensitive information, including SSH keys, cloud credentials, Kubernetes tokens, and cryptocurrency wallets from users who downloaded the compromised versions. This incident highlighted the critical vulnerabilities present even in widely trusted security tools and the potential for attackers to leverage them for widespread compromise.
The implications of such supply chain attacks are far-reaching. A compromise of a widely used tool like Trivy can have a cascading effect, potentially impacting thousands of organizations that rely on it for security assessments. The trust placed in these software providers makes them prime targets for attackers seeking to gain a broad foothold.
Escalation: The Data-Wiping Worm and Iranian Targets
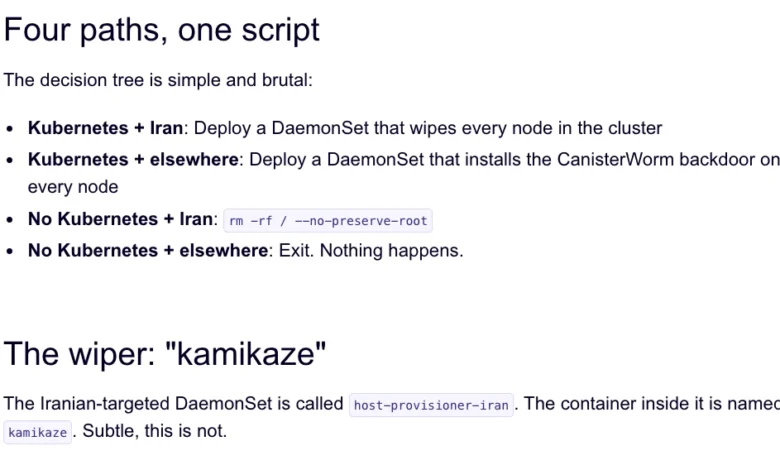
The same technical infrastructure that TeamPCP utilized in the Trivy attack was later leveraged to deploy a new malicious payload. This payload, identified as a data-wiping worm, was designed to execute its destructive function if it detected that a system’s configuration matched Iran’s time zone or had Farsi set as the default language.
Charlie Eriksen, a security researcher at Aikido, detailed the campaign in a blog post published on Sunday. According to Eriksen, if the wiper component identifies a victim within Iran and has access to a Kubernetes cluster, it will proceed to destroy data across all nodes within that cluster. "If it doesn’t it will just wipe the local machine," Eriksen stated.
This targeted approach suggests a potential geopolitical motivation or a deliberate attempt to sow chaos and disruption within Iran, possibly in connection with ongoing geopolitical tensions. The choice to target systems based on language and time zone is a precise method for singling out a specific national infrastructure.
CanisterWorm: The Infrastructure Behind the Attacks
Aikido has dubbed TeamPCP’s operational infrastructure "CanisterWorm." This unique moniker stems from the group’s use of an Internet Computer Protocol (ICP) canister to orchestrate their campaigns. ICP canisters are tamperproof, blockchain-based smart contracts that combine code and data. Their distributed architecture and ability to serve web content directly make them highly resistant to takedown attempts, as they remain accessible as long as their operators continue to pay the necessary virtual currency fees. This reliance on decentralized technology provides TeamPCP with a resilient command and control infrastructure.

Boasting and Bragging: A Telegram Confession
The individuals behind TeamPCP have reportedly been boasting about their exploits and the extent of their access in a Telegram group. They claim to have used their worm to exfiltrate vast amounts of sensitive data from major corporations, including a large multinational pharmaceutical firm. This public display of success, while potentially aimed at inflating their reputation within underground communities, also provides valuable insights into their capabilities and aspirations.
"When they compromised Aqua a second time, they took a lot of GitHub accounts and started spamming these with junk messages," Eriksen noted. "It was almost like they were just showing off how much access they had. Clearly, they have an entire stash of these credentials, and what we’ve seen so far is probably a small sample of what they have."
GitHub as a Weaponization Platform: The Spammed Commits
The practice of spamming compromised GitHub accounts with junk messages is not merely a show of force but also a strategic tactic. Security experts suggest that this could be a method for TeamPCP to artificially inflate the visibility of their malicious code packages within GitHub search results. Attackers have been observed pushing meaningless commits to their repositories or utilizing services that sell GitHub "stars" and "likes" to keep malicious packages prominently displayed.
This trend is further detailed in a recent newsletter by Risky Business reporter Catalin Cimpanu, titled "GitHub is Starting to Have a Real Malware Problem." Cimpanu’s analysis documents an alarming increase in supply chain attacks since 2024, underscoring the growing challenge of identifying and mitigating malicious content on platforms designed for code sharing and collaboration.
A Pattern of Exploitation: Recurring Trivy Vulnerabilities
The weekend’s outbreak involving Trivy is not an isolated incident. It marks the second major supply chain attack targeting the vulnerability scanner in as many months. In late February, Trivy was also compromised as part of an automated threat known as HackerBot-Claw. This earlier attack mass-exploited misconfigured workflows in GitHub Actions to steal authentication tokens, demonstrating a recurring vulnerability in how these automation pipelines are secured.
It appears that TeamPCP may have leveraged the access gained from the initial compromise of Aqua Security to perpetrate the more recent attack. However, the actual success of the data-wiping payload remains uncertain. Eriksen indicated that the malicious code was active for a limited period over the weekend, and the attackers have been rapidly modifying and updating their payload.
"They’ve been taking [the malicious code] up and down, rapidly changing it adding new features," Eriksen said. When not serving malware downloads, the malicious canister was reportedly redirecting visitors to a Rick Astley "Rick Roll" video on YouTube, adding an element of unpredictability and a potential "chaotic evil" persona to their operations. "It’s a little all over the place, and there’s a chance this whole Iran thing is just their way of getting attention," Eriksen speculated. "I feel like these people are really playing this Chaotic Evil role here."
Broader Implications and the Need for Enhanced Platform Security
The increasing frequency and sophistication of supply chain attacks are a growing concern for the cybersecurity community. As threat actors become more adept at exploiting these vulnerabilities, the need for robust security measures at all levels of the software development lifecycle becomes paramount.
"While security firms appear to be doing a good job spotting this, we’re also gonna need GitHub’s security team to step up," Cimpanu wrote. "Unfortunately, on a platform designed to copy (fork) a project and create new versions of it (clones), spotting malicious additions to clones of legitimate repos might be quite the engineering problem to fix."
The challenge lies in balancing the open and collaborative nature of platforms like GitHub with the imperative to maintain security. The distributed architecture that makes these platforms so powerful also makes them attractive targets for attackers seeking to leverage them for widespread distribution of malicious code.
Additional Compromise: KICS Vulnerability Scanner Targeted
In an update on March 23rd, Wiz reported that TeamPCP had also compromised the KICS (Keeping Infrastructure as Code Secure) vulnerability scanner developed by Checkmarx. Credential-stealing malware was pushed to the KICS scanner’s GitHub Action, with the compromise occurring between 12:58 and 16:50 UTC on that day. This further underscores TeamPCP’s persistent focus on targeting tools that organizations rely on for security and code integrity.
The ongoing campaign by TeamPCP serves as a stark reminder of the evolving threat landscape and the critical importance of securing cloud environments, scrutinizing software supply chains, and enhancing the security of collaborative development platforms. The group’s ability to leverage a diverse range of attack vectors, from cloud misconfigurations to supply chain compromises, positions them as a significant threat actor requiring continued vigilance and sophisticated defensive strategies.