Microsoft’s April 2026 Security Updates Trigger Critical Restart Loops on Windows Domain Controllers

Microsoft has confirmed a significant and disruptive issue affecting some Windows domain controllers following the deployment of its April 2026 security updates. Organizations utilizing Privileged Access Management (PAM) are particularly vulnerable, with affected servers experiencing critical Local Security Authority Subsystem Service (LSASS) crashes that lead to persistent restart loops. This malfunction prevents essential authentication and directory services from operating, potentially rendering entire domains unavailable and posing a severe threat to business continuity.
The problem specifically impacts non-Global Catalog (non-GC) domain controllers that are configured to process authentication requests early in their startup sequence. This early processing, combined with the presence of PAM, creates a perfect storm for the LSASS process to fail catastrophically after the April 2026 security update, identified by KB5082063, is installed and the server is rebooted. Microsoft acknowledged the issue in a recent update to its release health dashboard, highlighting the cascading effect of these LSASS crashes on domain functionality.
The Scope of the Outage
The current known issue exclusively affects enterprise environments that have implemented Privileged Access Management (PAM) solutions. This is a critical distinction, as it means that typical home or small business users with unmanaged personal devices are unlikely to encounter this specific problem. However, for the organizations that do rely on PAM for enhanced security and granular control over privileged accounts, the impact can be profound.
The affected Windows Server versions include a range of widely deployed operating systems, underscoring the broad potential reach of this vulnerability:
- Windows Server 2025
- Windows Server 2022
- Windows Server 23H2
- Windows Server 2019
- Windows Server 2016
The inclusion of Windows Server 2025 and 23H2, representing the latest iterations of Microsoft’s server operating system, is particularly concerning. It suggests that even organizations leveraging the newest technologies are not immune to these critical update-related disruptions. The widespread adoption of these server versions means that a significant number of businesses could be at risk.

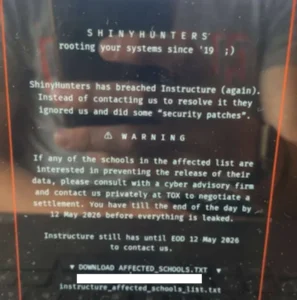
A Recurring Pattern of Update-Related Disruptions
This incident is not an isolated event for Microsoft’s server operating systems. In recent years, the company has grappled with a recurring pattern of security updates inadvertently causing critical issues for Windows Server environments. This recurring nature raises questions about the thoroughness of pre-release testing and the potential for complex interdependencies within the Windows Server ecosystem to be overlooked.
A Chronology of Recent Server Update Incidents:
- June 2025: Microsoft addressed widespread Windows Server authentication problems that emerged following the April 2025 security updates. This incident, similar to the current one, disrupted critical authentication services, necessitating a swift response from the IT community.
- May 2024: Another significant bug was resolved, which had been causing NTLM authentication failures and domain controller reboots after the deployment of the April 2024 Windows Server security updates. This highlights a consistent trend of April updates causing significant issues.
- March 2024: Microsoft was forced to release emergency out-of-band (OOB) updates to rectify critical Windows domain controller crashes that occurred after administrators installed the March 2024 Windows Server security patches. This emergency intervention underscores the severity of the problems encountered.
The repeated occurrence of such critical issues, especially following monthly security patch cycles, creates a significant burden on IT administrators. It necessitates extensive testing of updates before deployment, often leading to delays in patching, which in turn can leave systems vulnerable to actual cyber threats. This creates a challenging dilemma for security professionals: deploy updates quickly to mitigate known vulnerabilities, or delay to avoid introducing new, disruptive problems.
Broader Implications and Analysis
The implications of these recurring update-related failures extend beyond mere inconvenience. For businesses, particularly those with stringent uptime requirements and complex IT infrastructures, a domain controller outage can translate directly into significant financial losses. This includes lost productivity due to inaccessible systems, potential data corruption, reputational damage, and the considerable cost of emergency IT response and remediation.
The reliance on Privileged Access Management (PAM) as a trigger for this particular issue suggests a deep-seated complexity in how these security features interact with core Windows Server services during the boot process. PAM solutions are designed to enhance security by tightly controlling who can access sensitive systems and for how long, often involving sophisticated mechanisms for authentication and authorization. When these mechanisms are disrupted at such a fundamental level as an LSASS crash, the entire authentication infrastructure can collapse.
Current Mitigation and Future Outlook
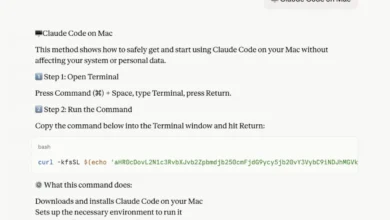
As Microsoft continues to work on a permanent fix for the April 2026 update issue, it has advised IT administrators to proactively contact Microsoft Support for Business. This direct line to Microsoft’s support channels is intended to provide access to mitigation measures that can be applied even after the problematic update has been deployed. The nature of these mitigation measures has not been publicly detailed, but it is likely to involve registry adjustments, service configuration changes, or potentially a phased rollback of certain update components.

The persistent nature of these update-related problems raises important questions about Microsoft’s internal testing and validation processes. While monthly security updates are crucial for maintaining the integrity of the digital landscape against evolving cyber threats, the frequency of disruptive bugs is becoming a significant concern for enterprise IT. Organizations are increasingly looking for greater assurance that security updates will not introduce new, business-crippling vulnerabilities.
Additional Unresolved Issues
Adding to the current turmoil, Microsoft is also investigating a separate, albeit related, issue where the same April 2026 update (KB5082063) is failing to install on some Windows Server 2025 systems. This installation failure further complicates the patching landscape, leaving administrators uncertain about the security posture of their latest server deployments.
Furthermore, in a separate advisory issued on the same Wednesday, Microsoft warned that some Windows Server 2025 devices might unexpectedly prompt users for a BitLocker recovery key after deploying the KB5082063 update. This particular issue, while not directly causing restart loops, introduces another layer of potential disruption and data access challenges for administrators. The overlap of multiple critical issues with a single update highlights a particularly challenging month for Windows Server administrators.
The consistent stream of critical issues associated with Windows Server security updates underscores the immense complexity of managing large-scale enterprise IT environments. While Microsoft’s commitment to security is evident in its regular patch releases, the recurring disruptions serve as a stark reminder of the intricate balance required to maintain both security and operational stability. For IT professionals, the ongoing vigilance, rigorous testing protocols, and proactive engagement with vendor support remain paramount in navigating these challenging update cycles.