Data Extortion Attack on Canvas Platform Disrupts Education Sector, Threatens Millions of Student Records
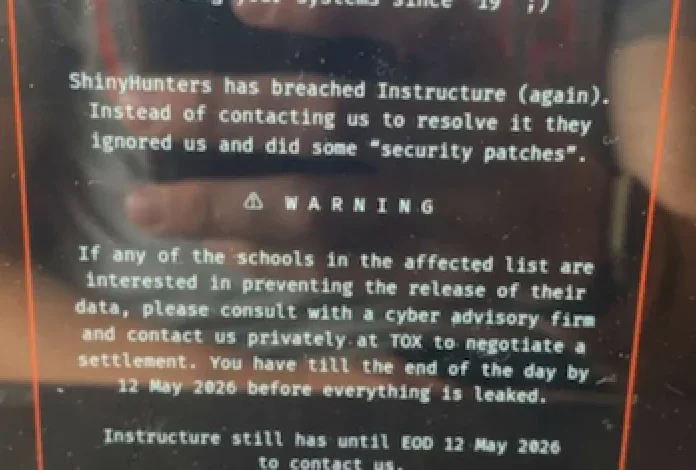
An escalating data extortion attack targeting the widely adopted educational technology platform Canvas has sent shockwaves through the academic landscape, causing widespread disruptions to classes and coursework across the United States. The cybercrime group known as ShinyHunters defaced the service’s login page with a brazen ransom demand, threatening to release sensitive data belonging to an estimated 275 million students and faculty members from nearly 9,000 educational institutions. This incident marks a significant escalation in cyber threats against critical educational infrastructure, raising urgent questions about data security and the resilience of platforms relied upon by millions.
The attack, which unfolded rapidly in early May 2026, saw the usual login portal for Canvas replaced with an alarming message from ShinyHunters. This message not only detailed the breach but also explicitly stated the potential consequences for institutions that failed to comply with their demands. The cybercriminal group claimed to possess a vast trove of information, including billions of private messages exchanged between students and educators, alongside personal identifiers such as names, phone numbers, and email addresses.
Instructure, the parent company of Canvas, confirmed a data breach earlier in the week. In response to the escalating threat and the defacement of its platform, Instructure took the drastic measure of temporarily disabling the Canvas service. This action, while intended to contain the damage and prevent further unauthorized access, resulted in the immediate halt of essential academic functions for thousands of schools, universities, and businesses that depend on Canvas for managing coursework, assignments, and student-teacher communications.
A Timeline of Disruption and Uncertainty
The unfolding events painted a concerning picture of a rapidly evolving cyber crisis:
- Early May 2026: ShinyHunters initially claims responsibility for a data breach affecting Instructure, demanding a ransom and setting a deadline of May 6 for payment. The group threatens to leak data pertaining to tens of millions of students and faculty.
- May 6, 2026: Instructure issues a public statement acknowledging the breach. The company’s investigation indicates that the compromised information includes "certain identifying information of users at affected institutions, such as names, email addresses, and student ID numbers, as well as messages among users." Crucially, Instructure states there is no evidence of more sensitive data, such as passwords, dates of birth, government identifiers, or financial information, being accessed. At this point, Instructure believes the incident is contained and that Canvas is fully operational.
- May 7, 2026 (Mid-day): Students and faculty across numerous educational institutions begin reporting on social media that the Canvas login page has been replaced by a ransom demand from ShinyHunters. In response, Instructure takes Canvas offline, displaying a "scheduled maintenance" message on its status page.
- May 8, 2026: Instructure publishes an incident update, revealing that the hackers exploited an issue related to "Free-for-Teacher" accounts, which was the same vulnerability exploited in a prior incident. The company announces the temporary shutdown of these accounts and confirms that affected organizations were notified on May 6.
- May 11, 2026: Instructure releases a further update, stating that they paid the extortionists in exchange for a promise to destroy the stolen data. The company claims to have received digital confirmation of data destruction and assurance that no Instructure customers would be extorted as a result of the incident.
The Scope of the Threat: Millions of Records at Risk
The scale of the data allegedly compromised by ShinyHunters is staggering. The cybercrime group claims to have exfiltrated data impacting approximately 275 million individuals. This figure encompasses students, faculty, and potentially administrative staff across a vast network of educational institutions. While Instructure’s initial assessment downplayed the sensitivity of the stolen information, the sheer volume raises significant privacy concerns. The inclusion of billions of private messages between users, as claimed by ShinyHunters, could expose a wealth of potentially sensitive communications, personal insights, and academic discussions.
The specific types of data allegedly compromised include:
- Names: Essential personal identifiers.
- Email Addresses: Facilitating further phishing or social engineering attacks.
- Student ID Numbers: Potentially useful for identity theft or unauthorized access to other systems.
- Billions of Private Messages: Containing academic discussions, personal exchanges, and potentially sensitive student-teacher interactions.
Instructure’s May 6 statement sought to reassure users by asserting that passwords, dates of birth, government identifiers, and financial information were not believed to be compromised. However, the protracted nature of the attack and the defacement incident cast a shadow of doubt, prompting ongoing vigilance from affected institutions and individuals.
ShinyHunters: A Persistent Threat Actor
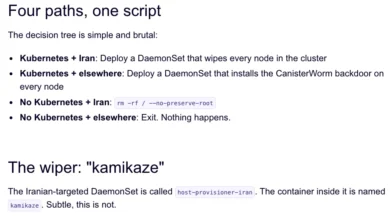
ShinyHunters has established itself as a prolific and formidable cybercriminal organization specializing in data theft and extortion. Their modus operandi typically involves sophisticated social engineering tactics, including voice phishing (vishing) and impersonation of IT personnel, to gain initial access to target networks. Once inside, they are adept at exfiltrating large volumes of data and then leveraging this information for financial gain through ransom demands.
The group’s track record is extensive and alarming. In the months leading up to the Canvas attack, ShinyHunters had been linked to a series of high-profile breaches:
- University of Pennsylvania (September 2025): ShinyHunters released thousands of internal university files, including donor records and confidential memos, through what was determined to be a Canvas/Instructure-mediated access path. This incident, though initially framed as a Penn-specific issue, is now seen by security experts as a precursor and "proof of concept" for the later, larger-scale attacks against Instructure.
- ADT (April 2026): The home security giant reported a data breach affecting 5.5 million customers. ShinyHunters claimed responsibility, stating they compromised an employee’s Okta single sign-on account via a voice phishing attack, granting them access to ADT’s Salesforce instance.
- Other Notable Victims: The group has also taken credit for extortion attacks against major organizations such as Medtronic, Rockstar Games, McGraw Hill, 7-Eleven, and Carnival.
The Impact on Educational Institutions and the Timing
The timing of the Canvas attack could not have been worse for many affected institutions. Early May is a critical period for numerous universities and K-12 districts, often coinciding with the administration of final exams and the submission of end-of-semester assignments. A prolonged outage of Canvas, a platform central to academic operations, threatened to disrupt these crucial academic milestones, potentially impacting student grades, graduation timelines, and overall academic progress.
The extortion message itself highlighted the direct responsibility placed on individual institutions to negotiate their own ransom payments, irrespective of Instructure’s actions. This strategy places an immense burden on already stretched IT departments and administrative bodies, forcing them to make difficult decisions under duress.
Security Experts Raise Concerns and Criticisms
Security professionals have voiced significant concerns regarding Instructure’s handling of the breach and its communication strategy. Dipan Mann, founder and CEO of the security firm Cloudskope, was particularly critical of Instructure’s initial classification of the outage as "scheduled maintenance."
Mann argued that ShinyHunters had demonstrated its ability to breach Instructure’s systems as early as May 1. He pointed to the September 2025 University of Pennsylvania breach as a clear indication of an ongoing attack pattern against Instructure’s environment. Mann characterized the September 2025 incident as a "proof of concept," the May 1 incident as a "production run," and the May 7 re-compromise as a public demonstration that the May 2 "containment" was ineffective.
"Penn was the named victim," Mann wrote in a blog post. "Instructure was the mechanism. The incident was treated as a Penn-specific story by most of the national press and quietly handled by Instructure as a customer-specific matter. That framing was wrong then. It is dramatically more wrong in light of the May 2026 events, which now look like the planned escalation of an attack pattern that ShinyHunters had been working against Instructure’s environment for at least eight months prior."
Charles Carmakal, chief technology officer at Google-owned Mandiant Consulting, corroborated the severity of ShinyHunters’ current activities, stating, "there are multiple concurrent and discrete ShinyHunters intrusion and extortion campaigns happening right now." While declining to comment specifically on the Canvas breach, his statement underscored the widespread and coordinated nature of ShinyHunters’ operations.
The "Free-for-Teacher" Vulnerability and Instructure’s Response
In its May 8 update, Instructure clarified that the breach exploited a vulnerability specifically related to its "Free-for-Teacher" accounts. This admission shed light on the technical vector of the attack and explained why the issue might have persisted despite initial containment efforts. These free accounts, while valuable for educators, may have presented a less secure attack surface.
Instructure’s decision to temporarily shut down these accounts, while disruptive, was presented as a necessary step to address the underlying security flaw. The company emphasized its commitment to resolving the issues associated with these accounts and indicated that affected organizations would be contacted directly by Instructure for validated information, urging users not to rely on unverified third-party lists.
The Extortion Payment and its Aftermath
The most significant development came on May 11, when Instructure announced it had paid the ransom demanded by ShinyHunters. In an update to its incident page, the company stated that the stolen data was returned and that they received digital confirmation of data destruction, including "shred logs." Instructure also reported being informed that no Instructure customers would be extorted as a result of this incident, either publicly or privately.
This decision to pay a ransom is often a controversial one. While it can prevent the immediate public release of stolen data and potentially mitigate further extortion, it also fuels the business model of cybercriminal groups. Security experts and law enforcement agencies often advise against paying ransoms, arguing that it incentivizes future attacks. However, in situations where the potential fallout is catastrophic, organizations may feel compelled to pay to protect their users and their reputation.
The broader implications of this incident for the education sector are profound. It underscores the critical need for robust cybersecurity measures, regular security audits, and comprehensive incident response plans for all educational technology providers. The reliance of modern education on digital platforms makes them prime targets, and the Canvas attack serves as a stark reminder of the persistent and evolving threats in the cyber landscape. As Instructure navigates the aftermath and works to restore full trust, the incident will undoubtedly prompt a re-evaluation of security protocols and vendor management practices across the education industry.