Mirai Botnet Variants Exploit Vulnerabilities in TBK DVRs and End-of-Life TP-Link Routers
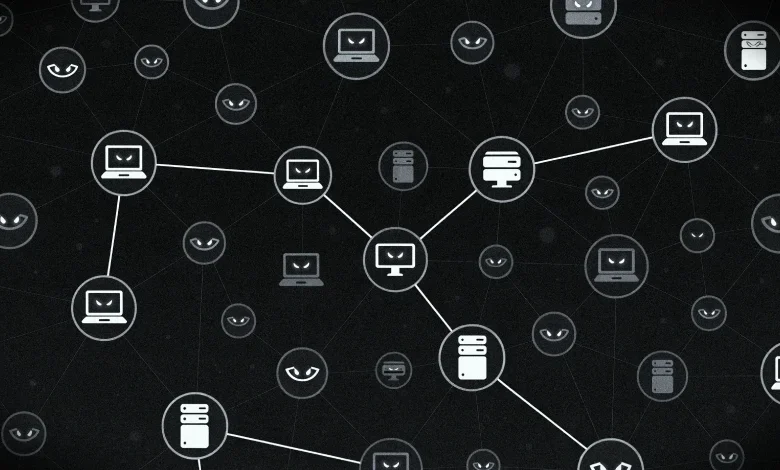
Threat actors are actively exploiting security vulnerabilities in TBK Digital Video Recorders (DVRs) and end-of-life (EoL) TP-Link Wi-Fi routers, deploying sophisticated Mirai botnet variants to compromise these devices. This ongoing campaign, detailed by Fortinet FortiGuard Labs and Palo Alto Networks Unit 42, highlights the persistent risks associated with unsecured Internet of Things (IoT) devices and outdated networking equipment. The attacks leverage known vulnerabilities, turning these typically overlooked devices into powerful tools for large-scale cyber threats, including Distributed Denial-of-Service (DDoS) attacks.
Nexus of Exploitation: TBK DVRs and Nexcorium Botnet
The primary focus of recent activity involves the exploitation of CVE-2024-3721, a medium-severity command injection vulnerability affecting TBK DVR-4104 and DVR-4216 digital video recording devices. This flaw, with a CVSS score of 6.3, allows attackers to execute arbitrary commands on the compromised DVRs. Security researchers have observed the deployment of a Mirai variant, dubbed "Nexcorium," through this exploit.
Vincent Li, a security researcher, emphasized the escalating threat posed by IoT devices: "IoT devices are increasingly prime targets for large-scale attacks due to their widespread use, lack of patching, and often weak security settings. Threat actors continue exploiting known vulnerabilities to gain initial access and deploy malware that can persist, spread, and cause distributed denial-of-service (DDoS) attacks."
The exploitation chain typically begins with the successful leverage of CVE-2024-3721 to gain initial access. Once inside the TBK DVR, attackers drop a downloader script. This script then intelligently identifies the Linux system’s architecture and downloads the appropriate botnet payload. Upon successful execution of the malware, a distinctive message, "nexuscorp has taken control," appears, signaling the device’s assimilation into the botnet.
Fortinet’s analysis reveals that Nexcorium shares a similar architectural blueprint with its Mirai predecessors. Key features include an XOR-encoded configuration table initialization, a watchdog module designed to maintain the botnet’s presence, and a dedicated DDoS attack module. This modular design allows for flexibility and adaptability in launching various forms of cyberattacks.
Furthermore, Nexcorium is not content with merely compromising the initial target. It actively scans the network for other vulnerable devices. Its arsenal includes an exploit for CVE-2017-17215, specifically targeting Huawei HG532 devices, and a comprehensive list of hard-coded usernames and passwords. This allows it to perform brute-force attacks via Telnet, attempting to gain unauthorized access to other hosts within the compromised network.
Upon a successful Telnet login, the malware proceeds to establish persistence by manipulating crontab entries and creating systemd services. This ensures that the botnet remains active even after a device reboot. It then establishes a connection to an external command-and-control (C2) server to await further instructions, which commonly involve launching coordinated DDoS attacks across UDP, TCP, and SMTP protocols. To further evade detection and analysis, once persistence is secured, the malware diligently deletes its original downloaded binary.

Fortinet’s assessment concludes that "The Nexcorium malware displays typical traits of modern IoT-focused botnets, combining vulnerability exploitation, support for multiple architectures, and various persistence methods to sustain long-term access to infected systems. Its use of known exploits, such as CVE-2017-17215, along with extensive brute-force capabilities, underscores its adaptability and efficacy in increasing its infection reach."
End-of-Life TP-Link Routers: A Fertile Ground for Mirai-like Malware
In parallel, Palo Alto Networks Unit 42 has identified exploitation attempts targeting end-of-life TP-Link wireless routers, specifically exploiting CVE-2023-33538. This vulnerability, rated with a higher CVSS score of 8.8, is a critical command injection flaw. While active, automated scans and probes have been observed, the researchers note that these attempts are currently flawed and do not result in successful compromise. However, the underlying vulnerability is confirmed to be exploitable.
"Successful exploitation requires authentication to the router’s web interface," the Unit 42 researchers, Asher Davila, Malav Vyas, and Chris Navarrete, stated. "Although the in-the-wild attacks we observed were flawed and would fail, our analysis confirms the underlying vulnerability is real."
The security flaw associated with CVE-2023-33538 was recognized for its severity and was added to the U.S. Cybersecurity and Infrastructure Security Agency’s (CISA) Known Exploited Vulnerabilities (KEV) catalog in June 2025. This inclusion mandates federal agencies to patch or otherwise remediate the vulnerability to prevent further exploitation.
The malware observed in these TP-Link exploitation attempts bears resemblance to Mirai, with source code exhibiting numerous references to the string "Condi." This variant possesses the capability to self-update with newer versions and can function as a web server, actively seeking to infect other devices that connect to it. This self-propagation mechanism is a hallmark of potent botnets.
The fact that these TP-Link devices are no longer actively supported by the manufacturer exacerbates the risk. Users are strongly advised to replace these EoL routers with newer, supported models and to rigorously enforce the use of strong, unique credentials, moving away from default usernames and passwords.
"For the foreseeable future, the security landscape will continue to be shaped by the persistent risk of default credentials in IoT devices," Unit 42 cautioned. "These credentials can turn a limited, authenticated vulnerability into a critical entry point for determined attackers."
A Persistent Threat: The Evolution of Mirai and its Offshoots
The exploitation of TBK DVRs and TP-Link routers is not an isolated incident but part of a broader, ongoing trend of Mirai botnet variants targeting vulnerable IoT devices. This particular vulnerability, CVE-2024-3721, has a history of being weaponized. Over the past year, it has been leveraged to deploy not only Nexcorium but also a distinct, relatively new botnet known as RondoDox.

In September 2025, cybersecurity firm CloudSEK shed light on a large-scale "loader-as-a-service" botnet infrastructure that was actively distributing RondoDox, Mirai, and Morte payloads. This operation exploited a combination of weak credentials and older vulnerabilities in routers, IoT devices, and enterprise applications, underscoring a multi-faceted approach by threat actors.
The resilience and adaptability of Mirai are key factors contributing to its continued prevalence. First identified in 2016, Mirai gained notoriety for its ability to rapidly infect hundreds of thousands of IoT devices, leveraging default credentials and known vulnerabilities to launch massive DDoS attacks. Its open-source nature has led to the proliferation of numerous derivatives and new variants, each with unique characteristics and exploit methodologies, but sharing the core objective of building large-scale botnets.
Chronology of Exploitation and Discovery
- Ongoing: Threat actors actively scan for and exploit vulnerabilities in TBK DVRs (CVE-2024-3721) and end-of-life TP-Link routers (CVE-2023-33538).
- Past Year: CVE-2024-3721 has been exploited to deploy Mirai variants and the RondoDox botnet.
- September 2025: CloudSEK discloses a loader-as-a-service botnet distributing RondoDox, Mirai, and Morte.
- June 2025: CISA adds CVE-2023-33538 to its KEV catalog, highlighting its active exploitation.
- Recent Findings (Fortinet FortiGuard Labs & Palo Alto Networks Unit 42): Detailed analysis of Nexcorium botnet deployment via TBK DVRs and observed exploitation attempts on TP-Link routers.
Broader Implications and Industry Response
The continuous exploitation of IoT devices by botnets like Mirai and its variants poses a significant threat to cybersecurity. The sheer volume of interconnected devices, coupled with the slow pace of patching and updating, creates a vast attack surface. This not only impacts the individual users whose devices are compromised but also poses risks to critical infrastructure, online services, and the broader internet ecosystem through large-scale DDoS attacks.
The involvement of EoL devices is particularly concerning. Manufacturers often discontinue support and security updates for older products, leaving them permanently vulnerable. This creates a ticking time bomb, where devices that were once secure can become significant security liabilities over time. The CISA KEV catalog serves as a crucial tool in identifying and prioritizing these known threats, but proactive measures by device manufacturers and diligent adoption of security best practices by users are paramount.
Industry experts and researchers consistently advocate for a multi-layered approach to IoT security. This includes:
- Manufacturer Responsibility: Designing devices with security in mind from the outset, providing ongoing security updates, and clearly communicating end-of-life support policies.
- User Education: Emphasizing the importance of changing default credentials, enabling strong Wi-Fi passwords, regularly updating firmware, and being aware of the risks associated with outdated devices.
- Network Segmentation: Isolating IoT devices on separate network segments to limit the lateral movement of malware if a device is compromised.
- Security Solutions: Employing firewalls, intrusion detection systems, and endpoint security solutions that can help detect and mitigate botnet activity.
The findings from Fortinet and Palo Alto Networks serve as a stark reminder that the battle against botnets is an ongoing one. As threat actors become more sophisticated, so too must the efforts to secure the increasingly interconnected world of IoT devices. The continued exploitation of legacy vulnerabilities and the proliferation of powerful botnet variants like Nexcorium underscore the urgent need for vigilance and proactive security measures across the entire digital landscape.