The Ghost in the Machine: Unmanaged Non-Human Identities Fueling the Next Wave of Cloud Breaches
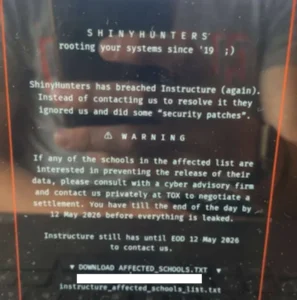
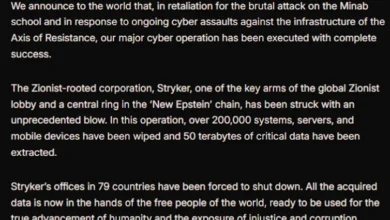
The digital landscape is facing a silent but pervasive threat, with unmonitored and compromised non-human identities emerging as the primary vector for cloud breaches. A stark revelation from 2024 data indicates that a staggering 68% of cloud security incidents were attributed not to sophisticated phishing campaigns or weak user passwords, but to the overlooked credentials of service accounts, API keys, and other automated entities. This trend highlights a critical blind spot in traditional enterprise security strategies, which are increasingly ill-equipped to manage the burgeoning complexity of modern IT environments.
The sheer volume of these automated credentials far outstrips human oversight. For every employee within an organization, there are an estimated 40 to 50 automated identities. These range from service accounts that facilitate communication between applications to API tokens that grant access to sensitive data and AI agent connections that power intelligent workflows. The problem escalates when projects conclude or employees depart, as these highly privileged, often unmonitored, credentials frequently remain active, effectively leaving digital doors unlocked for malicious actors.
"Attackers don’t need to break in. They just pick up the keys you left out," encapsulates the alarming reality of this security vulnerability. This sentiment underscores the ease with which adversaries can exploit these "ghost identities" – digital entities that exist and operate without active human management or scrutiny. The implications are profound, suggesting a fundamental shift in the threat landscape where the perimeter is no longer the primary battleground, but rather the complex web of interconnected services and automated processes within an organization’s cloud infrastructure.
The Escalating Threat of Non-Human Identities
The proliferation of Artificial Intelligence (AI) and the increasing adoption of automated workflows have dramatically accelerated the creation of these non-human identities. AI agents and interconnected systems require persistent access to data and services to function, leading to an exponential growth in API keys, OAuth grants, and specialized service accounts. Security teams are finding it increasingly challenging to maintain visibility and control over this rapidly expanding digital footprint.
A significant concern is the excessive privilege often granted to these automated credentials. Many are configured with administrative-level access that far exceeds their operational necessity. This over-provisioning means that a single compromised token can grant an attacker unfettered lateral movement across an entire cloud environment, enabling them to access, manipulate, or exfiltrate vast amounts of sensitive data. The average dwell time for such intrusions, before detection, is reportedly over 200 days, allowing attackers ample opportunity to achieve their objectives.
Traditional Identity and Access Management (IAM) systems, designed primarily to govern human access to resources, are fundamentally ill-suited to address this emerging threat. They were built in an era where the majority of digital interactions were initiated and managed by people. The current paradigm, however, is increasingly driven by machine-to-machine communication and automated processes, leaving a critical gap in security governance.
A Growing Crisis: Data and Trends
The statistics paint a grim picture of the current state of cloud security related to non-human identities. While the precise methodologies for tracking these breaches can vary, industry reports consistently highlight the significant role of compromised credentials.
- 2024 Cloud Breach Data: As stated, 68% of cloud breaches in 2024 were linked to compromised service accounts and API keys. This figure represents a substantial increase from previous years, indicating a trend that is accelerating.
- Volume of Non-Human Identities: Estimates suggest a ratio of 40-50 non-human identities for every human employee in a typical enterprise. This exponential growth is outpacing the capacity of human security teams to manage.
- Privilege Escalation: A significant percentage of these non-human identities are provisioned with excessive privileges, often at the administrator level, increasing the impact of any compromise.
- Dwell Time: The average time an attacker can remain undetected within a network after exploiting a non-human identity is over 200 days, providing ample time to conduct reconnaissance, move laterally, and achieve malicious goals.
- Financial Impact: While direct figures for breaches specifically attributed to non-human identities are still being aggregated, the overall cost of cloud breaches continues to rise. The IBM Cost of a Data Breach Report 2023 indicated an average cost of $4.45 million per breach, with cloud misconfigurations being a significant contributing factor. The exploitation of unmanaged identities can be a direct pathway to such misconfigurations.
The Evolution of the Threat Landscape
The genesis of this problem can be traced back to the rapid adoption of cloud computing and microservices architectures. As organizations migrated their infrastructure and applications to the cloud, they embraced the agility and scalability offered by these platforms. This often involved the extensive use of APIs and automated services to enable seamless integration and operation.
In the early days of cloud adoption, the focus was primarily on securing human access. IAM solutions were developed to manage user accounts, roles, and permissions. However, the proliferation of cloud-native applications, DevOps practices, and the subsequent integration of AI and machine learning tools introduced a new class of digital entities that operated outside the purview of traditional IAM.
The COVID-19 pandemic further accelerated this trend. The widespread shift to remote work and the increased reliance on digital tools and cloud services meant that organizations had to deploy and integrate systems at an unprecedented pace. This rapid deployment often came at the expense of rigorous security practices, particularly concerning the lifecycle management of automated credentials. Projects were launched, teams were formed and disbanded, and new integrations were built, but the associated service accounts and API keys were often forgotten or left with broad permissions.
![[Webinar] Eliminate Ghost Identities Before They Expose Your Enterprise Data](https://blogger.googleusercontent.com/img/b/R29vZ2xl/AVvXsEi6vJpO9kksCQDpSksNkqDFNUCbXD70dMGYqI6P9S_XPMY5d8BR8PVdrsVQP1ZJO_-nzL6eQShM3Cap9heQ5kAglsPjfxwIcXPSsf_cfgUVnGQ2XzIWVOuo7JhxMjnHYDN6r9KlQ6LqZJisRZkjatnWChuzUkSlXRa1hFseUPq28PZ5gjGR7L2WzTFdZ3fM/s1700-e365/ghost.jpg)
The "Ghost Identities" Phenomenon
The term "Ghost Identities" aptly describes these unmanaged, often forgotten, non-human entities. They exist in the digital ether, performing their intended functions, but without the active oversight that would be applied to a human user. Their invisibility makes them an ideal target for attackers.
- Lack of Visibility: Security teams often lack comprehensive inventories of all active non-human identities, their purposes, and the privileges they possess. This makes it difficult to identify and revoke unnecessary access.
- Stale Credentials: Credentials that are no longer needed but remain active are prime targets. These might be API keys for a deprecated service, service accounts for a project that was shelved, or OAuth grants for an application that has been decommissioned.
- Over-Provisioning of Privileges: As mentioned, many non-human identities are granted broad permissions, such as administrative rights, which they do not require for their specific tasks. This significantly amplifies the potential damage if these credentials are compromised.
- Complex Interdependencies: In modern cloud environments, services and applications are highly interconnected. A compromise in one area can cascade through these dependencies, leading to widespread impact.
The Implications for Enterprise Security
The rise of "Ghost Identities" has profound implications for enterprise security strategies:
- Erosion of Traditional Defenses: Perimeter-based security and even standard endpoint protection are becoming less effective when attackers can gain access through legitimate, but unmonitored, service accounts.
- Increased Attack Surface: The sheer number of these identities dramatically expands the potential attack surface for organizations.
- Sophisticated Lateral Movement: Compromised non-human identities can facilitate swift and stealthy lateral movement across cloud environments, making it difficult for security teams to detect and contain breaches.
- Compliance and Regulatory Risks: The lack of visibility and control over these identities can lead to non-compliance with data protection regulations such as GDPR and CCPA, resulting in significant fines and reputational damage.
- The Need for a New Paradigm: Existing IAM solutions are insufficient. Organizations need new approaches that can provide continuous monitoring, automated discovery, and intelligent management of non-human identities.
Industry Reactions and Expert Opinions
Security professionals and industry analysts have been vocal about the growing concern. Many are calling for a fundamental re-evaluation of how organizations manage identities in the cloud.
"We’ve been so focused on securing the human element that we’ve inadvertently created a vast, unsecured digital underworld," commented a leading cybersecurity analyst. "These machines and automated processes are the new frontier for attackers, and our current security frameworks are lagging far behind."
The sentiment is echoed by cybersecurity vendors who are developing new solutions to address this gap. The focus is shifting towards "Machine Identity Management" (MIM) or "Non-Human Identity Management" (NHIM) solutions, which aim to provide comprehensive visibility, governance, and security for these entities.
While specific company statements directly addressing this article’s premise are not publicly available, the increasing focus on cloud security and identity management by major cybersecurity firms, such as Microsoft, Okta, and Palo Alto Networks, indicates a growing industry recognition of this threat. Their product roadmaps and research publications often highlight the challenges and solutions related to managing a hybrid and multi-cloud identity landscape, implicitly including non-human entities.
Navigating the Path Forward: A Call to Action
The challenge of managing "Ghost Identities" is not insurmountable, but it requires a proactive and strategic approach. Organizations must:
- Inventory and Discover: Implement tools and processes to continuously discover and inventory all non-human identities across their cloud infrastructure.
- Least Privilege Principle: Apply the principle of least privilege rigorously, ensuring that each identity only has the permissions absolutely necessary for its function.
- Automate Management: Leverage automation to manage the lifecycle of these identities, including provisioning, de-provisioning, and regular access reviews.
- Continuous Monitoring: Establish robust monitoring mechanisms to detect anomalous behavior or unauthorized access attempts related to non-human identities.
- Adopt Modern IAM Solutions: Invest in IAM solutions that are specifically designed to manage machine identities and integrate with cloud-native environments.
To provide practical guidance on this critical issue, a forthcoming webinar titled "Ghost in the Machine" aims to equip security teams with the knowledge and strategies to identify and eliminate these hidden threats. The session promises to offer a "working playbook" rather than a product demonstration, empowering attendees to implement actionable steps immediately. The focus will be on securing these non-human identities step-by-step, ensuring that organizations can fortify their cloud environments against this evolving threat vector.
The digital age demands a constant evolution of security practices. As our reliance on automation and AI grows, so too must our vigilance in securing the very mechanisms that power our digital lives. Ignoring the "Ghost Identities" that permeate our cloud infrastructure is no longer an option; it is an invitation to a breach.
This article was originally published by The Hacker News on April 18, 2026, focusing on Artificial Intelligence and Enterprise Security. For more exclusive content, follow us on Google News, Twitter, and LinkedIn.