Cybersecurity & Privacy
-

NIST Overhauls Vulnerability Database Operations Amidst Unprecedented Surge in CVE Submissions
The National Institute of Standards and Technology (NIST) has announced a significant shift in its operational strategy for managing cybersecurity…
Read More » -
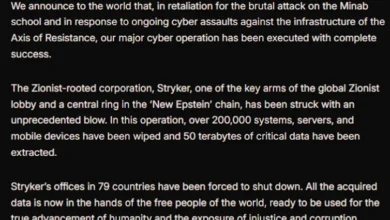
Iran-Backed Hacktivist Group Handala Claims Responsibility for Widespread Cyberattack Against Medical Technology Giant Stryker
A sophisticated cyberattack, attributed to an Iran-linked hacktivist group known as Handala, has crippled the global operations of Stryker, a…
Read More » -

Upcoming Speaking Engagements Detail Bruce Schneier’s Continued Public Engagement on Security and Technology
Security expert Bruce Schneier has announced a series of upcoming speaking engagements, underscoring his ongoing commitment to public discourse on…
Read More » -

CISA Warns of Actively Exploited Apache ActiveMQ Vulnerability, CVE-2026-34197, Posing Significant Risk to Federal Agencies
The U.S. Cybersecurity and Infrastructure Security Agency (CISA) issued a stern warning on Thursday, April 16, 2026, revealing that a…
Read More » -

Google Enhances Android Privacy with New Play Policies and Intensifies Fight Against Malvertising
Google this week unveiled a significant overhaul of its Google Play policies, introducing stringent new measures designed to bolster user…
Read More » -
International Law Enforcement Dismantles Four Major IoT Botnets Responsible for Record-Breaking Cyberattacks
A coordinated international effort spearheaded by the U.S. Justice Department, in collaboration with authorities in Canada and Germany, has successfully…
Read More » -

Defense in Depth: Medieval Style
The ancient Theodosian Land Walls of Constantinople stand as a testament to sophisticated medieval engineering and strategic thinking, offering a…
Read More » -

From Phishing to Fallout: Why MSPs Must Rethink Both Security and Recovery
The cybersecurity landscape is in a constant state of flux, with threat actors demonstrating an alarming capacity to innovate and…
Read More » -

Microsoft Defender Under Siege: Threat Actors Exploit Zero-Day Vulnerabilities for Privilege Escalation
Threat actors are actively exploiting three recently disclosed, zero-day security vulnerabilities in Microsoft Defender, a critical component of endpoint security…
Read More » -
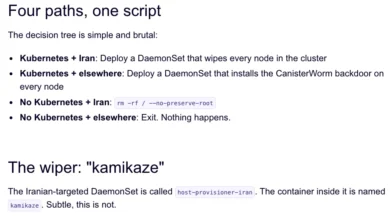
TeamPCP Targets Iran with Data-Wiping Worm, Exploits Cloud Vulnerabilities and Supply Chains
A financially motivated cybercrime group known as TeamPCP has escalated its operations by unleashing a sophisticated worm designed to inflict…
Read More »