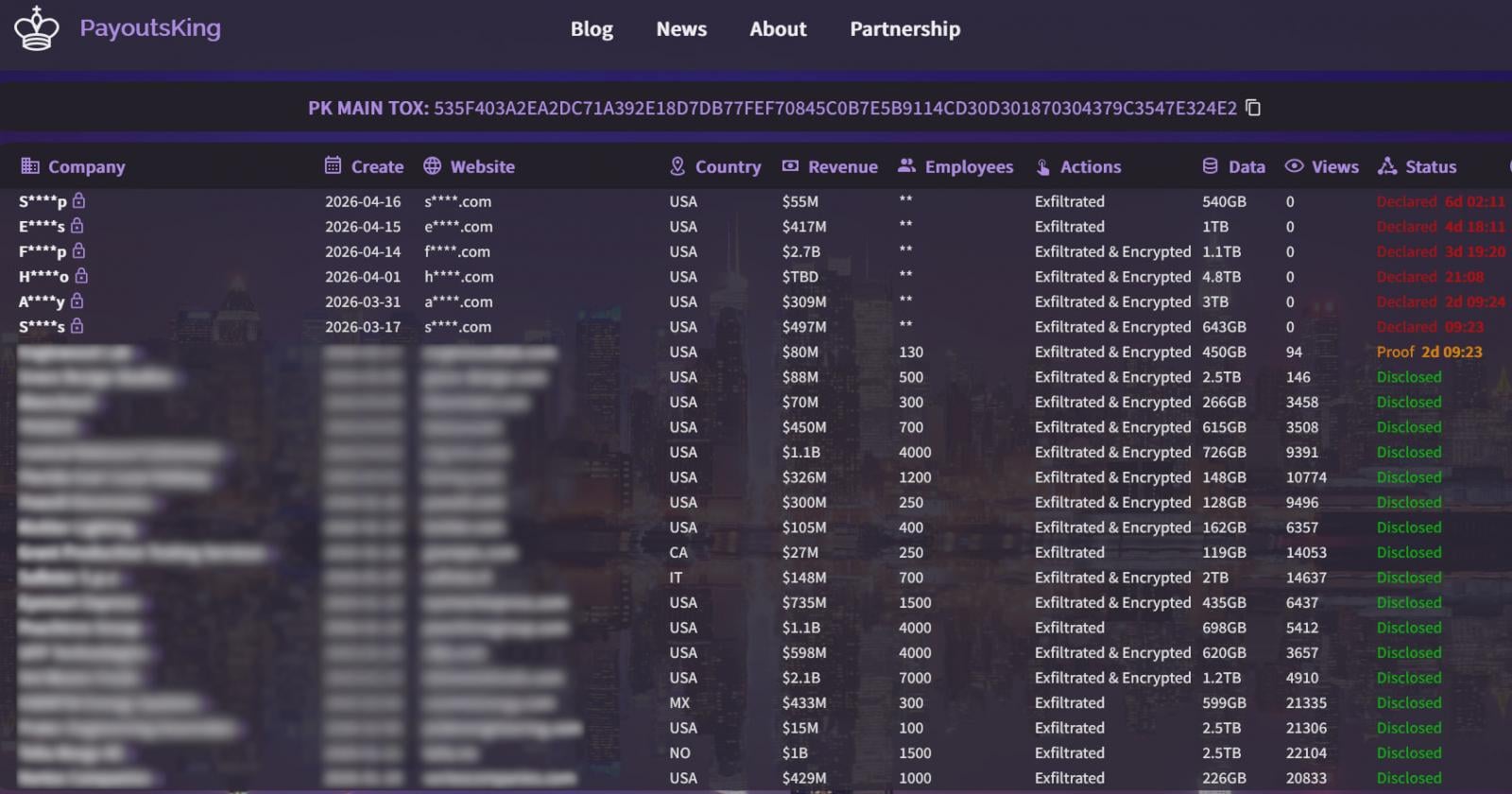
Payouts King Ransomware Evolves: Sophisticated QEMU Virtualization Tactics Evade Advanced Security Defenses

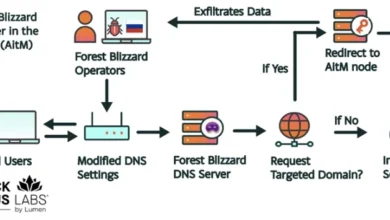
The Payouts King ransomware, a growing threat in the cybersecurity landscape, has adopted a sophisticated new tactic: leveraging the open-source QEMU emulator to create hidden virtual machines (VMs) for reconnaissance, payload deployment, and covert command-and-control (C2) operations. This advanced technique allows the ransomware to operate with a significant degree of stealth, bypassing traditional endpoint security solutions that are often incapable of inspecting the internal workings of these emulated environments. Security researchers at Sophos have detailed two distinct campaigns, STAC4713 and STAC3725, where this QEMU-based evasion strategy has been employed, with the former directly linked to the Payouts King operation and the latter exploiting a critical vulnerability in network security appliances.
The core of this evolving threat lies in the clever repurposing of QEMU, a legitimate and powerful tool for system emulation and virtualization. While intended for benign purposes such as software development, testing, and running legacy operating systems, QEMU’s ability to create isolated environments presents an attractive avenue for malicious actors. By running an operating system, such as Alpine Linux, within a QEMU VM on a compromised host, attackers can execute their tools and malware without triggering the security alerts that would typically flag such activities on the main operating system. This isolation acts as a digital fortress, rendering host-based security software blind to the malicious operations unfolding within the emulated environment.
The Rise of QEMU Abuse in Cybercrime
This is not the first instance of threat actors exploiting QEMU for nefarious purposes. The cybersecurity community has observed its use in various high-profile attacks, highlighting a trend of adapting legitimate technologies for criminal gain. Previously, the 3AM ransomware group, known for its aggressive targeting of organizations, was identified as using QEMU. Similarly, the LoudMiner cryptomining campaign, which aimed to hijack computing resources for illicit cryptocurrency mining, also employed QEMU to conceal its operations. More recently, the ‘CRON#TRAP’ phishing campaign utilized QEMU to inject backdoored Linux VMs into Windows and macOS environments, demonstrating the versatility of this attack vector across different operating systems and attack types. The recurrence of QEMU abuse underscores the constant innovation within the cybercriminal underground and the ongoing challenge for defenders to stay ahead of these adaptive tactics.
Sophos Uncovers Two Payouts King-Associated Campaigns
Cybersecurity firm Sophos has been at the forefront of tracking these QEMU-centric attacks, documenting two significant campaigns that offer crucial insights into the Payouts King ransomware’s operational methods.

Campaign STAC4713: The Genesis of Payouts King’s QEMU Strategy
The campaign designated STAC4713, first observed in November 2025, is directly attributed to the Payouts King ransomware operation and is associated with the GOLD ENCOUNTER threat group. This group has a known history of targeting hypervisors and encryptors, particularly within VMware and ESXi environments, suggesting a focus on disrupting critical infrastructure and data availability.
In STAC4713, the attackers meticulously establish a foothold by creating a scheduled task named "TPMProfiler." This seemingly innocuous task is engineered to launch a hidden QEMU VM with SYSTEM privileges, effectively granting it elevated access on the compromised host. The attackers employ sophisticated disguise tactics, utilizing virtual disk files that are deliberately made to resemble legitimate database or DLL files, further camouflaging their presence. To maintain covert control, they configure port forwarding, establishing a reverse SSH tunnel that provides a clandestine communication channel back to their infrastructure.
The virtual machine itself is a lean and efficient Alpine Linux distribution, specifically version 3.22.0. This minimalist OS serves as a robust platform for a suite of attacker tools, including AdaptixC2 for command and control, Chisel for tunneling, BusyBox for essential Unix utilities, and Rclone for data transfer and synchronization. This carefully curated toolkit allows the attackers to conduct reconnaissance, exfiltrate data, and prepare the system for the final ransomware payload without raising immediate alarms.
Initial access for the STAC4713 campaign was primarily achieved through exposed SonicWall VPNs, a common entry point for many cyberattacks. However, more recent iterations of this campaign have demonstrated an adaptation by exploiting the SolarWinds Web Help Desk vulnerability (CVE-2025-26399), indicating a dynamic approach to gaining initial access.

Following successful compromise, the attackers engage in post-infection activities that are critical for lateral movement and data theft. They leverage the Volume Shadow Service (VSS) utility, specifically vssuirun.exe, to create shadow copies of critical system data. This allows them to access and copy sensitive files, including the NTDS.dit (Active Directory database), SAM (Security Account Manager) hive, and SYSTEM hive, to temporary directories for later exfiltration. This data is crucial for harvesting domain credentials, enabling further network penetration.
More recent observed incidents linked to the GOLD ENCOUNTER threat actor have shown a diversification of initial access vectors. In an attack documented in February, the group exploited an exposed Cisco SSL VPN. In a subsequent incident in March, they resorted to social engineering, impersonating IT staff and tricking employees via Microsoft Teams into downloading and installing QuickAssist, a legitimate remote support tool that was then abused to establish a malicious presence. Sophos researchers noted that in these instances, the attackers utilized the legitimate ADNotificationManager.exe binary to sideload a Havoc C2 payload (vcruntime140_1.dll) before employing Rclone to exfiltrate sensitive data to a remote SFTP server.
Campaign STAC3725: Exploiting Critical Vulnerabilities with QEMU
The second campaign documented by Sophos, tracked as STAC3725, has been active since February 2026 and exhibits a different, yet equally potent, initial access strategy. This campaign specifically targets NetScaler ADC and Gateway instances by exploiting the critical CitrixBleed 2 vulnerability (CVE-2025-5777). This vulnerability, which gained significant notoriety in early 2025, allows attackers to compromise sensitive information from vulnerable devices, often serving as a gateway to deeper network penetration.
Upon gaining access to compromised NetScaler devices, the attackers deploy a ZIP archive containing a malicious executable. This executable is responsible for establishing a persistent presence on the network by installing a service named "AppMgmt." It also creates a new local administrator user, curiously named CtxAppVCOMService, and installs a ScreenConnect client. ScreenConnect, a legitimate remote access tool, is then weaponized by the attackers to establish a persistent session with system privileges, connecting to a remote relay server.

From this established foothold, the attackers drop and extract a QEMU package. This package is configured to run a hidden Alpine Linux VM using a custom disk image file, custom.qcow2. Unlike the STAC4713 campaign where pre-built toolkits were employed, the threat actors in STAC3725 exhibit a higher degree of technical sophistication by manually installing and compiling their tools directly within the QEMU VM. This arsenal includes powerful tools such as Impacket for network protocol manipulation, KrbRelayx and Coercer for Kerberos relay attacks, BloodHound.py for Active Directory reconnaissance, NetExec for remote execution, Kerbrute for Kerberos enumeration, and Metasploit for exploitation and post-exploitation activities.
The observed activities within the STAC3725 campaign encompass extensive credential harvesting, detailed Kerberos username enumeration, in-depth Active Directory reconnaissance, and the staging of exfiltrated data via FTP servers. This methodical approach suggests a focus on gaining comprehensive control over the target network before initiating the final ransomware deployment.
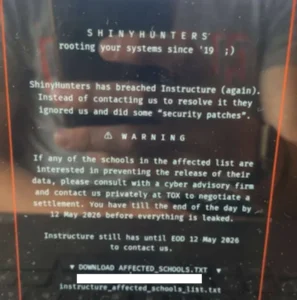
Payouts King’s Affiliations and Operational Modus Operandi
Recent analysis from Zscaler offers further context regarding the Payouts King ransomware. Their reports suggest a strong likelihood of Payouts King being linked to former affiliates of the BlackBasta ransomware group. This connection is inferred from the adoption of similar initial access methods, including spam bombing, sophisticated Microsoft Teams phishing campaigns designed to trick users into downloading malicious files, and the abuse of the legitimate Windows Quick Assist tool for malicious purposes.
The Payouts King ransomware itself is characterized by its robust evasion techniques. It employs heavy obfuscation and anti-analysis mechanisms to thwart detection by security software. Persistence is achieved through the creation of scheduled tasks, a common but effective method. Crucially, it also utilizes low-level system calls to terminate running security tools, further diminishing the chances of detection. The encryption scheme employed by Payouts King utilizes AES-256 in CTR mode, combined with RSA-4096 for key exchange, and features intermittent encryption for larger files to accelerate the encryption process. Victims are typically directed to dark web leak sites via ransom notes, a hallmark of modern ransomware operations aiming for public shaming and increased pressure to pay.
Implications for Cybersecurity Defense
The widespread adoption of QEMU virtualization by sophisticated threat actors like those behind Payouts King presents a significant challenge for cybersecurity professionals. The ability to operate undetected within an emulated environment negates many of the signature-based and behavioral analysis tools commonly deployed at the endpoint.
Key implications include:
- Evolving Detection Strategies: Traditional security solutions need to evolve to detect the presence and activity of QEMU VMs, even when they are intentionally hidden. This may involve monitoring for unusual process behavior, network traffic patterns, and the presence of QEMU binaries in unexpected locations.
- Network Segmentation and Zero Trust: Robust network segmentation and the implementation of Zero Trust architectures become even more critical. By limiting lateral movement, even if an attacker gains a foothold, their ability to spread and deploy ransomware across the network is significantly curtailed.
- Proactive Vulnerability Management: The reliance on exploiting known vulnerabilities, such as those in VPNs and network appliances, underscores the paramount importance of diligent and timely patch management. Organizations must prioritize addressing vulnerabilities that are actively being exploited in the wild.
- Enhanced Monitoring and Forensics: Organizations need to invest in advanced logging, monitoring, and forensic capabilities that can provide deeper visibility into system activities, including the creation and operation of virtualized environments.
Recommendations for Organizations
In light of these evolving threats, Sophos offers several crucial recommendations for organizations to bolster their defenses:
- Monitor for Unauthorized QEMU Installations: Regularly audit systems for the presence of QEMU installations, particularly in environments where they are not expected or sanctioned.
- Investigate Suspicious Scheduled Tasks: Scrutinize scheduled tasks, especially those running with SYSTEM privileges, for unusual names or configurations that might indicate malicious intent.
- Analyze Unusual SSH Port Forwarding: Be vigilant for instances of unexpected SSH port forwarding, which can be a strong indicator of covert C2 channels.
- Detect Outbound SSH Tunnels on Non-Standard Ports: Monitor network traffic for outbound SSH connections on ports other than the standard 22, as these can be used to establish hidden communication pathways.
- Secure VPN and Network Appliances: Ensure that all VPN concentrators, firewalls, and network appliances are patched and configured securely, with regular vulnerability assessments performed.
- Implement Robust Endpoint Detection and Response (EDR): Deploy EDR solutions that can provide deeper visibility into process execution and system calls, potentially flagging the anomalous behavior associated with QEMU usage.
- Conduct Regular Security Awareness Training: Educate employees about social engineering tactics, such as phishing emails and deceptive Teams messages, and the importance of verifying requests for software installations or credential sharing.
The Payouts King ransomware’s sophisticated use of QEMU virtualization marks a significant escalation in the cat-and-mouse game between cybercriminals and defenders. As attackers continue to innovate and leverage legitimate technologies for malicious ends, organizations must remain vigilant, adapt their security strategies, and prioritize proactive defense measures to mitigate the ever-present threat of ransomware. The ongoing evolution of these tactics necessitates a continuous reassessment of security postures and a commitment to staying informed about emerging threats.